Cloud Security Risks are increasing worldwide and across the United States as cloud adoption has extended far beyond basic storage and processing use. Today, companies oversee entire application ecosystems on the cloud, assigning tasks across AWS, Azure, Google Cloud, and industry-specific platforms. This significant change has offered speed and scalability, yet it has also increased the attack surface area. 2026 calls for increased awareness of the most frequent cloud security hazards and a deeper understanding of their impact on contemporary environments, as the average cloud-based data breach is expected to reach USD 4.4 million in 2025 (IBM Security Report).
Cloud threats in 2026 go beyond outside attacks. Mature companies can be exposed to internal mistakes, inappropriately set up cloud services, and poor identity habits. Their exposure increases in ways conventional security strategies were never meant to manage as businesses gather more data, adopt multi-cloud systems, expand DevOps processes, and automate infrastructure. Better visibility and actual actions help you to spot, evaluate, and reduce important cloud hazards; thus, this guide highlights the most important cloud vulnerabilities and clarifies how they arise.
If you want deeper visibility into misconfigurations across AWS, Azure, or GCP, Qualysec can run a tailored cloud vulnerability assessment and help you prioritize remediation based on actual risk!
What Cloud Security Risks Will 2026 Bring?
Cloud security threats in 2026 are any flaws, mistakes, exposed services, identification problems, or attack vectors enabling attackers to take over cloud workloads. Technical faults as well as human mistakes cause these risks; hence, cloud settings demand continuous monitoring instead of one-time fixes. One dangerous setup can swiftly turn into a bigger breach than conventional IT systems as cloud services become more connected.
Cloud security faults generally show up in four domains:
- Data exposure is the situation in whereby workloads or storage solutions show sensitive information.
- Identity abuse, whereby illegal access is made possible via stolen credentials or excessive permissions;
- Gaps in configuration brought on by inappropriate resource allocation or hasty infrastructure changes;
- Weak visibility—that is, where businesses just cannot see all cloud resources makes threats more challenging to spot.
The difficulty is that until attackers capitalize on them, these problems are typically invisible. A methodical approach, like ongoing cloud vulnerability assessment, helps reveal flaws before they become violations. Qualysec can map threats and make recommendations for urgent fixes if your team demands more understanding of the kinds of vulnerabilities hidden inside your surroundings.
Top 11 Cloud Security Concerns in 2026
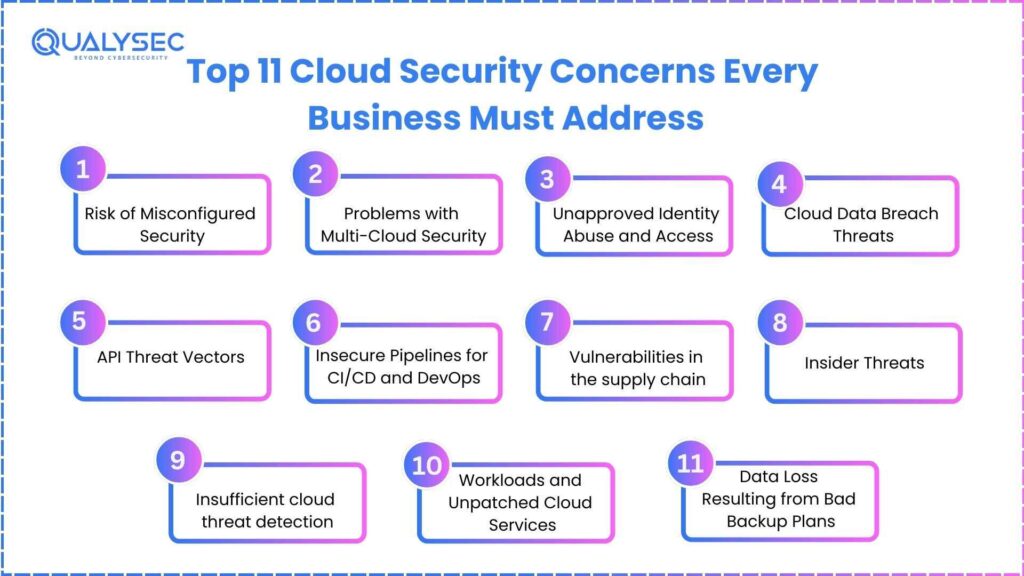
1. Risk of Misconfigured Security
Still, the main cause of cloud breaches worldwide (Gartner Cloud Misconfiguration Study), misconfigurations. These problems develop when identity roles, services, containers, or storage buckets are accidentally left open. Thousands of records may be exposed by even one public S3 bucket or a too lenient IAM policy.
