Key Takeaways
- CTEM solutions is a continuous, risk-based cybersecurity program, not a single tool.
- Focus shifts from “what is vulnerable” to “what is exploitable.”
- Validation (BAS, AEV, pentesting) is the most critical CTEM phase.
- Enterprises need a stack of integrated tools, not isolated solutions.
- Real CTEM success depends on mobilization (fixing issues), not just detection.
Introduction
Most enterprises do not realize how exposed they have become until a real incident forces them to ask that question. Over time, systems spread across cloud, APIs, SaaS tools, and connected environments, each adding another point of access that is easy to overlook.
Security teams are not short on data. They are flooded with it. The problem is knowing what actually matters. Long vulnerability lists create movement, but not always progress. That is why many organizations are turning to ctem platforms and tools, often supported by a CTEM solution focusing less on volume and more on exposures that can lead to real impact.
If your current efforts feel heavy but outcomes remain uncertain, there is a gap worth examining. In the sections ahead, you will see how this shift is changing enterprise security and what it takes to implement it effectively.
What is CTEM?
CTEM, or Continuous Threat Exposure Management, is a continuous program that helps you identify, validate, prioritize, and remediate exposures across your environment. It is not limited to a single tool or activity. It works as an ongoing process that keeps your security efforts aligned with actual risk.
An exposure includes more than just vulnerabilities. It covers misconfigurations, identity risks such as excessive access, and attack paths that connect multiple weaknesses. These are the conditions that can be used in a real attack scenario. It is important to separate the two ideas. A vulnerability does not always mean risk. An exposure represents something that is both exploitable and capable of causing impact.
CTEM cybersecurity solutions bring these elements together into one continuous program, so you are not managing risks in isolation but addressing them as part of a complete picture.
Benefits of Implementing CTEM in Enterprises
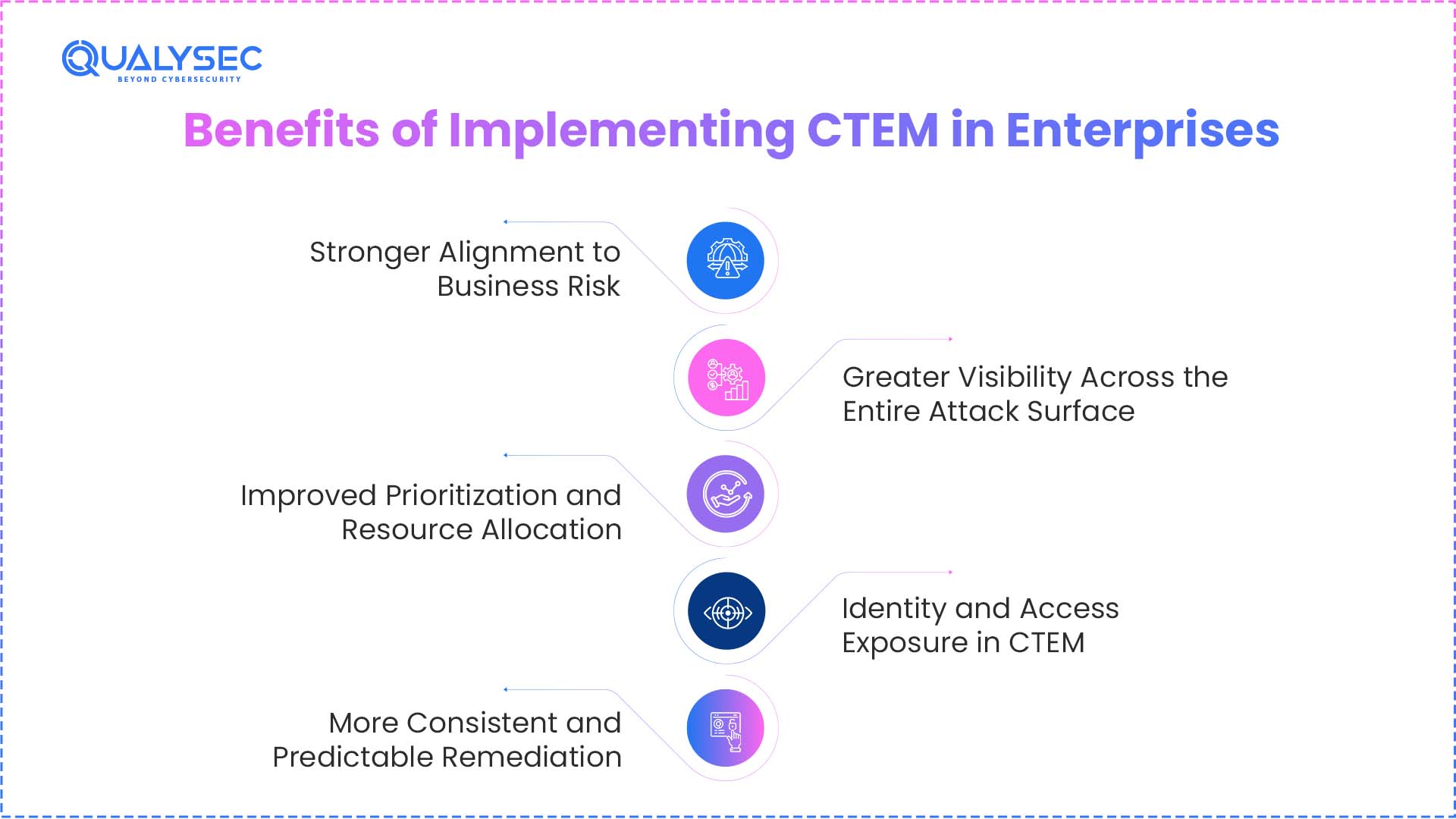
1. Stronger Alignment to Business Risk
Severity scores have their place, but they rarely tell you what actually puts your business at risk. A high score does not always mean high impact. What matters is how an exposure affects your revenue or compliance.
