An essential security feature in cloud service providers desiring to service the federal government is FedRAMP vulnerability scanning. Such a strict policy is the Federal Risk and Authorization Management Program (FedRAMP), which requires an overall evaluation of vulnerabilities to comply with a high level of security of a cloud system before processing government information. Vulnerability scanning is the backbone of continuous monitoring of the security objectives of organizations because it enables them to detect their security fluctuations and to mitigate the effects before being taken advantage of by ill-minded individuals.
As critical as it is, the FedRAMP vulnerability scanning requirements must be understood by any organization intending to seek FedRAMP authorization. This is a detailed handbook that covers the tools, techniques, and best practices in the execution of practical vulnerability scanning programs that can meet federal security standards. Having just started with the FedRAMP process or hoping to be able to strengthen your current security position, this article will contain the steps to move forward with the issue of compliance.
What Is FedRAMP Vulnerability Scanning?
FedRAMP vulnerability scanning can be defined as the methodical procedure of identifying, reviewing, and reporting security vulnerabilities that are found in the cloud systems that are used by the federal agencies. This is an automatic security evaluation method that analyses networks, applications, and infrastructure components to identify known weaknesses in security, misconfigurations, and probable attack vectors.
In contrast to typical vulnerability scanning, FedRAMP vulnerability scanning is required to be performed according to particular federal guidelines and rules. The scanning process will imply the implementation of specialized tools able to establish vulnerabilities on various levels of the technology stack, such as operating systems, databases, web application, and network devices.
FedRAMP vulnerability scanning is mainly aimed at achieving the following objectives:
- Identification of danger: Finding the security weaknesses prior to use of the security vulnerability
- Compliance verification: The confirmation of systems in line with security requirements in the federal level
- Ongoing assessment: Offering the assessments on security continuity as an element of the FedRAMP authorization process
- Remediation advice: Providing remedial guidance to be applied to take care of reported weaknesses
What are FedRAMP Vulnerability Scanning Tools for Best Practices?
FedRAMP vulnerability scanners are specific security assessment tools that pertain to federal standards necessary to ensure compliance with government demands, and at the same time implement in dissimilar solutions with substantial vulnerability identification capability. Such tools should show the capacity to scan complicated cloud environments, to integrate with current security postures, and write reports that meet the federal auditing standards.
The most effective tools used to scan the vulnerabilities of FedRAMP are those that incorporate both automated discovery functions and a great reporting facility. They also accommodate many types of scanning models (authenticated and unauthenticated scans) and could be used to scan both the internal and external-facing systems. The tools also have a vulnerability prioritization element that includes prioritization of risks based on their severity to ensure security teams prioritize the work on the most essential problems.
Partner with Qualysec to implement top-tier FedRAMP scanning tools and best practices. Get a Free Compliance Consultation.
Qualysec’s cloud pentest gives you results—no endless emails, no digging through PDFs, no guesswork.

FedRAMP Vulnerability Scanning Requirements
The requirements of FedRAMP vulnerability scanning are listed under the FedRAMP Security Assessment Framework and should be applied during the authorization lifecycle. Such requirements take care of the fact that cloud service providers still have strong security postures as they serve federal agencies.
Core Scanning Requirements
The basic FedRAMP vulnerability scanning requirements are:
- Authenticated scans: At least once per month, systems should be scanned thoroughly for vulnerabilities
- External scan weekly: The Sort of system that is accessible on the Internet should be scanned weekly to determine vulnerabilities
- Credentialed scanning: A proper credential is required for scans to evaluate the internal system’s configuration
- Database and web application scan: Database and web application scans are required
- Operating system tests: Each of the operating systems should also be checked routinely by using known vulnerabilities
Documentation and Reporting Standards
The FedRAMP penetration tests and vulnerability scanning events have to be well documented. FedRAMP process necessitates reports that are detailed and joined by:
- Vulnerability descriptions and severity ratings
- Components of affected systems and possible impact evaluations
- Remediation durations and risk management programmes
- Documentation of the testing and results of the vulnerability checks
- The trend analysis and updates of compliance status
Qualysec delivers detailed, standardized documentation and reporting that aligns with FedRAMP and industry compliance requirements. Download a Sample Report.
FedRAMP-Approved Vulnerability Scanning Tools
Successful FedRAMP vulnerability scanning implementation depends on the choice of tools. Although FedRAMP does not have an official list of approved tools, some of the solutions are recognized as effective tools to address federal needs.