Attackers are continuously searching the internet for assets left available. Automated scanners handle the labor; therefore, they need not specifically aim at your business. One exposed storage bucket or abandoned testing environment opens the gateway. This is rather typical in quick DevOps teams when speed takes precedence over security reviews, therefore causing inadvertent incorrect configuration.
Businesses may lower these hazards by automating configuration checks and applying tight access restrictions. Employing IaC templates with predetermined guardrails helps avoid recurring mistakes. Running frequent cloud vulnerability assessment scans also brings unneeded permissions or dangerous settings to light. Qualysec can assist you in getting a more thorough view of misconfigurations across your cloud platforms by examining your surroundings and presenting a crystal-clear fix-first road map.
2. Problems with Multi-Cloud Security
Two or more cloud services are now used by many companies, both in the United States and all around. Although multi-cloud offers flexibility and corporate continuity, it also increases infrastructure intricacy. Security rules differ across AWS, Azure, and GCP, therefore leads to irregular configurations and monitoring problems.
Among the most often seen multi-cloud security challenges are those produced without adequate documentation, that is, shadow workloads. Teams sometimes set up short-term settings and neglect to delete or safeguard them. Also becoming an issue is fractured identity management since users develop duplicated or unneeded access across clouds. Attacks go for the least cloud in the chain, not the strongest one.
Centralizing identity governance and creating cross-cloud policy baselines will help companies improve multi-cloud arrangements. Consolidated threat detection gives early detection and clarity enhancement. Qualysec can assist in evaluating every cloud platform and point you toward more seamless cloud threat detection approaches if your multi-cloud posture seems too great or erratic.
3. Unapproved Identity Abuse and Access
The fresh cloud perimeter is identity. Attacks steal API keys, compromise service accounts, abuse OAuth tokens, or brute-force identities with limited MFA. Frequently targeting public code repositories, they aim at developers who unintentionally upload credentials during quick development.
Once attackers get access, they use chained IAM policies or overly permissive roles to increase their permissions. Usually unnoticed for weeks, these problems result from the lack of strict monitoring of identity logs. One of the most difficult cloud security threats to solve is identity misuse, as legitimate user activity resembles attacker activity.
Rotating keys, implementing MFA, and eliminating unused roles help you lower identity threats. Early identification of odd access patterns is made possible by the use of identity behavior analytics. Qualysec can look into IAM roles, permissions, and authentication flows to identify missing spaces if your team wants more understanding of identity risks.
4. Cloud Data Breach Threats
Unapproved access, inadvertent exposure, ransomware attacks, or insider behavior define cloud data breaches. The effect worsens as businesses keep enormous amounts of sensitive data customer information, financial records, and company IP. Verizon’s Data Breach Investigations Report notes a rapid increase in cloud data breaches brought on by misconfigurations and lax identity controls.
One important consideration is data sprawl. Tracking where sensitive data resides gets challenging when teams create backups, make snapshots, or duplicate data across several areas. Particularly during multi-cloud security challenges, replication or data transfers, erratic encryption techniques also raise exposure.
Encryption, default logging, safe backup procedures, and more stringent data-sharing restrictions are all necessary for strong cloud data breach prevention. Observing outbound traffic also aids in the identification of exfiltration attempts. Qualysec can lead you through breach-prevention tests and encryption best practices, should your team need assistance developing a data-centric security model.
➡️ Discover How to Secure Your Cloud Data.
5. API Threat Vectors
Though they also provide more entry points, APIs form the core of cloud apps. APIs are appealing targets because of threats, including missing rate limits, obsolete API versions, excessive data exposure, and broken authentication. Automated tools allow attackers to hunt for exposed endpoints and take advantage of faulty input validation or weak authentication.
Developers who put functionality first often create API flaws. Versioning is ignored, security headers are skipped, and sensitive data is returned in replies for convenience. Microservices and serverless systems accelerate the rapid spread of these problems.