That is where risk-based vulnerability management starts to make sense. Instead of trying to fix everything, the focus shifts to exposures that can:
- Interrupt critical systems
- Affect customer-facing services
- Lead to regulatory issues
This keeps your team from getting pulled in too many directions. It also helps you stay focused on what actually needs attention.
It also makes conversations easier outside the security team. You are not just sharing technical details, you are explaining what those issues mean for the business. That clarity helps leadership make decisions faster with the right enterprise security solutions in place.
2. Improved Prioritization and Resource Allocation
Most security teams are not short on findings. They are short on clarity. Backlogs grow because everything looks important on paper.
A more practical approach focuses only on what attacks can exploit and on assets they are more likely to target. This filters out low-impact findings that consume time without reducing meaningful risk. Effort remains focused on exposures that can affect business operations.
With that clarity, planning becomes simpler. Security teams can allocate time and resources with confidence, avoid unnecessary work, and maintain steady progress using the right cyber risk reduction tools.
3. More Consistent and Predictable Remediation
Remediation often depends on urgency rather than process. One week is filled with high-priority fixes, the next slows down with little follow-through. That inconsistency makes it difficult to track progress or measure improvement over time.
When handled as an ongoing function, remediation becomes easier to manage and follow. Instead of ad hoc fixes, teams work within a clear structure:
- Defined workflows that outline how issues move from discovery to resolution
- Clear ownership across DevOps, IT, and security teams
- Shared visibility so nothing gets lost between handoffs
This brings better control to the process. Issues are resolved faster, tracking becomes straightforward, and accountability is no longer unclear. Teams can rely on consistent execution, supported by effective security operations solutions.
4. Greater Visibility Across the Entire Attack Surface
In most enterprises, visibility is fragmented. Different teams look at different parts of the environment, which leaves gaps that no one fully owns. That is how assets get missed, and risks go unnoticed.
A more complete view brings everything into one place, so you are not relying on partial data. This includes:
- Cloud environments and workloads
- SaaS applications in active use
- Identities and access controls across systems
- On-premises infrastructure that still supports core operations
When these areas are connected, common blind spots become easier to catch:
- Shadow IT that was never formally tracked
- Orphaned assets that remain exposed without ownership
This level of clarity helps leadership see actual exposure instead of isolated findings, especially when supported by the right exposure management platforms.
5. Identity and Access Exposure in CTEM
In most enterprise breaches today, identity is the initial entry point. Attackers do not always exploit software vulnerabilities. They exploit access.
CTEM expands visibility beyond systems to include identity-based exposures such as:
- IAM misconfigurations that grant excessive or unnecessary permissions
- Privilege escalation paths that allow low-level accounts to gain administrative access
- Stale or orphaned accounts that remain active without ownership
- Service accounts and machine identities with long-lived credentials
- Token misuse and credential leakage across APIs and cloud services
These identity risks often connect multiple systems and create hidden attack paths.
By including identity analysis within CTEM, organizations move closer to a Zero Trust model, where every access request is verified and continuously evaluated based on risk.
6. Measurable and Continuous Risk Reduction
Security reports can easily have a snapshot of a given time, but they seldom indicate whether the situation is getting better. This makes it hard to know whether or not your risk reduction efforts are effective.
By taking a continuous approach, you are able to monitor the alterations in exposure with time. This will provide you with better insight into whether risks are escalating or are being controlled.
It also supports practical needs across the business:
- Demonstrating progress when justifying budgets
- Tracking how your security program is maturing
- Aligning with governance and reporting expectations
Connect with our experts to see how CTEM works with real-world validation and measurable outcomes.