Enterprise-Grade Scanning Solutions
Qualysec is the ultimate solution when it comes to organizations that require the capabilities of scanning their vulnerabilities under FedRAMP. Having more than 10 years of experience in cybersecurity evaluation, Qualysec provides unique services that match the necessities of federal compliance.
Key Services of Qualysec:
- Comprehensive vulnerability assessments covering all FedRAMP security controls
- Professional pentesting services as per the federal requirements
- Constant surveillance systems that work with the current security systems
- Compliance reporting in detail based on the federal auditing standards
- The 24/7 coverage of security protection that guarantees a quick reaction to high-threat vulnerabilities
The FedRAMP vulnerability scanning under Qualysec deploys automated tools in conjunction with expert analysis, providing organizations with vulnerability data consisting of actionable intelligence. Their team consists of certified security experts who can advise organizations through complicated remediation procedures since they are aware of the intricacies behind federal compliance.
Location: Qualysec has offices in the main metropolitan areas that offer localized support to various federal agencies and contractors in the country.
Unique Selling Points:
- Specialised FedRAMP compliance expertise with a proven track record
- Advanced scanning methodologies that minimise false positives
- Integration capabilities with popular security orchestration platforms
- Custom reporting formats that align with federal documentation requirements
- Ongoing support throughout the entire FedRAMP authorisation process
Schedule a free consultation with Qualysec today to discuss your FedRAMP vulnerability scanning requirements and learn how their expertise can accelerate your authorization timeline.
Additional Scanning Tools
Other distinguished FedRAMP vulnerability scan tools are:
Nessus Professional: Powerful vulnerability scanner with rich and diverse plugin support and reporting features against an extensive, colossal library of more than 43,000 available.
Rapid7 Nexpose: It is an enterprise-level vulnerability management platform that provides features of continuous monitoring and risk assessment capabilities in the context of compliance guidance.
OpenVAS: Open vulnerability scanner with some minimal scanning features, but it can also require configurations to be fully compliant with FedRAMP.
How to Conduct FedRAMP-Compliant Vulnerability Scans
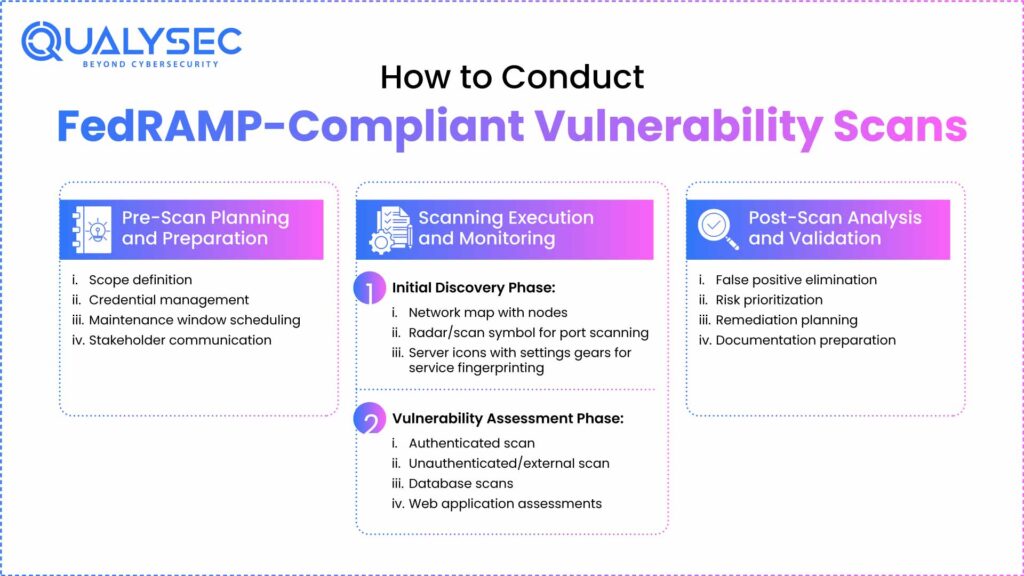
Establishing efficient FedRAMP vulnerability scanning needs an operational procedure that takes into account material as well as practices. The given technique guarantees the opportunity to cover all of the aspects without falling short of federal standards.
