Key Takeaways
- Traditional pentest reports fail because they lack clarity, evidence, and compliance mapping.
- Compliance-ready pentest reports for auditors provide clear proof, traceability, and control mapping.
- Audit-ready pentest report includes scope, methodology, findings, remediation, and retesting.
- Qualysec combines human-led testing, actionable remediation, and formal attestation.
Introduction
Many traditional penetration testing reports fail when they reach auditors. The problem? Traditional reports are built for engineers, not auditors. Under PCI Security Standards Council guidelines, penetration testing is not just about finding vulnerabilities; it must be documented and strongly backed with evidence. With traditional pentesting reports, the organisations may fix vulnerabilities, but still fail in compliance checks. Compliance-ready pentest reports for auditors are essential because they ensure clear traceability, accurate control mapping, and proof of a successful audit. Understanding what a compliance-ready pentesting report is, which standards organisations should follow while drafting penetration testing compliance reporting, and how Qualysec can help.
Why do traditional Pentesting Reports fail auditor inspection?
Traditional penetration reports are written for technical teams, not auditors. Pentesters hunt for holes, whereas the auditors hunt for proof. Traditional pentesting reports fail because:
- Not updated methodology: In a pentesting report, auditors look for “living” methodology, i.e., an approach that is evolving and continuously improving. When a pentesting report uses a generic, five-year-old template, it fails to show accountability for modern cybersecurity attack vectors such as Cloud-native exploitation or CI/CD pipeline vulnerabilities.
- Lack of clarity: Traditional pentesting reports are often prepared by technical teams that are too technical for auditors to interpret. Auditors do not look for technicalities; they look for clarity, context, and relevance. They need to understand the meaning of vulnerability for the organisation, its business impact, risk associated, and potential financial, legal, or reputational consequences.
- Lack of evidence: Most of the technical teams consider penetration reports as a “task,” whereas the auditors treat them as evidence. Many reports provide a list of vulnerabilities but omit to provide the Proof of Concept (PoC). The Auditors aren’t looking at Nmap scans or Burp Suite output, because it is not sufficient. They want evidence that specific controls were tested, validated, and documented properly.
- No framework mapping: Auditors specifically check the report against a set of controls such as NIST 800-53, ISO 27001, or PCI-DSS. When findings are not explicitly mapped to these controls, the report does not have compliance validation. This forces the auditor to do the work for the technical team. They have to then interpret and map technical findings, which ultimately increases the chances of audit failure.
- No proof of retesting: A pentest report with 20 high-risk findings and no follow-up is proof of non-compliance. When reports show a “Point-in-Time” report from six months ago without a “Letter of Remediation,” it significantly weakens audit report acceptance.
What is a compliance-ready penetration testing report?
A compliance-ready penetration testing report is a formal audit evidence document that proves that the security controls of the organisation are functioning as per the required frameworks, such as SOC2, PCI-DSS, or ISO 27001. It maps the vulnerabilities with the compliance controls to show clear evidence of control effectiveness and due diligence.
| Agenda | Compliance-Ready Pentest Report | Traditional Pentest Report |
| Primary Goal | Identify as many vulnerabilities as possible | Shows adherence to regulatory controls and frameworks |
| Approach | Evidence-driven, in line with the compliance framework and established controls | Tool-driven, focuses on identifying vulnerabilities through automated scans and tests |
| Target | Auditors, regulators, executives | Technical and security team |
| Methodology | Usually follows PTES or a proprietary “hacker” approach | Living methodology, explicit, follows NIST 800-115, OWASP, or specific framework requirements. |
| Evidence | Contains screenshots of successful exploits and proof of concept | Contains exhaustive evidence, retest results, and proof that every single required test was performed |
| Target | Auditors, regulators, executives | Technical and security team |
Latest Penetration Testing Report
Which standard should you follow?
In 2026, following a standard means two things basically: the Methodology used to perform the test and the Reporting Framework used to document it. Both elements are crucial to ensure that the audit-ready pentest report is true, correct, and aligned with the compliance requirements. Below are the frameworks that you should follow while drafting a compliance-ready pentesting report:
Testing Methodologies
OWASP WSTG
It is vulnerability-oriented and technical in nature, which provides deep-dive testing procedures for software flaws. OWASP WSTG is best for assessing Web Applications, APIs, and modern SaaS platforms. It is a mandatory reference for PCI DSS application security.