Talk with Qualysec experts today

Key Metrics for Measuring CTEM Effectiveness
To understand whether CTEM is actually reducing risk, enterprises rely on measurable indicators:
- MTTR (Mean Time to Remediate)
Tracks how quickly validated exposures are resolved - Exposure window
Measures how long a vulnerability or misconfiguration remains exploitable - Risk reduction trends
Shows whether overall exposure is decreasing over time - Validation coverage
Indicates what percentage of identified risks have been tested for real exploitability
These metrics help security teams move from activity-based reporting to outcome-driven security performance.
Improved Decision Making Through Continuous Validation
Many flagged issues never turn into real attack paths. Validating exposures against real-world scenarios filters out false positives and keeps attention on what can actually be exploited. Teams move forward with clearer judgment using risk-based vulnerability management.
5 Stages of CTEM
The CTEM framework is structured as a continuous cycle. Each stage builds on the previous one, helping you move from visibility to action without losing focus on real risk.
1. Scoping
This stage defines what actually matters. You identify critical assets, often referred to as crown jewels, and align security efforts with business priorities. Without this, everything looks equally important.
2. Discovery
Here, you map your environment as it exists today. This includes cloud assets, external-facing systems, and even shadow IT that may not be formally tracked but still adds risk.
3. Prioritization
Not all exposures need the same attention. Risk is evaluated using threat intelligence, business context, and whether an exploit is available. This helps narrow down what should be addressed first.
4. Validation
This is where you test Assumptions. Simulated attack scenarios confirm whether an exposure can actually be exploited, which removes false positives and brings clarity.
5. Mobilization
Once validated, issues move into action. Fixes are carried out through defined workflows, with coordination across DevOps and IT teams to ensure nothing stalls.
CTEM Architecture Blueprint for Enterprises
Running the CTEM framework is not about adding another tool. It comes together as a set of layers, each solving a specific part of the problem, but all working off the same view of your environment.
1. Visibility Layer
You start by knowing what exists. That sounds simple, but in most enterprises, assets are scattered. ASM tools and asset inventory systems help bring cloud resources, external assets, and even unmanaged systems into view.
2. Risk Analysis Layer
Once visibility is established, the focus shifts to understanding how exposures connect.
Modern CTEM programs go beyond isolated findings and use attack path analysis to map how an attacker could move through the environment. This includes:
- Lateral movement paths across systems, identities, and networks
- Chained vulnerabilities, where multiple low-risk issues combine into a critical exploit
- Graph-based risk modeling, which visualizes relationships between assets, users, and exposures
This approach reflects how real attackers operate. Instead of exploiting a single weakness, they move step by step until they reach high-value targets.
3. Validation Layer
This is where theoretical risk is tested against real-world conditions.Different validation methods have different purposes:
- BAS (Breach and Attack Simulation) confirms the ability of current security controls to identify and block the known attack methods.
- AEV (Adversarial Exposure Validation) works with the problem of validating entire attack paths through the chaining of multiple weaknesses.
- Penetration testing offers in-depth, hand-based testing of business logic vulnerabilities, sophisticated attack conditions, and actual exploitability.
Combined, these techniques eliminate false positives and ensure that you carry forward only exploitable, actionable risks.
4. Intelligence Layer
Threat intelligence feeds and exploit databases add useful context. They show what attackers are actively using, which helps you avoid treating every issue the same.
5. Execution Layer
Fixing issues should not feel disconnected. SOAR tools and ticketing systems like JIRA or ServiceNow make it easier to track progress and close gaps without delays.
6. Reporting Layer
Different teams need different views. Security teams track what they fix, leadership monitors overall exposure, and compliance teams rely on reports that reflect actual progress.
Download our sample pentest report to understand the depth and clarity you should expect.