Pre-Scan Planning and Preparation
An organization should have proper procedures and required authorizations before starting FedRAMP vulnerability scanning activities:
- Scope definition: A Clear definition of all the systems, networks, and applications that will be the scanning scope
- Credential management: Availability and secure management of the right scanning credentials will be implemented
- Maintenance window scheduling: Plan scans at allowable maintenance windows to avoid disruption of operations as much as possible
- Stakeholder communication: Important groups should receive updates about intended scanning exercises and the thoughtful impacts of the system concerned.
Scanning Execution and Monitoring
The FedRAMP vulnerability scanning is actually a process composed of several steps:
Initial Discovery Phase:
- Mapping of networks to find out all reachable systems and services
- Port scanning with the purpose of enumeration of available services and applications
- Fingerprinting of services to identify versions and settings of software
Vulnerability Assessment Phase:
- Authenticated scans using appropriate credentials to assess internal configurations
- Unauthenticated scans to identify externally visible vulnerabilities
- Database-specific scans for systems containing sensitive data
- Web application security assessments for internet-facing applications
Post-Scan Analysis and Validation
Following FedRAMP vulnerability scanning execution, teams must analyze results and validate findings:
- False positive elimination: Review and verify scan results to remove false positives
- Risk prioritization: Assess vulnerabilities based on potential impact and exploitability
- Remediation planning: Develop detailed plans for addressing identified vulnerabilities
- Documentation preparation: Create comprehensive reports that meet federal documentation standards
Qualysec offers cost-effective scanning services tailored to your compliance level. View Pricing Packages.
Our experts at Qualysec have helped secure fintech, SaaS, and enterprise systems across 25+ countries. Manual + Automated Pentesting. No false positives. Actionable reports.

Common Challenges in FedRAMP Vulnerability Scanning
When organizations seek to become compliant with FedRAMP vulnerability scanning, a variety of challenges arise and may affect the security position and the time of authorization.
Technical Implementation Challenges
Complex Clouds Architecture: The classic scanning tools do not sufficiently evaluate the contemporary cloud environments, which pose special scanning issues with dynamic IP addresses, containerized applications, and serverless functions.
Issues on Network Segmentation: Network segmentation has a possibility of limiting the scanner access to critical systems. Thus, this needs careful planning so as to have a good coverage without the encroachment of the security barriers.
Legacy System Integration: Most of the existing federal-based agencies use legacy systems that are incapable of supporting new scanning standards or will require unique vulnerability assessment methodologies.
Compliance and Documentation Challenges
Reporting Standardization: Producing reports that provide commercial documentation as well as technically actionable information can also be a complex undertaking when there is no standard tool or knowledge related to it.
Continuous Monitoring Integration: Strategic issues to consider in smart resource allocation involve planning and coordinating how to keep FedRAMP vulnerability scanning sustainable without complex integration problems with ongoing continuous monitoring programs.
Talk with our experts to understand how Qualysec can help overcome these common challenges and streamline your FedRAMP authorization process.
Best Practices for FedRAMP Vulnerability Scanning
Efficient FedRAMP vulnerability scanning demands that all the best practices put in place follow guidelines that guarantee full coverage and efficiency in operations undertaken.