Using API gateways, requiring authentication, validating inputs, and conducting frequent penetration tests will let you protect APIs. Qualysec can map your API inventory and look for major cloud security hazards if your API environment is changing and you’re unsure which endpoints represent the most threat.
➡️ Read the Complete Guide: What Is Cloud Application Security?
6. Insecure Pipelines for CI/CD and DevOps
High-speed pushing of code characterizes modern DevOps pipelines, yet security sometimes falls behind. Should pipeline credentials, build scripts, or container registries become public, attackers can directly introduce hostile code into production. Often unnoticed, this kind of compromise only shows up after extensive harm has occurred.
Developers who download unverified packages or containers from public repositories open supply-chain flaws with insecure pipelines. Attacks can slip into your surroundings quietly thanks to broken dependencies.
Organizations can cut down on these risks by keeping secrets safely, scanning pipelines for flaws, and utilizing trusted base images. Internal CI/CD security gates catch problems early. Should you desire an unbiased review of your DevOps pipelines, Qualysec can evaluate weaknesses and assist in securing end-to-end procedures.
7. Vulnerabilities in the supply chain
Modern applications’ reliance on third-party libraries, APIs, and open-source code has raised software supply chain risks. A single compromised dependency can open a backdoor into the cloud ecosystem. To introduce malicious payloads, attackers aim at package managers, container registries, and CI systems.
Because the evil element seems to be real, supply-chain attacks are hard to notice. Unwittingly, developers include damaged code during builds, thereby providing attackers with access in production. These attacks spread swiftly and target several companies simultaneously.
Reducing exposure comes from a software bill of materials (SBOM), dependency scanning, and vendor risk evaluations. Qualysec can examine your tech stack and pinpoint dependencies with high risk if you want assistance going over third-party security vulnerabilities or need direction in creating more secure supply chain policies.
8. Insider Threats
Insider employees, contractors, or vendors can intentionally or accidentally weaken cloud environments. Insiders often inadvertently erase assets, reveal information, or inappropriately set services. Though less frequent, malicious insiders typically do great harm since they already possess real access.
Insider hazards increase when access is not monitored or when users have access privileges. Often forgotten by companies are access revocations following role changes or short-term staff departures.
Reducing insider threats comes about by way of least privilege access, session monitoring, and alerting for unusual activity. Qualysec can assist with audit permission sets and expose hidden hazards if you’re not sure whether your access model exposes you to insider threats.
9. Insufficient cloud threat detection
Many businesses have difficulties spotting cloud threats fast. Built for on-premise settings, traditional SIEM systems frequently overlook cloud-specific trends. To fit in with real events, attackers use lateral movement, identity theft, or API abuse.
Cloud-aware and ongoing threat detection is required. This covers anomaly detection, behavioral analysis, and real-time identity, API, and workload monitoring. Better visibility and faster detection are offered by cloud-native SIEM systems.
Qualysec can help assess logs, fine-tune detections, and advise automated reaction plans appropriate for your architecture if your detection coverage seems inadequate or overwhelming.
➡️ Discover Qualysec’s CSPM Services →
10. Workloads and Unpatched Cloud Services
Regular patching is needed for cloud workloads, virtual machines, containers, serverless functions, and managed services. Because many companies put off patching to prevent downtime, attackers frequently abuse ancient components. Developers reuse outdated photos without updating containers, therefore creating particularly difficult problems.
Scheduled maintenance, image scanning, and automated patching cut exposure. Qualysec can lead you through a prioritized patching method if you need assistance recognizing unpatched elements or verifying your patch-management strategy.
11. Data Loss Resulting from Bad Backup Plans
Especially in ransomware attacks in cloud incidents, backups are the ultimate line of defense. Many companies, however, depend on antiquated or partial backup systems. Recovery gets really hard without geo-redundant backups that are immutable and versioned.
Data loss results from poorly aligned backup frequencies; erratic restore testing causes surprises during emergencies. Though only if set up appropriately, cloud-native backup solutions offer great resilience.
Qualysec can analyze your resilience plan and assist you in improving your recovery posture before a disaster strikes if your backup plan hasn’t been recently tested.
If you’re expanding into multi-cloud and want a clearer picture of gaps across identities, APIs, or workloads, Qualysec can help you build a unified cloud threat detection strategy!
➡️ Identify Your Cloud Risks Today — Request a Security Assessment.