Get a Free Sample Pentest Report

Types of CTEM Solutions (Tool Stack Breakdown)
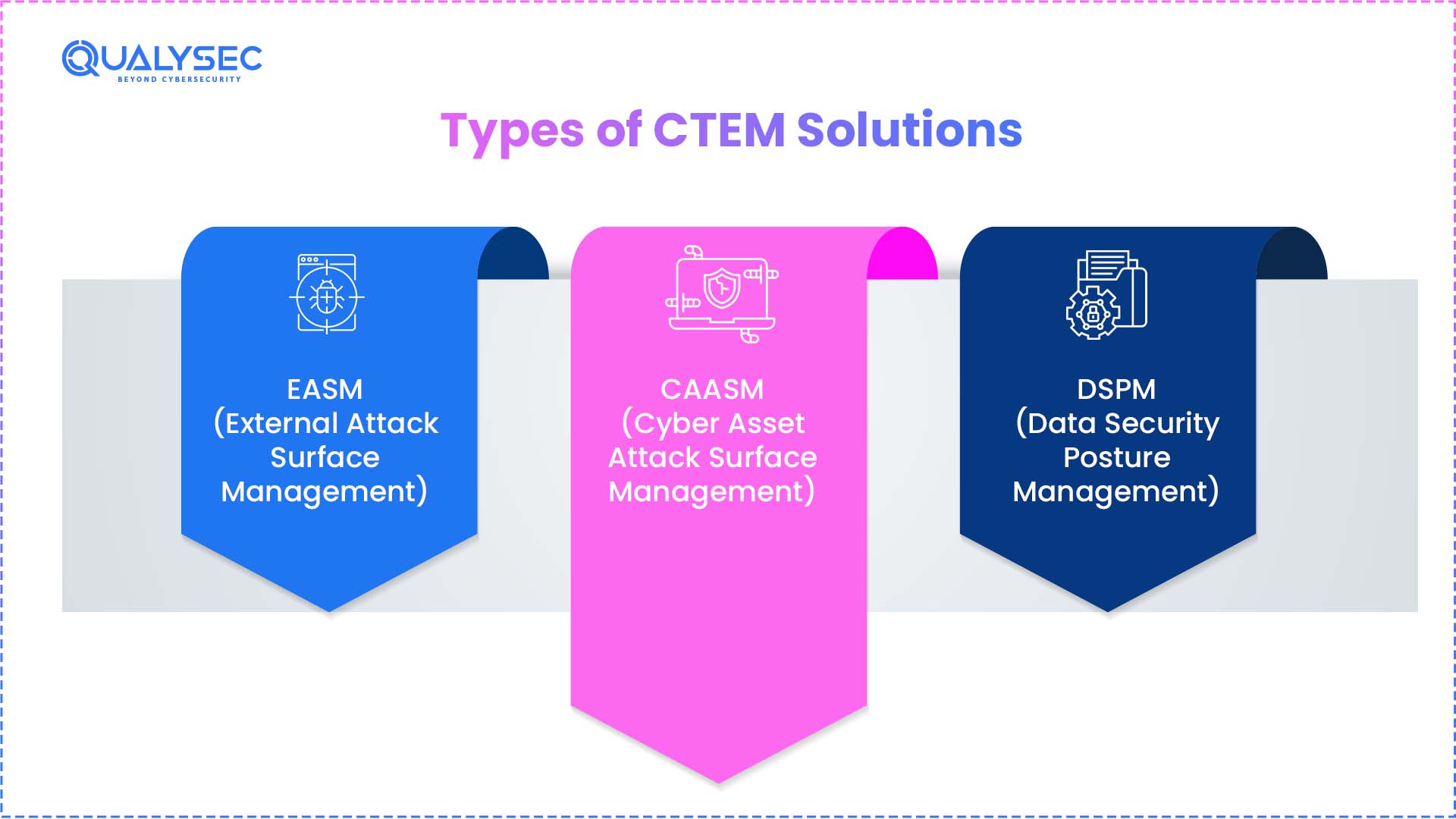
Modern Exposure Management Categories
As CTEM evolves, several specialized categories have become critical:
- EASM (External Attack Surface Management)
Focuses on discovering and monitoring internet-facing assets, including unknown or shadow systems - CAASM (Cyber Asset Attack Surface Management)
Provides a unified view of all assets across cloud, on-prem, and SaaS environments - DSPM (Data Security Posture Management)
Identifies where sensitive data resides and how it is exposed across systems
These categories strengthen CTEM by improving visibility across assets, identities, and data.
You are not dealing with a single product here. CTEM solutions come together as a mix of tools, each solving a specific part of the problem.
| Category | What It Does |
| Attack Surface Management | Finds external exposures, tracks internet-facing assets, and uncovers shadow IT that often goes unnoticed |
| Vulnerability Management | Identifies known vulnerabilities using CVEs and keeps systems under continuous scanning |
| Risk-Based Vulnerability Management | Prioritizes issues based on exploitability and business impact using risk-based vulnerability management |
| Breach and Attack Simulation | Runs automated attack scenarios to test how your defenses respond |
| Adversarial Exposure Validation | Validates real attack paths by connecting multiple weaknesses into practical scenarios |
| Continuous Pentesting | Combines human testing with automation to uncover deeper, less obvious issues |
| Remediation Orchestration | Automates workflows, assigns tasks, and tracks fixes through ticketing systems |
Best CTEM Solutions for Enterprises (2026 Comparison)
No single tool covers everything. What you choose depends on where your gaps are, whether that is validation or execution. The tools below are grouped by what they actually help you solve.
