Key Takeaways:
- Integrate cybersecurity throughout the entire medical device lifecycle.
- Maintain an up-to-date SBOM to track all software components accurately
- Establish a coordinated vulnerability disclosure process for medical devices to detect and address vulnerabilities.
- Execute a medical device patch management that complies with all MDR security update mandates
- Continuously monitor devices and notify authorities if risks threaten patient safety.
Introduction
IBM reports that the average expense associated with a healthcare data breach reached $10.93 million. In the realm of medical devices, the problem is more advanced: vulnerabilities arise from SOUP components, interconnected hardware,unupdated processes, etc., and can cause unauthorised access, data breaches, device malfunctions, or even directly compromise patient safety. To address these risks, the EU MDR mandates cybersecurity as a mandatory requirement for all medical devices, including SBOM-driven oversight, EU MDR Vulnerability Management, and integration with Post-Market Surveillance (PMS), Corrective and Preventive Actions (CAPA), and vigilance reporting.
Understanding what the EU MDR and auditors expect from the manufacturers, where security risks arise, and how manufacturers can implement vulnerability management to protect their devices against advance cyberthreats.
What Does the EU MDR Expect From Medical Device Manufacturers?
The European Union expects manufacturers to treat cybersecurity not as an IT task but as a core component of clinical safety. The EU MDR requires the medical device manufacturers to ensure that their devices are safe, effective, and fit for their intended purpose throughout their entire lifecycle. Manufacturers should integrate risk management and implement cybersecurity measures across the entire lifecycle of the product, and establish a proactive Post-Market Surveillance (PMS) system to monitor for new vulnerabilities.
They should design devices with built-in security controls and regularly identify, assess, and address cybersecurity risks. The manufacturers are expected to ensure devices are designed and manufactured using the “state of the art” to minimise risks from unauthorised access and cyber threats.
What is state of the art?
The state of the art (SOTA) is the currently acknowledged best practices, clinical guidelines, and technological advancements in medicine. It is the regulatory benchmark for the safety and performance of medical devices in the Clinical Evaluation Report (CER).
Where Do Security Risks in Medical Devices Arise?
Security risks in medical devices can directly compromise patient safety and even their treatment. Unauthorised access or manipulation. can lead to incorrect diagnosis or delayed clinical intervention. Security risks due to:
1. Development phase
Security risks often originate during the development phase through the use of Software of Unknown Provenance (SOUP) and third-party components. If shared software components, such as communication stacks or open-source modules, have a security weakness. Every device using it becomes a target. Therefore, EU MDR mandates “Security by Design,” which means that failure to use secure coding or to maintain a Software Bill of Materials (SBOM) creates an inherent risk before the device even reaches the patient.
2. Connectivity integration
Security risks arise when devices connect to unsecured hospital networks, use unencrypted communication channels, or lack robust authentication. A vulnerability here can lead to unauthorised access, data tampering, or “denial of service,” which can directly disrupt device functionality, delay or interrupt therapy delivery, and compromise patient safety. These risks highlight the importance of healthcare device testing to identify and fix security issues before deployment and throughout the device lifecycle.
3. Risk from the old devices
A significant security risk arises from old devices that were neither designed nor manufactured for today’s security landscape. risks emerge when manufacturers fail to implement proactive Post-Market Surveillance. If a new vulnerability (CVE) is discovered and a manufacturer does not have a rapid patching mechanism. Then the device remains an open window for exploitation throughout its remaining operational life.
Talk to a security expert to find, understand, and fix security risks in your medical devices, while staying compliant and protecting patient safety.
Speak directly with Qualysec’s certified professionals to identify vulnerabilities before attackers do.
How is Vulnerability Management Handled Under EU MDR?
In 2026, EU MDR vulnerability management is no longer a discretionary task but a core mandate to ensure continuous “state of the art” to protect medical devices. When medical devices are connected to the internet and run upgraded software, the attack surface increases, making continuous monitoring essential. Without any approach, vulnerabilities may go unnoticed, which is where vulnerability management becomes necessary. Vulnerability management is a process of identifying, assessing, prioritizing, and remediating security weaknesses in a system. It is a continuous proactive process spread across the entire lifecycle of the medical devices.