OSSTMM 3
The Open Source Security Testing Methodology Manual is a scientific and fact-based framework. It focused on an operational view of security over vulnerabilities. It is best for testing network infrastructure, physical, and human social engineering security controls.
PTES (Penetration Testing Execution Standard)
It is a 7-phase technical framework that standardises the “how-to” of an engagement. It covers everything from Pre-engagement Interactions to Post-exploitation and Reporting.
Compliance Framework
NIST SP 800-53
It is process-oriented and administrative, focusing on the organisational management of the testing lifecycle. It is considered the best fit for US Federal compliance, such as FISMA, SOC 2 audits, and general enterprise security assessments. This methodology uses a four-phase approach: Planning, Discovery, Attack, and Reporting.
CREST (Council of Registered Ethical Security Testers)
It is the premier global accreditation body that mandates clear documentation, accurate reporting of vulnerabilities, traceability from testing activities, prioritisation of findings, and remediation guidance. It is often required in Asia, the EU, and the UK.
ISO/IEC 27001
It governs technical vulnerability management within the organisation and mandates organisations to identify and address security gaps in a timely manner.
SOC 2 Type II
It mandates penetration testing to satisfy Trust Services Criteria CC4.1 and CC7.1. The pentesting report should map all the technical findings directly to the Security and Availability principles.
PCI DSS 4.0
It mandates annual penetration testing for any entity handling cardholder data in the USA. Include explicit “clean” re-test evidence and risk rating aligned with industry standards, such as CVSS, to prove that you successfully remediated all identified vulnerabilities.
Talk to our Cybersecurity Expert to discuss your specific needs and how we can help your business.
What are the essential components of Compliance-Ready Penetration Testing Reports?
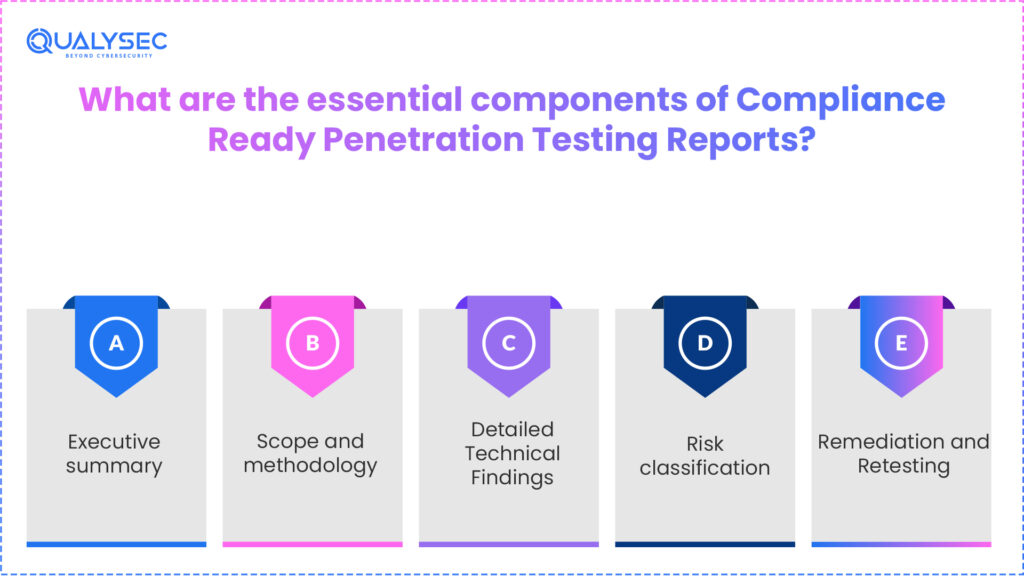
A Compliance-ready pentest report is a document that bridges the gap between technical teams and auditors. To satisfy the auditors, the report must contain:
Executive summary:
It provides risks, vulnerabilities, impact on business, and overall security posture of the organisation in a non-technical manner. An executive summary is essential in any compliance-ready penetration testing report because it helps auditors identify the main issue at a glance.
Scope and methodology:
It defines the systems tested, engagement boundaries, tools used, and frameworks followed during penetration testing.
Detailed Technical Findings:
This is the backbone of the audit-ready pentest report because it provides detailed documentation of risk rating, severity ratings (CVSS), proof of concept, affected assets, and compliance mapping- all supported with evidence.
Risk classification:
Risk classification aligns the vulnerabilities on the basis of risk and compliance requirements.