Speak directly with Qualysec’s certified professionals to identify vulnerabilities before attackers do.
How to Identify, Assess, and Mitigate Cloud Security Risks
1. Carry out a cloud vulnerability evaluation.
An analysis of cloud vulnerabilities reveals obsolete services, dangerous identities, exposed ports, and configuration flaws. These evaluations search your whole cloud footprint for flaws by looking at storage, compute, IAM, APIs, containers, and serverless architectures. Regular scanning guarantees early detection of emerging risks instead of their discovery during an event.
For rapidly changing environments, evaluations should run continuously. Automated scanning tools locate improperly set up security groups, overexposed assets, and weak policies. Together with manual validation, they present a whole picture of your cloud state. Qualysec can customize assessments to your unique cloud design if you wish to improve your assessment plan.
2. Improve efforts to prevent breaches of cloud data.
A multi-layered strategy is necessary to avoid data breaches. While logging gives insight into any illicit attempts to view sensitive data, encryption safeguards information during storage and transportation. Observing data flows, especially during replication or migration, aids in spotting odd behavior before it becomes worse.
Curbing permissions for data sharing helps to reduce inadvertent exposure. By checking outgoing traffic for sensitive information, data loss prevention solutions provide yet another level of protection. Qualysec will assist you in establishing an organized data security strategy matching compliance standards.
➡️ See What’s New in 2026 Cloud Security Compliance.
3. Develop better cloud threat detection plans.
Good detection demands constant monitoring throughout several levels: identity, network, workload, and application. While anomaly detection finds strange patterns like unexpected login attempts or API spikes, cloud-native SIEM solutions help to find suspicious events early.
Combining CIEM, CSPM, and SIEM raises general visibility. Before they proliferate, automated answers stop bad actions. Qualysec can help you develop a detection plan customized to your cloud configuration if setting up these tools seems too much.
4. Early resolution of multi-cloud security issues.
Multi-cloud setups require constant policies for identity, encryption, retention, and logging. Blind spots and erratic enforcement result from segmented configurations. Faster anomaly detection and lower operational expenses result from a single dashboard for every cloud.
Configuration drift is minimized by means of standardized policies. Breaches can also be contained by dividing networks across clouds. Qualysec can examine your architecture and offer practical solutions for improved visibility and standardization if your multi-cloud security environment feels challenging to administer.
5. Correct security problems with misconfigurations using automation.
By establishing safe starting settings, automation helps to minimize human error. Infrastructure-as-code scanning guarantees uniform and safe templates. As soon as they show up, auto-remediation bots can correct dangerous setups.
To avoid repeated configuration errors, groups should use predefined secure templates. Qualysec can lead you through top methods fit to your technology stack if you need assistance creating automated guardrails.
6. Protect DevOps Pipelines.
Security has to go left into early development phases. Before they go into production, scanning finds vulnerabilities. Dependency risks are reduced using reliable foundation pictures. Secrets should not be hardcoded in repositories or scripts.
Monitoring pipeline access guarantees that only approved users have build alteration privileges. Qualysec can audit your pipelines and offer enhancements that maintain the security of your DevOps procedures without delaying deployment.
If your DevOps pipelines or dependencies need a security health check, Qualysec can evaluate your CI/CD workflows, secrets handling, and third-party integrations to strengthen your supply-chain security. Get a Free Consultation!
7. Develop a robust recovery and backup strategy.
Strong backup plans include versioned, immutable, geographically redundant backups. Regular restore exercises guarantee backups actually operate. Companies should often examine their retention policies to make certain they meet operational demands and abide by rules.
Automated backups guarantee consistency and lower the possibility of skipped intervals. Qualysec may help you create a recovery strategy matching your workloads if your team doubts the resiliency of your backups.
Best Cloud Security Practices in 2026
- Map assets to bypass shadow resources.
- Follow permissions and track identities painstakingly.
- Wherever you can, automate to lower hand risk.
- Enforce minimum privilege access to reduce blast radius.
- Rotating keys and credentials often
- Keep track of suspicious activity on APIs.
- Turn on thorough recording.
- Regularly assess your cloud security position.
Qualysec can assist you in evaluating your surroundings and lead you through effectively securing every layer if you need help applying these best practices.
