In our fast-evolving digital landscape, web applications have seamlessly woven themselves into the fabric of businesses, acting as pivotal gateways for users to access a plethora of services and vital information. However, as the specter of cyber threats continues to loom large, safeguarding these web applications becomes paramount to ensure the sanctity of sensitive data and uphold the unwavering trust of users. This is where the potent shield of web application penetration testing services steps in. In this engaging blog post, we’re embarking on a riveting journey through the realm of web application security, placing the spotlight on the pivotal role of penetration testing in fortifying digital citadels.
Unraveling Web Application Security Testing
Web application penetration testing services, an intricate process, act as the sentinel for your web application’s digital fortress. It involves meticulously scrutinizing the labyrinthine web security software that safeguards your application. The objective? To unveil lurking flaws, vulnerabilities, and loopholes, thereby foiling the nefarious plans of cyber malefactors, whether it’s malware, data breaches, or other menacing cyber threats. This vigilant security testing lays bare all those covert, vulnerable entry points that cybercriminals may seek to exploit, arming you with the means to fortify your digital stronghold.
Delving into the Significance
The realm of web application security testing is more than just a defense mechanism. It’s a calculated move to preemptively identify chinks in your armor. By methodically peering into your web application’s vulnerabilities and frailties, this proactive approach serves as a bulwark against the potential onslaught of malicious individuals or groups. The stakes are high: It’s about preserving the sanctity of user data. More about staving off financial perils, safeguarding reputations, and warding off the ominous shadow of legal consequences.
The Perils of Neglect
Steering clear of web application security testing is akin to leaving your gates wide open to digital marauders. Consider these compelling reasons why web application penetration testing services should never be relegated to the sidelines:
| Benefits of Web Application Security Testing | Description |
|---|---|
| Exposing Flaws and Vulnerabilities | Security testing meticulously uncovers vulnerabilities that malicious hackers may exploit. This comprehensive testing regimen reveals weaknesses such as SQL injections, cross-site scripting (XSS), cross-site request forgery (CSRF), and more. Armed with this knowledge, countermeasures can be deployed to fortify your application’s security. |
| Nurturing Compliance | Different industries are governed by specific security and compliance regulations. Web application security testing acts as your ally in navigating these intricate paths, ensuring compliance and shielding you from legal entanglements and punitive consequences. |
| A Lens into Your Defenses | Beyond identifying vulnerabilities, security testing offers a panoramic vista of your current security landscape. It evaluates the efficacy of your existing security protocols, illuminates areas needing enhancement, and empowers you to fortify your defense lines with precision. |
| Sentinels for Breaches and Anomalies | Consider security testing as a vigilant sentry, diligently uncovering breaches and anomalies lurking within your web applications. By meticulously inspecting application logs, security testers unveil unauthorized access attempts, suspicious activities, and potential breaches. Swift detection enables rapid response, minimizing harm to systems and data. |
| Blueprint for Fortification | Web application security testing transcends mere vulnerability exposure; it’s about devising a strategic security master plan. Armed with insights into vulnerabilities and risks specific to your application, you can allocate resources, prioritize defenses, and thwart imminent threats with a comprehensive strategy. |
Architects of Security
The question of “Who performs web application penetration testing services ?” unfurls a spectrum of choices. It can be orchestrated by internal security mavens, external consultants wielding niche expertise, or even a synergistic fusion of both forces. The pendulum’s swing depends on considerations such as budget, resources, and the inherent complexity of the application in question.
| Who Performs Web Application Security Testing? | Description |
|---|---|
| Internal Security Teams | Organizations can leverage their internal security experts for web application security testing. These teams possess a deep understanding of the organization’s infrastructure and applications, allowing them to tailor the testing approach to the company’s specific needs. |
| External Security Consultants | Employing external security consultants brings a fresh perspective and specialized expertise. These experts offer an objective assessment and can uncover vulnerabilities that might be overlooked by internal teams. |
| Combination of Both | The choice between internal teams and external consultants isn’t necessarily an either-or scenario. Organizations can opt for a hybrid approach, leveraging the strengths of both internal and external resources. This choice hinges on factors such as budget, resources, and the complexity of the application under scrutiny. |
The Foundational Terms
To decode the language of web application penetration testing services, let’s delve into the foundational terms:
- SQL Injection: The strategic insertion of malicious SQL statements into an application’s database query, a potential gateway to unauthorized access or data manipulation.
- Cross-Site Scripting (XSS): A vulnerability empowering attackers to inject malevolent scripts into user-viewed web pages, enabling data pilferage and user impersonation.
- Cross-Site Request Forgery (CSRF): A crafty attack that deceives authenticated users into unknowingly executing malicious actions on a web application they’re logged into.
The Human Touch in Security Testing
The art of manual web application penetration testing services isn’t a mere button-push affair—it’s a meticulous dance of profound assessment. With an eagle eye, skilled security professionals embark on a systematic journey through the application’s code, configurations, and user interactions. This hands-on approach entails a panoply of techniques, from the surgical precision of code review and penetration testing to the discerning scrutiny of security headers, configurations, and the identification of vulnerabilities. The magic lies in their ability to simulate real-world scenarios, unearth vulnerabilities, and craft impregnable defenses.
