Introduction
Medical equipment utilized in the US is becoming software-enabled, networked and under constant upgrade throughout its life cycle. Since infusion pumps and imaging systems, modern products are now used in complex networked hospital environments and cloud-connected environments. This has changed Medical Device Vulnerability Management programs into a patient safety and regulatory requirement, and not a security capability.
Medical devices as cybersecurity vulnerabilities are not just a theory anymore. Real-world risks can be added to the software deficiencies recently revealed, or third-party libraries that were vulnerable to attack, or even configuration problems post-FDA clearance. In the absence of a proactive vulnerability management program, these problems can remain unnoticed until they disrupt operational processes of clinical facilities, reveal patient information, or prompt regulatory reviews.
The FDA cybersecurity compliance expectations in 2026 are highly focused on the way in which manufacturers deal with vulnerabilities once the device has been deployed. The regulators anticipate that manufacturers should demonstrate ongoing medical device vulnerability scanning, organized medical device risk assessment, on-time vulnerability remediation and disciplined medical device patch management procedures. Vulnerability management is ceasing to be regarded as a security activity that occurs infrequently. It has now become a part of the operations of postmarket safety monitoring and quality systems.
An effective vulnerability management system can assist manufacturers in responding to important questions:
- Do currently revealed vulnerabilities apply to deployed devices?
- Does it have the possibility of affecting patient safety or device efficacy?
- Are remedial measures prompt, confirmed, and recorded?
- Does it have a structured process of vulnerability disclosure?
Those manufacturers who take vulnerability management as an element of a lifecycle discipline are in better positions to mitigate patient risk, appropriately react to security disclosures, and be mature at FDA inspection. This guide outlines the implementation of a scalable vulnerability management program to address medical devices in 2026, based on the regulatory expectations and the actual threat conditions.
What Is a Vulnerability Management Program?
A medical device vulnerability management program is a repeatable process that consists of the identification of medical devices, assessment, prioritization, remediation and follow-up activities of cybersecurity vulnerabilities during the entire life of a device. It goes beyond a single time test and is concerned with keeping the devices safe and effective as new threats, changes in software and dependencies arise.
Vulnerability management in the medical device setting is closely associated with the safety of patients and regulatory controls. It makes sure that medical device cybersecurity vulnerabilities are not just identified, but their practical effect on the clinical use, integrity of data and operational capabilities in a device is also assessed.
On a high level, a medical device vulnerability management program contains:
- Scanning of medical devices to identify known software and configuration vulnerabilities in the firmware, operating systems, applications, and third-party components.
- Risk assessment by medical devices: to identify whether a vulnerability will affect the safety of patients, the performance of medical devices, or clinical processes.
- Medical device vulnerability remediation, patches, configuration modifications, compensatory controls, or usage instructions.
- Medical device patch management operations that are both timely and safe, as well as valid and operational.
- Organized vulnerability disclosure to control the communication with researchers, customers and regulators in case problems are detected.
The vulnerability management should be separated from such related activities:
- Vulnerability scanning reports the potential vulnerability, but not the exploitability or impact on safety.
- Penetration testing confirms the possibility of using vulnerabilities in the real world.
- A vulnerability management program collects these inputs and then forces the decision-making, remediation, and reporting.
Regulatory-wise, FDA compliance on cybersecurity critically relies on the availability of vulnerabilities rather than the management effectiveness of the same. FDA anticipates that the manufacturers demonstrate that the vulnerabilities are being monitored, evaluated for the risk to the patient, and managed by controlled processes in line with the quality system requirements.
Practically, a good vulnerability management program becomes a subset of the overall medical device lifecycle security strategy. It promotes postmarket surveillance, audit preparedness, as well as long term trust in interconnected medical technologies utilized in US healthcare settings.
Discover Healthcare Penetration Testing services for U.S. businesses.
FDA Requirements for Vulnerability Management
The medical device vulnerability management in the United States is directly linked to the FDA compliance expectations of cybersecurity through the lifecycle of the device. Although the FDA does not require one prescribed vulnerability management framework, it is evident that manufacturers should have continued, risk-based processes of detecting and remedying cybersecurity risks once a device is released to the market.
Vulnerability Management as a Postmarket Responsibility
Guidance provided by the FDA indicates clearly that vulnerability management is a postmarket requirement rather than an activity that should be undertaken once during development or premarket submission. After a device has been installed in a clinical setting, the manufacturers are supposed to:
- Follow up on newly reported vulnerabilities of device software, firmware, and third-party elements.
- Evaluate the potential of vulnerabilities that are identified to affect patient safety or device functionality.
- Act in time to mitigate risk by supplying remediation or compensating controls.
This strategy would bring vulnerability management to the level of postmarket surveillance instead of frozen security documentation.
Risk-Based Evaluation Over Severity Scores Alone
FDA does not anticipate manufacturers to be alone in responding to vulnerability severity scores. Rather, risk assessment of medical devices should take into account:
- The way the vulnerability may practically be taken advantage of in a clinical setting.
- The possibility of patient harm, data integrity problems, or loss of necessary functionality as a result of exploitation.