Remediation and Retesting:
This is the most important and final part of the compliance-ready penetration testing report; it provides clear, actionable steps for IT teams to remediate the vulnerabilities. It also contains Confirmation that testing artifacts were properly removed and, finally, a letter of attestation certifying that the audit-ready pentest report meets all requirements for penetration testing compliance reporting and adheres to regulatory standards.
Pro Tip:
For an audit-ready pentest report, always include a Mapping Table. Explicitly link every technical finding to specific regulatory controls (e.g., PCI DSS 4.0 or SOC 2).
Why Companies Trust Qualysec for Compliance-Ready Reporting
In 2026, traditional, automated reports are instantly flagged by auditors. Qualysec is one of the leading cybersecurity companies in VAPT audit documentation. Over 500 companies and high-growth startups trust Qualysec to deliver their audit-ready pentest report, because it provides:
- Process-Based, Human-Led Testing: While others rely on automated scanners that produce false positives, Qualysec employs a data-driven, manual-first approach. This ensures every vulnerability is verified with a clear Proof of Concept (PoC) to ensure effective penetration testing, compliance reporting and auditor verification.
- Alignment with regulations: Qualysec’s methodologies aren’t just technical; they are aligned with globally recognised standards. Their reports are built upon the testing methodology and compliance framework (as mentioned above).
- Actionable Remediation: Qualysec goes beyond identification and is dedicated. Security experts’ compliance-driven technical team collaborates closely with organisations to fix vulnerabilities. Once their team detects vulnerabilities, they provide unlimited retesting and issue a formal Letter of Attestation (LoA), which serves as the golden ticket for compliance.
- Comprehensive Risk Mapping: Instead of just listing vulnerabilities, Qualysec delivers structured audit-ready pentest reports that map each finding to specific compliance controls.
Conclusion
Creating compliance-ready pentest reports for auditors is about demonstrating due diligence. Align your testing with standards like OWASP and PTES, and ensure a Proof of Concept backs every finding to transform a technical hurdle into a compliance asset. Don’t let a poorly documented pentest be the reason you fail your next audit.
Find Your Perfect Security Partner

Frequently Asked Questions (FAQs)
Q.What do auditors expect in a pentest report?
Auditors want a clear view of what you tested, how you tested it, and proof of any vulnerabilities you found. They also need to understand the business impact of each vulnerability along with the risk level of each issue.
Q.What makes a pentest report compliance-ready?
A compliance-ready report shows the tested scope, method used, and detailed findings supported by evidence. It also shows retesting and remediation measures.
Q.Can a standard pentest report pass compliance audits?
Honestly, most standard pentest reports cannot pass a compliance audit because they often miss evidence, compliance mapping, and proof of fixes. The auditor is here to audit; they need all of these to confirm controls are effective and meet regulatory requirements.














































































































































































































































































































































































































































































































































































































































































































0 Comments