Important Steps in Web Application Penetration Testing services
The journey through web application penetration testing services is an odyssey comprising distinct stages:
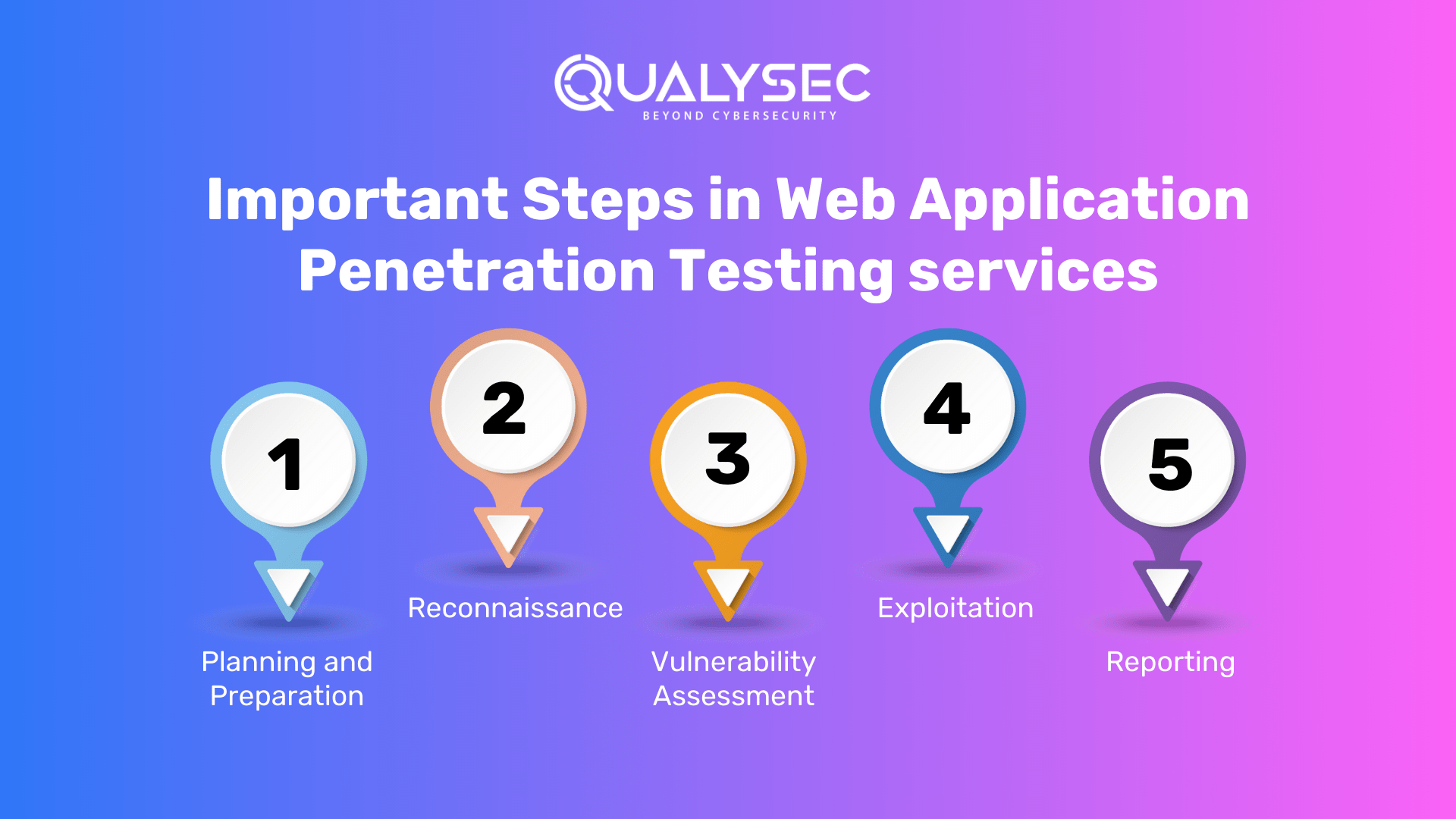
- Planning and Preparation: The voyage begins with outlining the scope, objectives, and requisite resources for the security testing voyage.
- Reconnaissance: This phase involves assembling vital intelligence about the target application’s architecture, vulnerabilities, and potential points of weakness.
- Vulnerability Assessment: Employing techniques like vulnerability scanning, code review, and security configuration analysis, this stage identifies and assesses lurking vulnerabilities.
- Exploitation: The daring phase where the testers attempt to exploit discovered vulnerabilities, validating their severity and potential impact.
- Reporting: The journey’s culmination, this step involves meticulous documentation and reporting of findings, from pinpointed vulnerabilities to their potential repercussions and the roadmap to remediation.
Empowering Tools of the Trade
In this digital age, technology serves as both the assailant and the defender. Meet the champions in the realm of web security testing tools:
| Tools | Description |
|---|---|
| Burp Suite | A comprehensive toolkit revered in web application testing. It boasts an array of functionalities, including vulnerability scanning, the ability to intercept and modify requests, and insightful analysis of application behavior. Burp Suite is a Swiss Army knife for security professionals, enabling them to uncover, analyze, and address vulnerabilities effectively. |
| OWASP ZAP | An open-source security scanner with a mission: ferreting out vulnerabilities. It’s a dedicated guardian against threats like Cross-Site Scripting (XSS), SQL injection, and Cross-Site Request Forgery (CSRF). OWASP ZAP constructs an impregnable digital moat around your applications, shielding them from lurking dangers. |
| Nmap | A nimble network scanning tool that is a master at revealing the secret world of open ports. Nmap shines a light on the digital terrain, exposing the security weak points that might otherwise remain concealed. It’s an essential companion in the quest for digital fortification. |
| Nessus | A sentinel with an unwavering focus on vulnerability identification. Nessus is adept at uncovering vulnerabilities across a wide spectrum—web applications, networks, and even operating systems. Its vigilance extends far and wide, ensuring no digital nook remains unexplored. |
Talk to our Cybersecurity Expert to discuss your specific needs and how we can help your business.
