With the increasing speed of digitalization in the financial sectors of the world, security compliance for financial institutions is now an important concern. To highlight this even further, by 2025, cybercrime will cost the globe $13.82trillion per year–almost doubling the amount of $8trillion in 2023. This is because in the financial sector that manages in excess of 475 trillion dollars in assets globally, cyberattacks and breaches of information are the order of the day, making it the most targeted sector in 2024, with 27% of data breaches. This year, more than $53billion was lost to financial fraud across the world, and ransomware attacks against banks, neobanks, and fintech levels have increased by 34% in 2022. Regulatory pressure is high, and 94 percent of financial organizations globally experienced at least one audit or regulatory examination in the previous 12 months, with 93 percent in fiscal 2025 recognizing security compliance as a high priority.
Regulators are on an offensive footing: 74% of the financial institutions reported that they faced augmented control expenditure in 2024, and 71% said that they have had to temporarily halt digital services in order to remediate compliance gaps. On average, breach of compliance costs an average of 5.1million dollars in fines, as well as lawsuit settlements and remediation per breach. These figures help to illustrate the truth that compliance with the security of financial organizations is no longer a legal nuisance but a business necessity. As regulators implement new frameworks such as the European DORA (Digital Operational Resilience Act) and increase their enforcement of PCI DSS, NYDFS, and FFIEC requirements, 2025 cannot afford to be an off-year.
To ensure your institution’s success in this unforgiving threat landscape, partner with verified security experts like Qualysec Technologies. Contact Qualysec to schedule a compliance readiness assessment.
What Is Security Compliance for Financial Institutions?
Security compliance for financial institutions is the systematic observance of the international, domestic, and industry-specific security requirements that relate to safeguarding sensitive information, privacy, and business continuity. The financial organization, in this case, is a bank, credit union, lending company, fintech startup, insurance company, or digital wallet.
The important pillars of compliance nowadays include –
- Protect customer financial and personal information (PII) and bank account details
- Ensuring effective IT controls to detect, respond and recover from incidents
- Having the capacity to meet current audit, reporting, and governance requirements
- Compliance with anti-money laundering (AML), fraud, and suspicious activity monitoring
Key Regulations for Financial Institutions

1. PCI DSS Compliance for Banks
The Payment Card Industry Data Security Standard, or PCI DSS compliance for banks, is the independent security standard that organizations accept globally to deal with payment cards. These requirements of PCI DSS v4.0 are enforced in 2025 –
- MFA to all cardholder information access
- Strict data encryption in transit and at rest
- Vulnerability checks and penetration testing every year
- Long-term third-party threat monitoring of service providers
Failure to comply with the PCI DSS may lead to fines of up to $500,000 per incident, the loss of the privilege to process cards, and a damaged reputation.
2. FFIEC Cybersecurity Guidelines
The Federal Financial Institutions Examination Council (FFIEC) introduces a standardized structure of the U.S. banking regulatory compliance requirements. The FFIEC cybersecurity guidelines are also the general global reference, which is used by more than 70 percent of non-U.S. financial organizations by 2025.
Key focus areas –
- Cyber risk management governance & oversight
- In-depth cybersecurity control assessments
- Sector-wide information sharing (ISACs)
- Ongoing independent audit and control testing
3. NYDFS Cybersecurity Regulation
The New York Department of Financial Services, or NYDFS cybersecurity regulation has security standards that are as high as, compared to what could be known as advanced cybersecurity compliance for banks and insurance companies within or working in the state. The 2023 amendments (effective for global firms by 2025) now include –
- 24-hour breach notification requirements
- Annual CISO attestation of compliance
- Third-party risk management standards
- Zero-trust architecture for critical systems
Firms non-compliant with NYDFS risk fines starting at $250,000 per violation, individual executive sanctions, and closure of business in New York State.
4. SOC 2
SOC 2 (System and Organization Controls 2) is not industry-specific but broadly used by financial institutions and financial services technology providers around the world. It targets the criteria relating to Trust Services: security, availability, processing integrity, confidentiality, and privacy.
A SOC 2 audit provides additional risk management assurance that your system architecture and processes protect your financial data in supporting due diligence in vendor risk management and customer assurance.
5. NIST Cybersecurity Framework
The NIST Cybersecurity Framework (CSF) is used as a best practices blueprint for regulators and multinational financial services firms. The latest 2024 NIST 2.0 update emphasizes –
- Continuous identification of new risks
- Real-time incident response capabilities
- Tiered, risk-based maturity assessments
Prescribing NIST CSF has become compulsory as of 2025 in the regulatory governance of over 56 countries’ banks.
Best Practices to Stay Compliant
The only strategy that can help organizations achieve and maintain security compliance when it comes to financial institutions is proactive and data-driven. Best practices in 2025 will be –
- Automated Compliance Monitoring – 74 percent of compliance monitoring in finance is now driven by AI-based tools, which reduce human error and are real-time alert drivers.
- Periodic Security Training – Periodic employee training minimizes the possibility of hacking and insider attacks. 85% of compliant firms run mandatory quarterly training.
- Resilient Vendors Risk Management – Partner rupture of 43 percent of incursions occurred in 2024. Zero-trust controls are a regular practice and an annual third-party audit.
- Incident Response Testing – A reduction in mean time to detect and respond to a cyber threat was with 38 percent among compliant firms as a result of their incident response simulation tasks on a yearly basis.
- Safe Move to Cloud – 92 % of institutions that have adhered to compliance use multi-cloud features secured through stringent configuration auditing standards and encryption standards.