Under the EU, vulnerability management is conducted as per MDCG Guidance 2019-26 as:
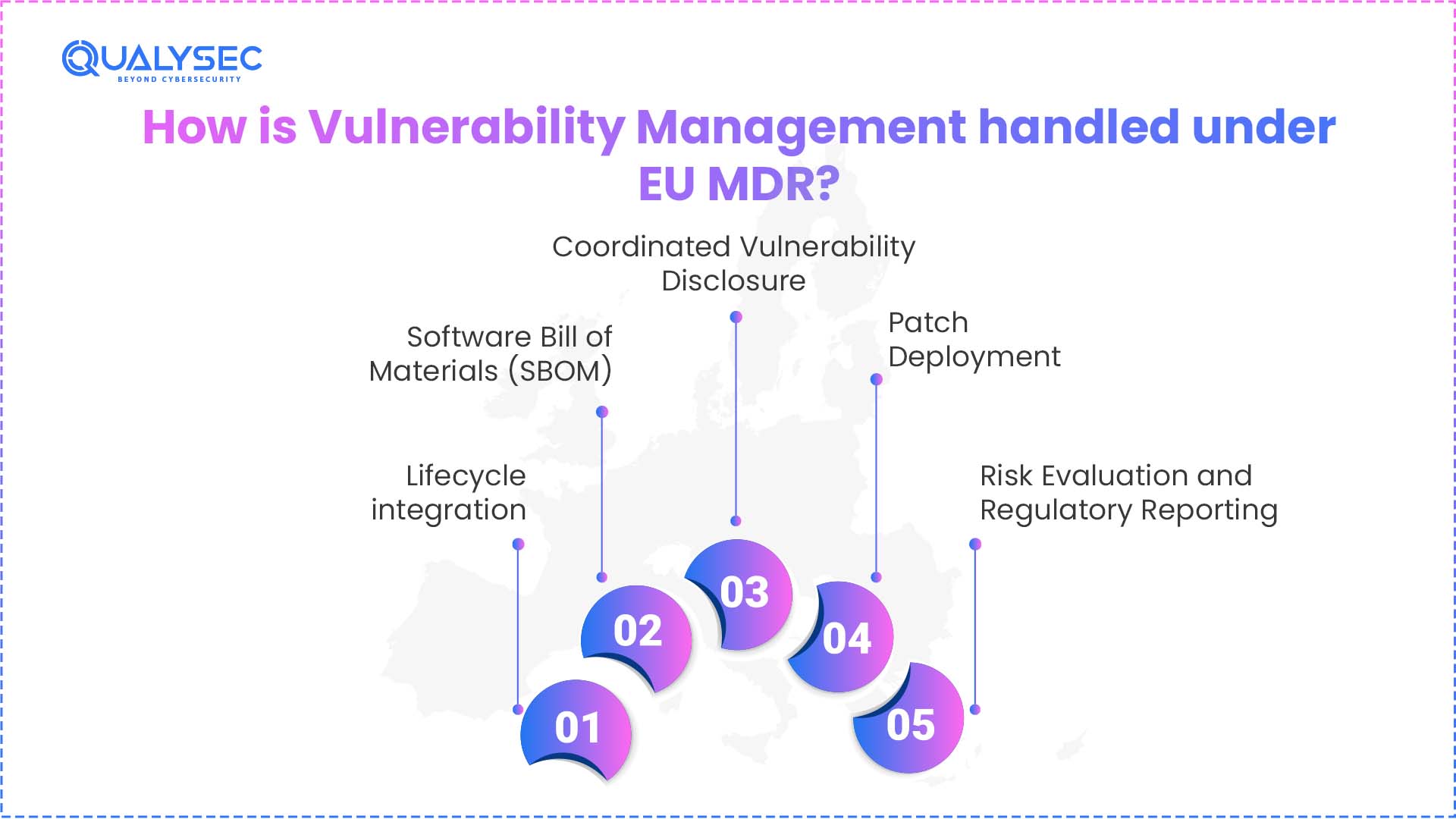
1. Lifecycle integration
Under EU MDR vulnerability management, Manufacturers are required to establish systematic processes for the continuous monitoring of emerging threats. They need to manage vulnerabilities throughout the entire device lifecycle, from design and development to post-market use.
2. Software Bill of Materials (SBOM)
Transparency is the backbone of modern MDR cybersecurity vulnerability handling. Auditors and regulators demand a comprehensive “ingredient list” for all software components, including third-party libraries and legacy code. To provide this, manufacturers need to maintain an SBOM, which gives them near-instant visibility into their software supply chain. This is essential for responding to zero-day threats, finding exactly which devices in the field are susceptible to a newly disclosed vulnerability.
3. Coordinated Vulnerability Disclosure
Manufacturers are required to establish a policy for coordinated vulnerability disclosure of medical devices. This allows independent researchers to report identified flaws. When independent researchers identify vulnerabilities, they can validate and remediate them internally before cyberattackers can exploit them.
4. Patch Deployment
Once security risks are identified and analysed, a medical device patch management plan is executed to remediate vulnerabilities in a controlled and traceable manner. In the patch deployment. This process includes the development and validation of patches, conducting impact and regression testing to guarantee that safety and performance remain intact, and securely deploying updates to devices in the field. The process is handled with care on the basis of proper documentation, traceability, and communication to users.
5. Risk Evaluation and Regulatory Reporting
MDR cybersecurity vulnerability handling is managed through established risk management and vigilance processes, where every identified flaw is identified and tested for its impact on patient safety. Depending on the severity of the incident, manufacturers must report to the relevant National Competent Authority (NCA) within 2 days for serious public health security threats, 10 days for incidents involving serious deterioration of health, and 15 days for other serious incidents.
Pro Tip
Apply security-by-design principles, maintain state-of-the-art alignment, and link vulnerability handling with post-market surveillance in your medical devices!
What Are the Best Practices That Medical Device Manufacturers Should Follow to Stay Compliant?