Introducing Qualysec’s PenTest Solution
Amid this dynamic security landscape emerges Qualysec, a luminary in cloud-based vulnerability and compliance management solutions. Their arsenal equips enterprises to orchestrate continuous monitoring, vulnerability assessment, and comprehensive compliance management across their sprawling IT infrastructure.
Qualysec’s Cybersecurity services are an intricate dance of manual finesse and automated precision, maximizing vulnerability coverage. Their detailed reports unravel a prioritized compendium of vulnerabilities, accompanied by practical recommendations for ironclad remediation. It’s a partnership where Qualysec acutely understands your unique needs, tailoring their solutions to match.
An Array of Services
Qualysec extends an array of services encompassing:
- Web App Pentesting
- Mobile App Pentesting
- API Pentesting
- Cloud Security Pentesting
- IoT Device Pentesting
- AI /ML Pen-testing
Qualysec’s services come to the fore for businesses navigating industry regulations or those aiming to demonstrate their security commitment to stakeholders. By embracing Qualysec as your trusted sentinel, you are crafting a fortress for your web applications, ensuring their impregnability.
Key Hallmarks of Qualysec
- 3000+ Comprehensive Tests: An arsenal of tests capable of exorcising all forms of vulnerabilities.
- Business Logic Expertise: Uncovering business logic errors and security chasms.
- False Positives: Zealously minimizing false positives through meticulous manual pen testing.
- Compliance-Centric Scans: Enabling compliance with standards like SOC2, HIPAA, and ISO27001.
- Expert Remediation: Aiding remediation through in-call guidance from seasoned security experts.
Qualysec is another noteworthy player in the field of Web Application Penetration Testing services. Renowned for its in-depth assessments and meticulous approach, Qualysec aids businesses in understanding their cybersecurity posture. Their penetration testing methodologies go beyond identifying vulnerabilities; they provide comprehensive reports that assist organizations in implementing robust security measures.
Latest Penetration Testing Report

Conclusion: Web Application Penetration Testing
In a world where digital realms reign supreme, web application security testing stands as a hallowed rite of passage. It’s not just about safeguarding code; it’s about protecting your users, fortifying your business, and nurturing your growth. The choice between manual and automated testing may dance to different tunes. But, the symphony of securing your digital existence is unison. As we bid adieu, remember, it’s not just your web applications that are at stake—it’s the very essence of your digital journey. So, arm yourself with the knowledge, tools, and partners to ensure this journey is one of triumph, resilience, and lasting prosperity.
We’ve discussed the importance of a collaborative approach to cybersecurity. Web Application Penetration Testing Services play a vital role in organizations and government bodies. It plays its part by working together to strengthen the nation’s defenses. By embracing collective responsibility and fostering partnerships, a company can harness the power of collaboration to create a unified front against cyber threats.
When it comes to comprehensive cybersecurity audits, Qualysec is the organization to go with. Their cost of VAPT guide helps clients make informed decisions by understanding the various factors that affect the cost by clicking here.















































































































































































































































































































































































































































































































































































































































































































2 Comments