Continuous Validation and Exposure Testing
Cymulate
If you want to see how your defenses behave under pressure, Cymulate does that well. It runs ongoing simulations across different parts of your environment. It shows where controls hold up and where they do not.
Teams often use it to move beyond assumptions. Instead of guessing whether something works, you get direct feedback from simulated attack scenarios. It also connects easily with existing tools, so results do not sit in isolation.
Picus Security
Picus is more focused on cutting through noise. It helps you check which findings can actually be used in an attack and which ones are not worth chasing.
This becomes useful when your team is dealing with too many alerts. Rather than reacting to everything, you can narrow down to what is worth fixing based on real validation.
Full CTEM Platforms
XM Cyber
XM Cyber looks at how an attacker would move through your environment. Instead of isolated issues, it shows connected paths across systems.
This makes it easier to understand how a small gap in one place can lead to something bigger. It is especially helpful for environments where everything is interconnected.
Tenable One
Tenable One brings together asset data, vulnerabilities, and context into a single view. It helps you understand which issues actually matter in your setup.
Teams often rely on it when they need more than just scan results. It gives a clearer picture of risk by combining multiple data points in one place.
Attack Surface Discovery
IONIX
IONIX focuses on what exists outside your internal view. It continuously discovers internet-facing assets, including those that may not be tracked properly.
It also highlights risks tied to third-party services, which can easily be missed but still affect your overall exposure.
Risk Prioritization and Intelligence
Rapid7
Rapid7 adds context to vulnerability data. Instead of showing a long list, it helps you understand which issues attackers are more likely to target.
This makes prioritization less about guesswork and more about what is actually relevant in the current threat landscape.
Remediation and Execution
Reclaim Security
Reclaim Security is built for getting things fixed. It connects findings with workflows so issues do not sit unresolved.
For teams that struggle with follow-through, this kind of setup helps keep remediation on track. It ensures work moves forward without constant manual coordination.
Check this Comparison Table
| Category | Tool | What Stands Out |
| Continuous Validation | Cymulate | Ongoing attack simulations across multiple layers with strong integrations |
| Continuous Validation | Picus Security | Clear validation of exploitable issues reduces unnecessary alerts |
| Full Platform | XM Cyber | Attack path visibility and lateral movement mapping |
| Full Platform | Tenable One | Combines asset data, vulnerabilities, and context in one place |
| Attack Surface Discovery | IONIX | External asset discovery with third-party risk visibility |
| Risk Prioritization | Rapid7 | Adds threat context to help prioritize what matters |
| Remediation | Reclaim Security | Automates workflows and keeps remediation on track |
CTEM Platform vs Tool Stack: What Enterprises Should Choose
Most teams face this question once they start building their approach. Do you rely on a single platform or put together your own set of tools?
Platform approach
- Everything is managed in one place
- Easier for teams to adopt and operate
- Faster setup with less coordination required
- Depth can be limited in areas like validation or advanced testing
Tool stack approach
- You choose tools based on what each one does best
- Stronger capabilities in specific areas
- Requires effort to integrate and maintain
- Data and workflows can become fragmented
Explore our case studies, see how enterprises are reducing real-world security risks with CTEM.
See How We Helped Businesses Stay Secure

Key Features That Define Top CTEM Solutions
When you evaluate options, features matter less on paper and more in how they actually help your team make decisions and take action. A few capabilities tend to separate average setups from ones that work well in practice.
- Attack path analysis
Shows how different weaknesses connect. Instead of isolated issues, you see how an attacker can move across systems. - Continuous validation
Combines BAS and pentesting to check if exposures can actually be used. Keeps findings grounded in real conditions. - Risk-based prioritization
Helps you focus on what carries real impact, not just what looks severe in a scan report. - Real-time threat intelligence
Adds context from active threats, so you are not treating every issue the same. - Unified asset visibility
Brings cloud, SaaS, identities, and on-premises systems into one view, reducing gaps. - Automated remediation workflows
Moves issues into action without manual follow-ups. Helps teams stay on track. - Executive reporting dashboards
Translates technical findings into something leadership can understand and act on.
Common CTEM Implementation Challenges in Enterprises
Most teams do not struggle with the idea of CTEM. The friction starts when they try to run it consistently.
- Balancing automation with human effort
Tools can scan and flag issues all day, but they do not tell you what actually deserves attention. Someone still has to review the findings, connect the dots, and decide what matters. - Resource constraints
Security teams are usually working at capacity. Adding another continuous process without enough people or budget makes it harder to keep things moving. - Integration complexity
Nothing runs in isolation. New tools have to fit into what is already there, and that is rarely smooth. Getting systems to work together and share data properly takes time. - Volume of vulnerabilities
Even after filtering, there is still a lot to deal with. If prioritization is not handled well, teams end up back where they started, working through long lists without clear direction.