- The controls currently in place can mitigate or remove practical risk.
This focus is the reason why medical device vulnerability remediation can be quite different compared to conventional IT patching. Rapid change is subordinated to patient safety and equipment availability.
Coordinated Vulnerability Disclosure Expectations
FDA is a great advocate of coordinated vulnerability disclosure as part of a developed vulnerability management effort. The manufacturers will be expected to:
- Develop a proper mechanism of getting vulnerability reports from researchers and users.
- Recognize and research documented problems on time.
- Interact with interested parties accordingly in the event of the need to act.
Effective disclosure practices minimize regulatory risk and assist in showing accountability at the inspection.
Reporting and Documentation Requirements
Vulnerability management is also a documentation exercise from the FDA perspective. The manufacturers are expected to demonstrate:
- The detection of vulnerabilities and their subsequent progress.
- Risk decision making and justification.
- What were the remediation actions and the time.
This documentation will assist FDA compliance with cybersecurity when conducting audits, inspection and postmarket reviews.
The general idea of FDA requirements is to remove all the vulnerabilities, but rather demonstrate the availability of a disciplined patient safety-oriented vulnerability management program by manufacturers.
Must Read: Vulnerability Management Process: Step-by-Step Guide for 2026
Core Components of a Medical Device Vulnerability Management Program
A powerful Vulnerability Management Program of Medical Devices is constructed upon repeatable processes which provide equilibrium of security, patient safety, and regulatory requirements. Instead of ad-hoc solutions, the manufacturers must have a program that is structured to operate over the lifecycle of a device.
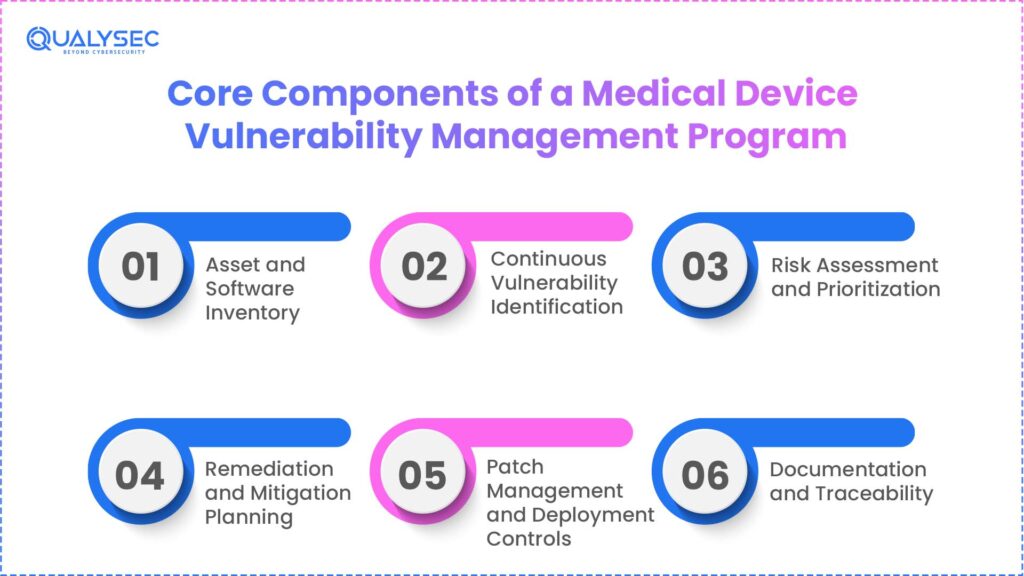
1. Asset and Software Inventory
Visibility is the beginning of effective vulnerability management. Manufacturers are expected to keep a correct inventory of:
- Devices models and versions in the sector.
- Inbuilt operating systems, software and firmware.
- Third-party and open-source libraries are deployed into devices.
It is an inventory that underlies medical device scanning and impact analysis of vulnerabilities.
2. Continuous Vulnerability Identification
The manufacturers should be keen to find the vulnerabilities of their gadgets by:
- Software and supporting infrastructure vulnerability scanning.
- Tracking the public advisories, CVEs, and supplier disclosures.
- Consumption of structured disclosure of vulnerability.
This is aimed at early awareness, rather than reactive discovery once exploited.
3. Risk Assessment and Prioritization
Vulnerabilities do not necessarily warrant identical responses. The risk assessment of medical devices should consider:
- Applicability in actual clinical practice.
- Possible effect on patient safety and other vital device functions.
- Existing mitigations or compensating controls are available.
Such a risk-based strategy is also in line with the expectations of the FDA and eliminates unnecessary and unsafe changes.
4. Remediation and Mitigation Planning
After becoming aware of risk, manufacturers should prepare vulnerability mitigation of the medical devices, which could include:
- Firmware updates or patches, Software patches.
- Setting modifications or access control.
- When patching is not possible immediately, compensating controls should be implemented.
Remediation decisions must be made with consideration of safety, stability and regulatory compliance.
5. Patch Management and Deployment Controls
The management of medical device patches is not like traditional IT systems. Programs must account for:
- Predeployment validation and testing.