The Role of Penetration Testing in Compliance
Security compliance among the financial institutions hangs on penetration testing.
- Over 99% of the regulatory frameworks (PCI DSS compliance for banks, FFIEC, NYDFS, SOC 2, NIST, etc) now require an annual or more frequent penetration test.
- Penetration tests exploit vulnerabilities, misconfigurations, and compliance failures to make them visible before unscrupulous users can compromise them.
- Organizations that have invested in proven process-based penetration testing have seen 54 percent fewer critical findings revealed in external audits and up to 70 percent faster compliance remediation cycles.
Latest Penetration Testing Report

Common Compliance Challenges & How to Overcome Them
Rapidly Changing Regulations
- Sixty-one percent of financial firms indicated it was a challenge to keep up with new or updated regulatory requirements over the last year.
- Solution – Develop automated compliance tracking tools and have constant contact with legal/ compliance specialists.
Resource Constraints
- 46% cited insufficient skills or staffing as a barrier to compliance.
- Solution – Leverage external partners for process-driven audits, training, and security testing.
Fragmented Data Environments
- Hybrid and multi-cloud operations may cause data silos that make audit channels and implementation of controls difficult.
- Solution – Unify log management, enforce integrated access controls, and make use of continuous monitoring platforms.
Third-Party Risks
- Third-party vendors were the cause of 58 percent of non-compliance incidents in 2024.
- Solution – Conduct vendor security assessments annually and in contractual compliance requirements.
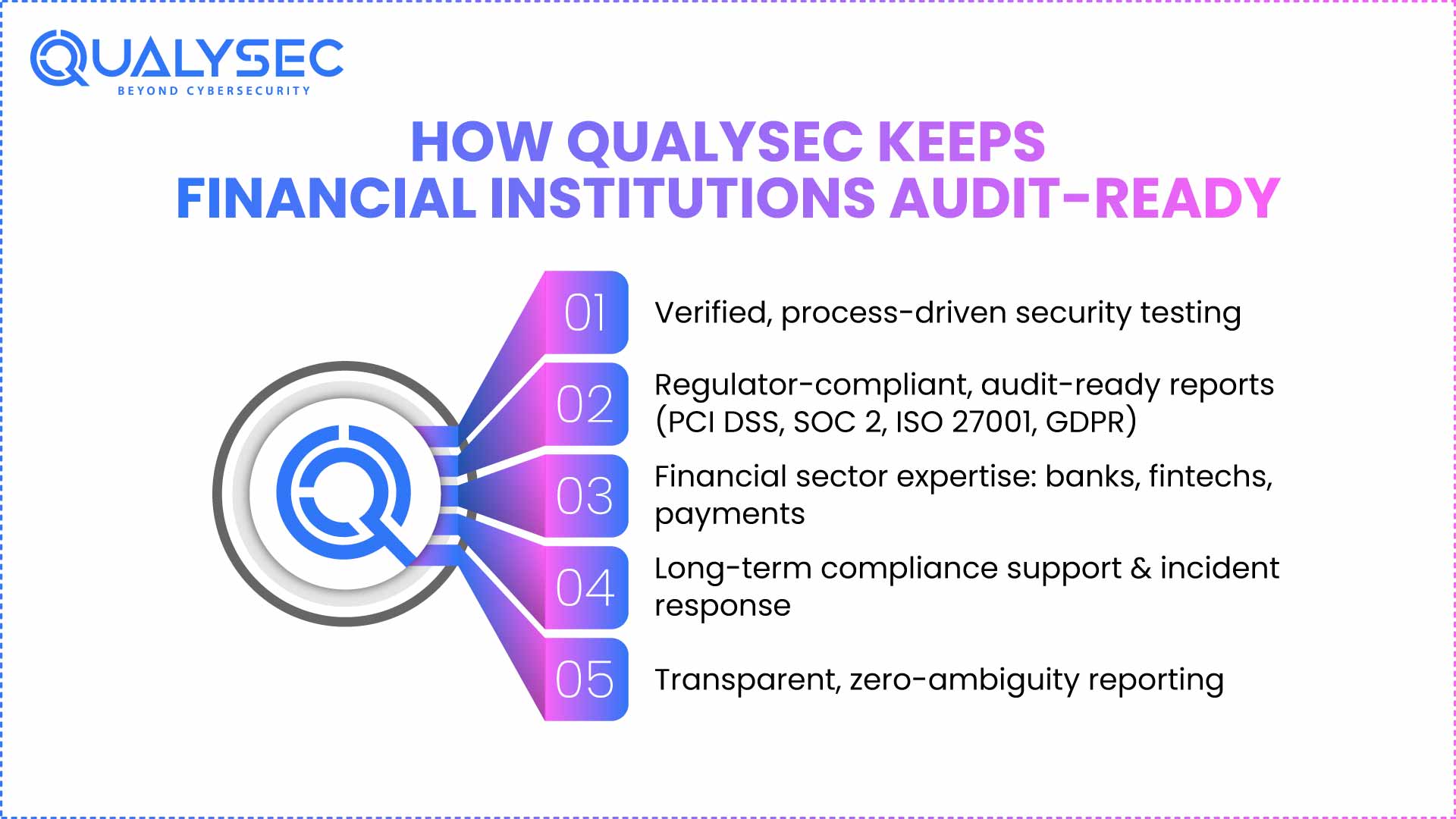
How Qualysec Helps Financial Institutions Stay Audit-Ready
About
Qualysec Technologies is an award-winning cybersecurity company focused on security compliance for financial institutions worldwide.