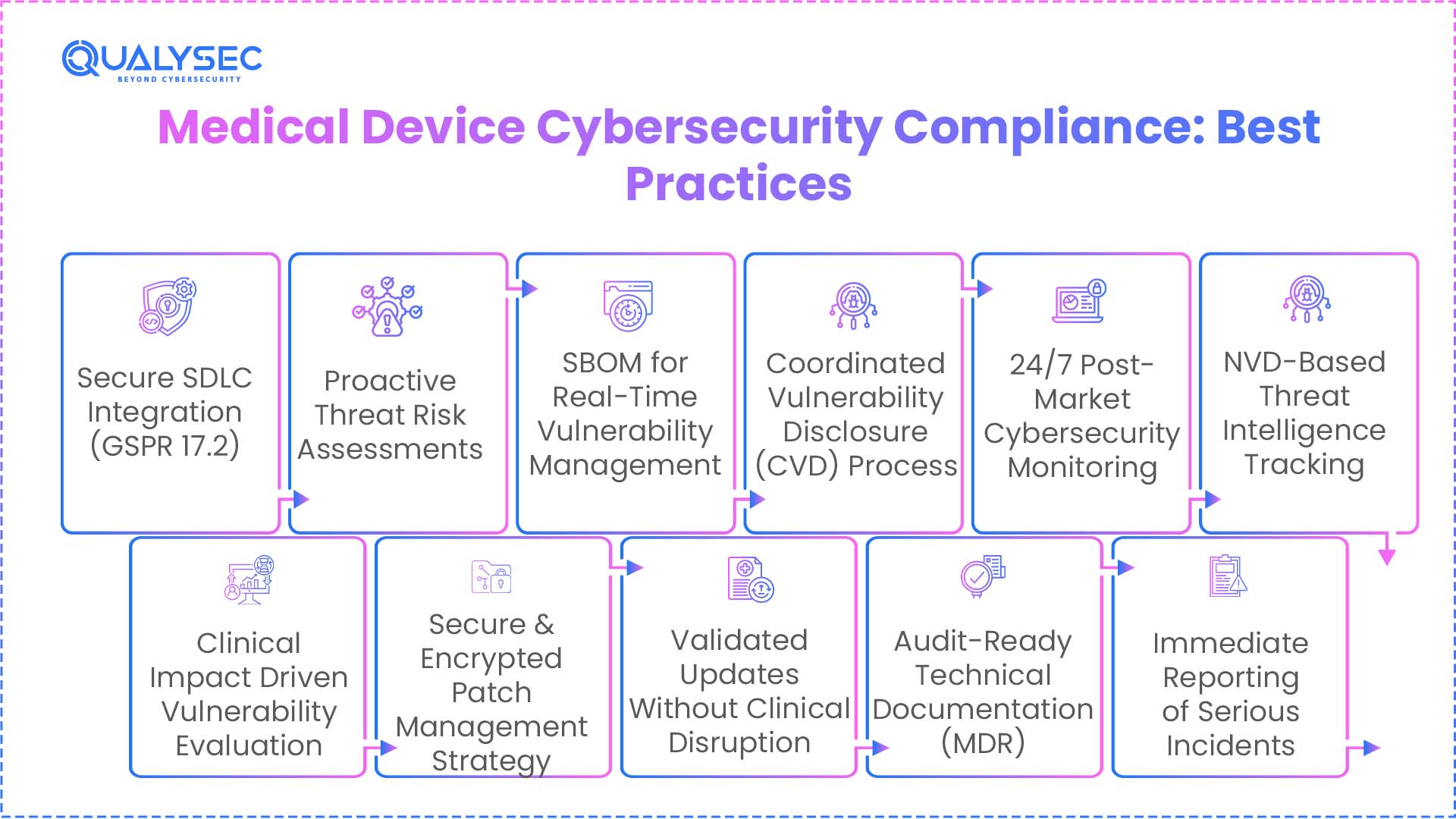
Manufacturers must align their internal processes with the General Safety and Performance Requirements (GSPR). The regulation and associated MDCG guidance directly derive the following best practices to ensure your medical devices stay ahead of cyberattacks:
- Integrate the security requirement (General safety and performance requirement (GSPR17.2) into the first stage of the software development lifecycle (SDLC).
- Perform regular threat assessments to identify potential attack vectors before manufacturing the device.
- Use SBOM to achieve near-instant MDR cybersecurity vulnerability handling when new global CVEs are announced.
- Implement a formal process for coordinated vulnerability disclosure (CVD) of medical devices.
- Set up a 24/7 post-market surveillance loop that monitors the National Vulnerability Database (NVD) for cyber threats that can affect your device
- Evaluate every discovered vulnerability based on its potential impact on clinical safety and patient health.
- Develop a medical device patch management strategy that uses authenticated and encrypted update channels.
- Make sure to validate the security patch to confirm it does not interfere with the device’s medical intended use.
- Keep your Technical File updated with all MDR security update requirements to stay audit-ready.
- Notify Competent Authorities immediately if a vulnerability is classified as a “serious incident”.
How Qualysec Simplifies Your Path to EU MDR Compliance?