- Liaison with health care providers to reduce interruptions.
- There should be strong instructions as to when updates must be installed.
Secure deployment is equivalent to the patch.
6. Documentation and Traceability
Evidence is of great use in FDA cybersecurity compliance. A vulnerability management program ought to articulate:
- Detection procedures and schedules.
- Risk evaluation decisions
- Action and results of remediation.
This traceability assists in audits, inspections and after-sales reviews.
All these elements create a scalable vulnerability management initiative that helps safeguard patients, uphold regulatory requirements and enhance the security of devices in the long term.
Also Read: Medical Device Cybersecurity: The Importance In Healthcare
How to Build a Scalable Vulnerability Management Workflow
The development of a scalable workflow is what transforms a vulnerability management initiative into a sustainable program. In the case of medical devices, the workflow should accommodate the increase in volume of devices, the complexity of the software, and regulatory examination without risking the patients.
Step 1: Establish Clear Ownership and Governance
Accountability begins with the definition of a scalable workflow. Manufacturers need to conspicuously allocate:
- Vulnerability identification and assessment teams.
- Design fixes and validate fixes by engineering teams.
- To assess the effect of safety and compliance, quality and regulatory teams will be involved.
This correspondence ensures that there are no delays or friction during remediation.
Step 2: Standardize Vulnerability Intake
All vulnerability signals are supposed to go through a single intake process, which includes:
- Findings of medical device vulnerability scanning.
- Third-party and supplier disclosures.
- Coordinated vulnerability disclosure programs have reports.
- Findings of internal testing and penetration testing.
With centralized intake, triage and tracking becomes consistent.
Step 3: Apply Risk-Based Triage
Manufacturers should not operate on the principle that every finding is equal, so that they can scale. A formal medical device risk assessment procedure must:
- Categorize vulnerabilities based on exploitability and patient impact.
- Determine response times depending on risk level.
- Justification of deferred or mitigated risks on a document.
This will keep low-risk problems from consuming important resources.
Step 4: Integrate Remediation Into Engineering Cycles
The remediation of vulnerability must be in line with the current development process and release. Effective workflows:
- Tie is embedded into scheduled or software updates.
- Add pre-release regression and safety testing.
- Time coordinate deployment with health care providers.
It is a method that will enable uniform management of medical device patches without interfering with clinical care.
Step 5: Track, Verify, and Close
Close-out discipline is needed in a scalable program. Every vulnerability must be followed up based on:
- Implementation of remediation or mitigation.
- Effectiveness testing to validate.
- Last FDA cybersecurity documentation.
Closed-loop tracking is used to make sure that there is no hidden risk.
Through formalizing these steps, manufacturers can expand vulnerability management between product lines and between device generations and stay in control, keep safe and be regulatory prepared.
Tools and Technology Used in Medical Device Vulnerability Management
An effective vulnerability management program is scalable based on the appropriate combination of both tools and processes. In the case of medical equipment, tooling needs to be sufficiently technical, and regulators need to be satisfied, but not to the extent of overwhelming teams.
Common Tool Categories Used by Manufacturers
The following is a combination of what is usually used by medical device manufacturers:
- Medical device vulnerability scanning tools: These are utilized with the goal of detecting known vulnerabilities in operating systems, firmware components, libraries, as well as network-exposed services. These give permanent visibility without certifying exploitability.
- Asset and SBOM management systems: Assist in tracking software elements, third-party dependencies, and versions between portfolios of devices. This is imperative in influence analysis in instances where new vulnerabilities are revealed.
- Database of threat intelligence and vulnerabilities: Feeds like CVE feeds and industry advisories facilitate the detection of new risks of relevance to deployed equipment in time.
- Ticketing and workflow systems: These are used to keep track of vulnerability remediation, approvals, testing status and closure. These systems offer the traceability needed in compliance with the FDA cybersecurity requirements.
- Testing and validation tools: Controlled penetration testing tools that are used to test the vulnerability to determine whether they are applicable in real-world situations.
Technology Alone Is Not Enough
Although automation is used to identify and monitor risks, risk judgment remains independent. Effective programs involve automation and human inspection to guarantee:
- The effect of patient safety is appropriately evaluated.
- False positives are eliminated.
- Decisions made to remediate can be justified in the course of an audit.
Process maturity is determined by tools, and scale depends on tools.
Suggested Read: FDA 510k Submission: A Step-by-Step Guide to Approval
How Qualysec Supports Medical Device Vulnerability Management
Qualysec helps the manufacturer by complementing those aspects of vulnerability management that cannot be resolved through automation. It involves risk validation and not mere vulnerability discovery.
Risk-Focused Assessments Aligned With FDA Expectations
Qualysec assists organizations in assessing vulnerabilities in the medical device risk assessment, and it looks at:
- Real deployment environment exploitability.
- Effects on the safety, performance, and usage of the device.
- Cybersecurity compliance with FDA expectations and post-market.
The strategy makes manufacturers focus on what is important.