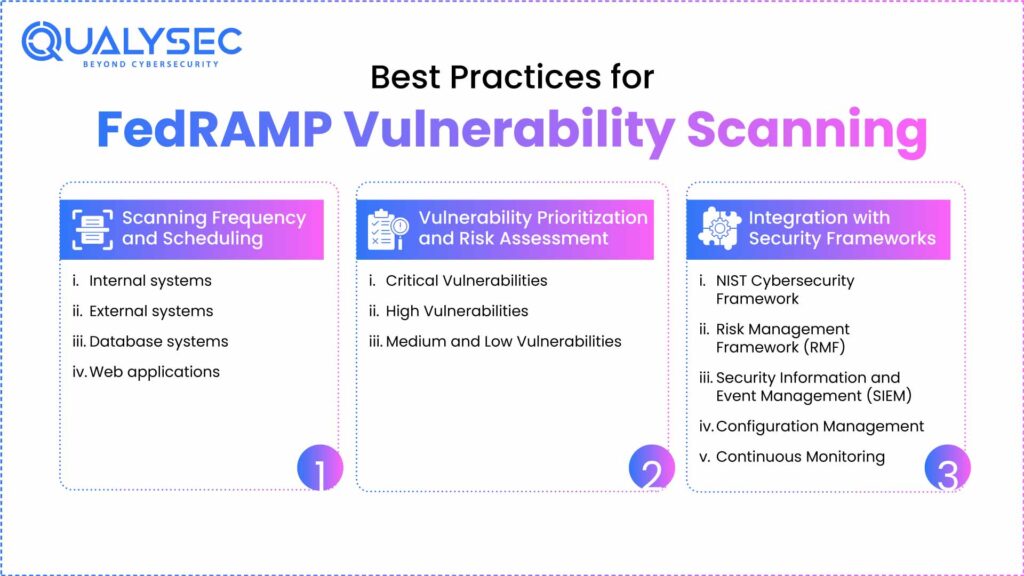
Scanning Frequency and Scheduling
FedRAMP vulnerability scanning requirements mandate specific scanning frequencies:
- Internal systems: Monthly comprehensive scans with weekly high-risk system assessments
- External systems: Weekly scans for internet-facing components
- Database systems: Monthly authenticated scans with quarterly comprehensive assessments
- Web applications: Continuous monitoring with monthly detailed assessments
Vulnerability Prioritization and Risk Assessment
Effective FedRAMP penetration testing and vulnerability management requires systematic risk prioritization:
Critical Vulnerabilities (CVSS 9.0-10.0):
- Immediate remediation is required within 15 days
- Executive notification and emergency change processes
- Temporary compensating controls if immediate patching isn’t possible
High Vulnerabilities (CVSS 7.0-8.9):
- Remediation within 30 days
- Standard change management processes
- Regular monitoring until resolution
Medium and Low Vulnerabilities:
- Remediation within 90 days based on risk assessment
- Batch remediation during scheduled maintenance windows
- Ongoing monitoring for potential escalation
Integration with Security Frameworks
FedRAMP vulnerability scanning should integrate seamlessly with existing security frameworks:
- NIST Cybersecurity Framework: Match scanning action to the functions of the framework.
- Risk Management Framework (RMF): Combine the data about vulnerabilities in continuous monitoring procedures.
- Security Information and Event Management (SIEM): Monitoring of vulnerability information in centralized systems.
- Configuration Management: This is used to coordinate scanning together with configuration control activities.
- Continuous Monitoring (ConMon) of Vulnerability Scanning.
Integrating Vulnerability Scanning Into Continuous Monitoring (ConMon)
Continuous monitoring programs with regular FedRAMP vulnerability scanning as one of the fundamental elements are necessary in the process of FedRAMP. This integration provides continuous security visibility and compliance uphold during the authorization life cycle.
Automated Scanning Integration
Successful continuous monitoring programs implement automated FedRAMP vulnerability scanning processes:
- Scheduled scan execution: Automated scans running according to FedRAMP frequency requirements
- Result aggregation: Centralized collection and analysis of scanning data from multiple tools
- Trend analysis: Historical vulnerability data analysis to identify emerging threats and systemic issues
- Alert generation: Automated notifications for critical vulnerabilities requiring immediate attention
Reporting and Dashboard Integration
Effective continuous monitoring requires comprehensive reporting capabilities:
Executive Dashboards:
- High-level security posture summaries with trend analysis
- Compliance status indicators and risk metrics
- Remediation progress tracking and timeline management
Technical Reports:
- Detailed vulnerability listings with technical descriptions
- Remediation guidance and testing procedures
- System-specific assessments and configuration reviews
Download our comprehensive pentest report template to understand how proper documentation supports successful FedRAMP authorization.
Metrics and Key Performance Indicators
Successful FedRAMP vulnerability scanning programs track specific metrics:
- Mean time to detection (MTTD): Average time to identify new vulnerabilities
- Mean time to remediation (MTTR): Average time to resolve identified vulnerabilities
- Vulnerability trend analysis: Tracking vulnerability counts and severity over time
- Compliance percentage: Percentage of systems meeting scanning frequency requirements
Latest Penetration Testing Report

Conclusion
Vulnerability scanning in FedRAMP is a crucial aspect of the federal cloud security requirements, and it requires high proficiency skills as well as elaborate implementation plans. Organizations seeking FedRAMP certification should install rigorous scanning programs that can effectively cover the cost of meeting the strict federal requirements and thrive on efficiency.