Why Enterprises Choose Qualysec for CTEM Validation
CTEM depends heavily on how well the validation stage is handled. You may already have tools for discovery and prioritization, but without proper testing, it is difficult to confirm what is actually exploitable.
What Qualysec Focuses On
- Supports the validation stage through penetration testing
- Confirms which exposures can be exploited in real conditions
- Helps filter out false positives from automated tools
How Testing Is Performed
- AI-assisted attack simulation to accelerate testing coverage
- Scenario-based validation that mimics real-world attacker behavior
- Automated attack chaining to identify multi-step exploit paths
Qualysec focuses specifically on penetration testing across web, mobile, APIs, cloud, and IoT environments. This ensures exposures are tested where they actually exist, not just identified.
The reports are structured for developers, with clear remediation guidance and retesting support to confirm fixes. This makes it easier to move from validation to resolution without delays. If the CTEM process highlights risks but does not clearly show what can be exploited, reviewing the penetration testing approach can make a significant difference.
Conclusion
CTEM is not about adding another tool to your stack. It is an ongoing way of working that keeps up with how your environment keeps changing. What really makes a difference is what happens after issues are found. If they are not properly tested and fixed, the effort does not lead anywhere. even when by a CTEM Solutions.
For most enterprises, the gap is not in discovery. It is in knowing what is actually exploitable and making sure it gets resolved. That is why validation and remediation carry more weight than anything else. When you handle these parts well and connect them with the rest of your process, the entire approach starts to make sense.
At that point, it comes down to how you put things together, the tools you rely on, and the partners you bring in to make sure the work leads to real outcomes.
Schedule a call with our experts and see how CTEM can work for your business.
Speak directly with Qualysec’s certified professionals to identify vulnerabilities before attackers do.
FAQs
1. What are the 5 stages of CTEM?
The CTEM lifecycle includes five stages: scoping, discovery, prioritization, validation, and mobilization. The process starts with identifying critical assets, then maps exposures, narrows down what matters, confirms what attackers can exploit, and finally fixes those issues.
2. What is a CTEM solution?
A CTEM solution is not a single product. It is a combination of tools and processes used to continuously identify, assess, validate, and remediate exposures across an environment.
3. Who needs CTEM solutions?
Enterprises with complex environments benefit the most. CTEM brings structure to risk management when you manage cloud assets, APIs, SaaS tools, and on-premises systems together.
4. How do CTEM solutions work?
They work as a continuous cycle. The process discovers assets, analyzes risks, validates exposures through testing, and carries out remediation. It runs continuously instead of being done once.
5. Are CTEM solutions cloud-based?
Many tools used in CTEM are cloud-delivered, but the approach itself does not limit users to the cloud. It covers cloud, on-premises systems, and hybrid environments.
6. What problems do CTEM solutions solve?
They help reduce noise from large vulnerability lists, improve prioritization, validate real risk, and ensure that teams actually fix critical exposures instead of overlooking them.














































































































































































































































































































































































































































































































































































































































































































0 Comments