Services
End-to-end compliance-driven penetration testing, vulnerability assessments, security audits, and cybersecurity consulting for the financial sector.
Our Unique Value Proposition
- Verified Process-Based Testing – What sets Qualysec apart is our patented, process-driven approach to security testing. Every engagement follows a documented, transparent process verified by independent experts. Our proprietary process outshines international benchmarks in identifying, reporting, and tracking all identified risks to have them repaired with a full audit trail.
- Audit-Ready Documentation & Evidence – Qualysec provides extensive, regulator-compliant reports aligned with industry and international benchmarks: PCI DSS, FFIEC, NYDFS, SOC 2, NIST, ISO 27001, and GDPR. Our evidence packages prove all the findings, so you can always pass on an audit.
- Sector-Specific Expertise – All Qualysec consultants are specially trained in banking regulatory compliance requirements and financial data security compliance. Our team has decades of expertise in international banks, fintechs, lenders, and digital payments platforms.
- Continuous Partnership – We are not limited to single-time testing; we guide you to long-term compliance by monitoring, training personnel, providing risk management pointers, and responding to incidents.
- Objective, Transparent Reporting – Our “zero-ambiguity” reporting empowers your technical and executive stakeholders alike. With deep-dive analytics and executive summaries, you’ll always know your compliance status and what steps to take next.
Why Choose Qualysec for Your Financial Services Cybersecurity Compliance?
Selecting Qualysec will place your financial services cybersecurity compliance in line with the future of 2025 and beyond. Our combination of checked process-oriented testing, industry experience, and a deep documentation pathway gives clients a decisive advantage in audit readiness, compliance, and operational resiliency.
Take the first step to bulletproof security compliance for financial institutions. Book your personalized compliance consultation with Qualysec now.
Conclusion
Security compliance for financial institutions is no longer just an IT concern—it’s essential to business survival, trust, and growth. Threat actors continue to advance, and regulating environments become increasingly more stringent, leaving your only defense to be tested and ongoing, process-based practices.
It is important to leave your compliance- and your reputation- to chance. Turn cybersecurity into a business driver with the help of quality infrastructure technologies professionals at Qualysec Technologies, who are unmatched in assurance, transparency, and outcomes to provide a balanced auditability process.
Transform your approach to financial data security compliance – start your journey with Qualysec today.
Talk to our Cybersecurity Expert to discuss your specific needs and how we can help your business.
FAQ
1. Which cybersecurity regulations apply to banks and fintech companies?
The principal financial services cybersecurity compliance that governs the practice of financial organizations around the world is PCI DSS, SOC 2, NIST Cybersecurity Framework, FFIEC cybersecurity guidelines, NYDFS cybersecurity regulation, and domestic data protection regulations, including GDPR (Europe), CCPA (California), and DORA (EU). Specific needs vary according to the geographies, services, and customer base of the institution.
2. How can financial institutions prepare for a compliance audit?
Start with a gap analysis of standards or regulations of relevance, including PCI DSS or FFIEC. Perform process-based pen testing, review vendor and cloud controls, have a robust section of documentation, and ensure that the staff are trained on their aspect of compliance.
3. What are the penalties for non-compliance in the financial sector?
Penalties differ according to regulations and different geographical locations. Violation fines can be as high as five million dollars per violation, with PCI DSS non-compliance possibly causing elimination of card processing privileges, and repeated violations can suspend a business, lead to criminal prosecution, and the destruction of reputations.
4. How often should financial institutions perform security assessments?
The majority of frameworks will need at least a minimum of annual penetration testing or security evaluation. Good practice (and in highly regulated jurisdictions) requires reviews every six or three months, particularly following major changes in infrastructure, systems, or processes.











































































































































































































































































































































































































































































































































































































































































































0 Comments