Keeping your medical devices safe and compliant these days pretty much demands working with a solid cybersecurity partner. Qualysec steps in with a hands-on approach, making sure security isn’t just an afterthought. They ensure that medical devices remain secure and compliant through a proactive, lifecycle-based approach. This includes integrating security into design (GSPR 17.2, 17.4) and enforcing continuous post-market surveillance (PMS) to identify, triage, and patch software security flaws. Qualysec provides:
- Audit-Ready compliance support: Qualysec aligns your technical documentation and risk management files with EU MDR 2017/745 requirements to ensure that strict Notified Body assessments and CE certification prepare you.
- Security by Design & Threat Modelling: Expert teams perform early-stage threat modelling to identify attack vectors and implement robust security controls during the design phase, satisfying GSPR “state of the art” mandates.
- Medical Device Penetration Testing (VAPT): Qualysec conducts deep-dive, hacker-style testing on firmware, APIs, and wireless protocols (BLE, Wi-Fi) to uncover exploitable vulnerabilities that automated tools often miss.
- SBOM Generation & Vulnerability Analysis: We assist in creating a comprehensive Software Bill of Materials (SBOM) to provide near-instant visibility into third-party libraries (SOUP) and facilitate rapid response to zero-day threats.
- Post-Market Surveillance (PMS) Monitoring: Qualysec establishes a continuous monitoring loop to track new CVEs and validate security patches, ensuring updates fix flaws without compromising the device’s clinical performance.
- Coordinated Vulnerability Disclosure (CVD): Guidance is provided to set up formal channels for vulnerability reporting, allowing you to stay ahead of emerging threats through collaborative engagement with the global security community.
Download a sample pentesting report to identify vulnerabilities and improve your medical device security while staying EU MDR compliant
Get a Free Sample Pentest Report

Conclusion
EU MDR expects you to handle cybersecurity risks for medical devices in a very hands-on way through EU MDR Vulnerability Management. You can’t just spot a vulnerability and leave it at that; you need to assess it. After assessing deal with it, and keep an eye on it as part of your device’s risk management and post-market monitoring. It starts with knowing exactly what’s running in your software, and then moves to rolling out patches quickly when something pops up. You have to document every step and make sure it aligns with safety and performance rules. You have to show you’re actively keeping them under control, all the way from development to when the device is in use.
Is Your Device Ready for the Next Audit? NGSPR 17.2 and 17.4 can be challenging. Let our team help you close the gap. Schedule a 30-Minute Expert Consultation.
Frequently Asked Questions (FAQs)
1. What is vulnerability management under MDR?
Vulnerability management constitutes an ongoing process of identifying, evaluating, and rectifying security vulnerabilities in medical devices. This process guarantees that devices are maintained in a safe, secure, and compliant state throughout their entire lifecycle. It includes their use after they have been marketed.
2. How should medical device manufacturers handle security flaws?
Manufacturers must identify, evaluate, and prioritise security vulnerabilities, and then implement remediation actions. They must also document their actions and assess the implications for safety.
3. Are patch updates required for MDR compliance?
Yes. Under EU MDR (Annex I & post-market obligations), manufacturers must implement timely security patches as part of risk control. Updates should be validated, documented, and deployed without affecting device safety.
4. What is coordinated vulnerability disclosure?
Coordinated vulnerability disclosure (per MDCG 2019-16) requires manufacturers to provide formal channels (e.g., PSIRT, contact points) for reporting vulnerabilities.
5. How do companies track device vulnerabilities?
Companies track vulnerabilities through integrated risk management (ISO 14971), post-market surveillance (PMS), and security monitoring. Manufacturers need to maintain vulnerability logs, CVE tracking, impact assessments, and link findings to CAPA processes





















































































































































































































































































































































































































































































































































































































0 Comments