The key to successful FedRAMP vulnerability scanning is to choose suitable tools, work out processes, and have the possibility to continue monitoring. With the best practices methodology as discussed in this guide and using the services of security partner companies, organizations can indeed traverse through the complex security requirements of FedRAMP and achieve good security foundational grounds.
Since federal agencies are trending towards greater adoption of cloud, it will only become more significant to have effective FedRAMP penetration testing and vulnerability management. Companies that have invested in the development of complete security test mechanisms today are in a better position to handle federal markets and secure government-sensitive data.
The FedRAMP pentest guidance and FedRAMP penetration test guidance presented in this article can act as the basis for developing effective security programs. Nevertheless, it usually takes expertise and long-term assistance by security specialists to be implemented successfully.
Partner with Qualysec to get expert-led vulnerability scanning, clear documentation, and full FedRAMP alignment. Trusted by leading cloud service providers. Book Your Free Consultation Today → Schedule Now
Talk to our Cybersecurity Expert to discuss your specific needs and how we can help your business.
FAQs
1. What is the difference between vulnerability scanning and penetration testing?
Vulnerability scanning refers to the tools that scan the installed systems and applications and retrieve the known security weakness with comprehensive coverage and limited depth. FedRAMP penetration testing is a form of penetration testing that is a combination of automatic scanning and manual exploitation methodologies and mimics the actions of a real-world attacker to verify the vulnerability status and exploitability of any discovered vulnerability.
2. How often should vulnerability scans be performed under FedRAMP?
The FedRAMP vulnerability scanning requirements state that the continuous vulnerability scanning should have specific frequency requirements, depending on the categorization of systems. Testers must conduct vulnerability testing on high-impact systems monthly, with an authenticated test every three months. They should also conduct monthly vulnerability testing on moderate-impact systems, adding authenticated testing at one-quarter intervals.
3. Do we need to scan staging environments too?
Yes, the FedRamp vulnerability scanning requirements apply to all environments that process, store, or transmit federal data including staging and development environments. These un-production systems tend to have the same configuration, as well as code, as production systems but they might not have the same protection measures, which makes them possible targets of attackers.
4. Can we use open-source scanners for FedRAMP?
Although open-source vulnerability scanners may be included in FedRamp vulnerability scanning programs. They have to satisfy the same rigour and documentation requirements as commercial ones. An organisation should prove that it has sufficient coverage using open-source tools, is up-to-date in terms of vulnerability databases, and produces reports that are in compliance with federal documentation reports. FedRamp process necessitates elaborate tool validation and constant upkeep of tools, whether they are commercial or open-source in nature.
Have any questions? Feel free to ask now—our cybersecurity experts are here to help.











































































































































































































































































































































































































































































































































































































































































































0 Comments