Penetration Testing to Validate Real-World Risk
Qualysec conducts the penetration testing to ascertain the possibility of identified vulnerabilities being exploited in reality. This supports:
- Beyond medical device vulnerability scanning validation.
- Proper remediation prioritization and scoring of risks.
- Greater rationale of regulatory and quality review.
Remediation Validation and Evidence Support
Qualysec helps in;
- Ensuring that remediation is efficient and does not pose additional risks.
- Assisting with paperwork of audits, inspections and in-house checks.
- Correction of the results of remediation with the organized process of vulnerability disclosure.
Qualysec can empower the manufacturers to retain control of vulnerability remediation by providing a risk validation partner that enhances the safety of patients and regulatory preparedness.
Conclusion
By the year 2026, medical device vulnerability management will not be a supporting security feature. The patient safety, regulatory preparedness and long-term product viability are central requirements. Since devices are used for years and will continue to receive software updates, vulnerabilities are not a one-time endeavor; manufacturers need to handle vulnerabilities as a lifecycle concern and not an isolated task.
The best programs do not only involve scanning the vulnerability of medical devices. These are ongoing surveillance, organized risk evaluation of medical devices, rigorous vulnerability reduction and controlled patch management of medical devices. No less significantly, they would spawn obvious evidence that vulnerabilities are detected, evaluated, and resolved according to FDA cybersecurity compliance and harmonized expectations of disclosed vulnerabilities.
Those manufacturers which consider vulnerability management as a living program are in a better position to:
- Minimize patient vulnerability to attackable weaknesses.
- Conquer FDA audits and inspections.
- Remediation: Last-minute remediation during regulatory reviews is an avoidable occurrence.
- Build credibility among partners and medical practitioners.
If you are strengthening or scaling your vulnerability management program for medical devices, Qualysec can help validate real-world risk, confirm remediation effectiveness, and support regulatory-ready documentation. Engage Qualysec to build a vulnerability management approach that stands up to FDA scrutiny and protects patient safety.
FAQs
1. What is the FDA’s expectation for medical device vulnerability management?
The FDA anticipates that manufacturers have a continuous vulnerability management program that recognizes, evaluates and eliminates cybersecurity threats during the lifecycle of the device. This involves ongoing monitoring, making risk-based decisions, and remediation, which is documented in accordance with the FDA cybersecurity compliance requirements.
2. How frequently should vulnerabilities be scanned in medical devices?
The vulnerability scanning of medical devices should be implemented frequently, and every time there is any major change, e.g. software upgrade or introduction of a new integration. Constant or periodic scanning facilitates the timely assessment of risk associated with the medical devices and can be used to identify the emergent threats in time.
3. What tools do manufacturers use for vulnerability management?
A set of automated medical device vulnerability devices, asset discovery services and security surveillance tools is common among manufacturers. These are assisted by manual analysis to rank up risks and direct vulnerability mitigation of medical devices.
4. Is penetration testing part of a vulnerability management program?
Yes, penetration testing is the complement of vulnerability management since it confirms the actuality of the vulnerabilities being exploited in the field. It aids in asserting risk severity outside the scanner findings and enhancing rigorous compliance with the cybersecurity of the FDA.
5. What is CVSS, and how is it used in medical device risk scoring?
CVSS is a standardized scoring scheme which is applied to determine the technical severity of vulnerabilities. CVSS scores are used with patient safety impact, exploitability, and context of the device in medical device risk assessment to rank remediation actions.














































































































































































































































































































































































































































































































































































































































































































0 Comments