Improving Visibility And Risk Coverage With Qualysec’s Expertise
Qualysec assists companies with cloud penetration testing, vulnerability assessments, API testing, and misconfiguration security risks analysis. The team collaborates with customers to spotlight major problems and provide prioritized, practical solutions. Furthermore, assisting in developing cloud threat detection plans, reinforcing identity governance, examining supply chain dependencies, and enhancing backup and recovery systems, they also
Qualysec can conduct a customized evaluation and offer step-by-step development recommendations if you want a more accurate view of your cloud hazards. Their advising philosophy guarantees your cloud posture grows more resilient while remaining congruent with business requirements.
Get a Cloud Pen Testing Report

Conclusion
Cloud adoption will continue to accelerate, and so will the sophistication of cloud-focused attacks. The risks outlined in this guide highlight why organizations must take a proactive approach to securing their environments. Understanding misconfigurations, identity abuse, API gaps, supply-chain vulnerabilities, and multi-cloud challenges helps reduce exposure and improve resilience. When you combine continuous assessment with automated guardrails, strong identity controls, and effective monitoring, your cloud security posture becomes far stronger and better prepared for evolving threats in 2026 and beyond.
If your team needs help evaluating cloud risks or strengthening any part of your cloud ecosystem, Qualysec can support you with tailored assessments and step-by-step remediation advice to keep your environment secure.
If you want a structured roadmap to reduce cloud security risks and improve compliance readiness, Qualysec can support you with detailed assessments and step-by-step remediation guidance. Talk to Our Experts!
FAQs
1. What are the most common cloud security risks in 2026?
Misconfigurations, API vulnerabilities, identity abuse, inadequate threat detection, unsafe pipelines, supply chain problems, and multi-cloud configuration gaps are among the most frequent hazards.
2. Why are misconfigurations such a major cloud security risk?
Misconfigurations are simple to create but difficult to spot manually. Open storage buckets, public services, and excessive permissions are all search targets for attackers; therefore, misconfigured assets are a simple target.
3. How do cloud security risks differ from traditional IT security risks?
Perimeter-based traditional IT systems are those. Driven by identity and API, cloud settings present more dynamic attack surfaces that call for more focus on identity management, logging, and automation.
4. What percentage of data breaches involve multi-cloud environments?
Studies reveal that because of uneven security measures and monitoring gaps, over 60 per cent of breaches target companies running multi-cloud systems.
5. How can organizations effectively assess their cloud security risks?
Regular cloud vulnerability assessments, IAM reviews, configuration scanning, API testing, and cloud threat detection strategies help organizations maintain stronger visibility across cloud assets.














































































































































































































































































































































































































































































































































































































































































































0 Comments