NIST 800 53 compliance is the standard when it comes to safeguarding sensitive government data and federal information systems. In addition, this holistic cybersecurity framework will address the rising threats to organizations today. In fact, according to recent reports, in the past year alone, cyberattacks against federal systems have risen by more than 40%. Therefore, the need to understand and implement NIST 800-53 controls is no longer an option – it’s a requirement for any organization that deals with federal data, or that wants to do business with U.S. government agencies.
NIST has provided a risk management framework which provides a systematic approach to securing information systems. From there, it also helps organisations to build resilient defenses against cyber threats, natural disasters and human errors. This article takes a deep look at everything you need to know about NIST 800 53 compliance, from the basics to how to implement it.
Ready to strengthen your security posture? Contact Qualysec’s NIST compliance specialists to discover how we can help you navigate the complexities of NIST 800-53 implementation and achieve seamless compliance.
What is NIST 800 53 compliance, and why is it Important in Today’s Cybersecurity?
NIST 800 53 compliance is the compliance of security and privacy controls based on the National Institute of Standards and Technology (NIST) set by NIST. Essentially, this framework is an exhaustive listing of security measures that are meant to provide security to federal information systems and organizations. Furthermore, it covers the threats from cyberattacks to operational risks in the range.
The framework was originally published in 2005 in an effort to make it easier to comply with the Federal Information Security Management Act (FISMA). Since then, it has developed to a significant extent. Consequently, the current version, Revision 5, being released in September 2020, contains more than 1000 controls organized in 20 control families. Importantly, this revision removed the word “federal” for expanded use in industries.
According to the Cybersecurity and Infrastructure Security Agency (CISA), organizations implementing comprehensive security frameworks like NIST 800-53 experience significantly fewer successful breaches and faster incident recovery times.
Who Needs NIST 800 53 Compliance?
Federal IT compliance standards essentially require NIST 800-53 for:
- U.S. Federal Agencies: All Federal Agencies (except national security-related) have to comply within a year of publication.
- Cloud Service Providers (CSPs): Organizations that FedRAMP authorizes must follow these controls
- Federal Contractors: Companies working with government agencies have to comply with these security standards
- Defense Industrial Base (DIB): Organizations with Controlled Unclassified Information (CUI)
Nevertheless, numerous privately-run organizations are voluntarily adhering to this model. In fact, it is a good foundation to be in line with other compliance needs, e.g., HIPAA, PCI DSS and CMMC. Thus, any organization that processes various sensitive data enjoys the advantage of the implementation of NIST 800-53 controls.
Want to assess your current compliance status? Schedule a free consultation with Qualysec to evaluate your security posture against NIST standards.
Speak directly with Qualysec’s certified professionals to identify vulnerabilities before attackers do.
Nist 800-53 Controls – What Are the Ways to make them Effective by Organizations?
Implementation of NIST 800-53 controls should be a phased approach. Moreover, the organisations must be specific about the risk profile and the environment where they are operating in so as to be able to adapt the controls to their operational environment. The security control assessment process would verify that these controls are operating as it is supposed to.
Understanding the 20 Control Families
Controls are grouped into 20 families that cover particular security aspects in the following framework:
| Control Family | Focus Area | Key Purpose |
| Access Control (AC) | User permissions | Limits access based on least privilege principle |
| Awareness and Training (AT) | Security education | Ensures personnel understand risks and responsibilities |
| Audit and Accountability (AU) | Activity monitoring | Records system activities for incident detection |
| Assessment, Authorization, and Monitoring (CA) | System authorization | Ongoing assessment of security controls |
| Configuration Management (CM) | System integrity | Maintains secure configurations |
| Contingency Planning (CP) | Disaster recovery | Prepares for system interruptions |
| Identification and Authentication (IA) | User verification | Confirms user identity before access |
| Incident Response (IR) | Security incidents | Establishes response capabilities |
| Risk Assessment (RA) | Threat identification | Identifies and assesses organizational risks |
| System and Communications Protection (SC) | Network security | Protects information transmissions |
Three Implementation Approaches
Organizations have three different strategies for implementation to choose from:
1. Common Control Implementation
- Used across the organization in a universal manner
- Provides baseline security to multiple systems
- Managed in a centralized way by security teams
- Examples: security policies, physical protection and training programs
2. System-Specific Implementation
- Unique to individual information systems
- Deals with unique security requirements
- Responsibility is with system owners
- Examples include certain types of access control and encryption.
3. Hybrid Implementation
- Combines Common and system-specific elements
- Catering to universality as well as particularity
- Requires cooperation between the security team and system owners
- Examples include system-specific centralised patch management.
Furthermore, the inclusion of such approaches in your system development lifecycle improves effectiveness. As such, security is an inherent part from the beginning.
What Does a Complete NIST Compliance Checklist Include?
A detailed NIST compliance checklist helps organisations with the complex implementation process. Moreover, it ensures that no critical security measure is disregarded. The risk management framework provided by NIST follows a structured six-step process.
Essential Steps for NIST 800 53 Compliance
1: Assessment and Gap Analysis
- Start by carefully assessing existing security measures
- Compare existing practices with required controls
- Identify gaps in compliance
- Document policies and procedures
- Select specific controls to be assessed
2: Prioritisation and Planning
- Prioritise critical vulnerabilities
- Address the most important threats to the organisation
- Develop an implementation timeline
- Assign resources in a proper manner
Methodology: Follow NIST SP 800-30 Guide for Conducting Risk Assessments
3: Control Implementation
- Deploy controls using an appropriate approach (common, system-specific or hybrid)
- Document each control with clear procedures
- Establish operation & maintenance guidelines
- Make security part of the daily operations
4: Training and Awareness
- Hold full-staff educational sessions
- Discuss the importance of controls
- Define individual roles in the maintenance of compliance
- Produce an organisation-wide security culture
5: Continuous Monitoring and Assessment
- Implement automated monitoring solutions
- Conduct regular security control assessments
- Perform periodic vulnerability assessments
- Execute penetration testing for NIST 800-53 compliance
- Review and update controls based on evolving threats
- Track compliance metrics and KPIs
- Adapt to new NIST guidance and revisions
6: Documentation and Reporting
- Keep detailed records of compliance
- Document Risk Assessments and Implementations
- Maintain records of training and auditing results
- Prepare reports for stakeholders
- Provide proof of compliance status
In addition to NIST 800 53 compliance vulnerability assessments, NIST 800 53 compliance penetration testing is also an important task. Specifically, these activities identify the weaknesses before the attackers can exploit them.
Download our comprehensive pentest report to see how we identify vulnerabilities in NIST environments.
Download a Sample Pen Testing Report

Key Security Control Areas
Below are the areas of critical control that organisations have to handle:
- Access Control: Use multi-factor authentication (MFA) and role-based access control (RBAC).
- Network Security: Implement firewalls, Internet intrusion detector systems and segmentation of the network.
- Data Protection: Encourage rest and transit data encryption.
- Incident Response: Have official procedures of preparation, detection, containment, and recovery.
- Risk Assessment: Do periodic analysis through quantitative and qualitative analysis.
- System Integrity: Install anti-malware and prompt patching processes.
Need expert guidance on implementation? Download Qualysec’s comprehensive NIST 800-53 implementation guide to see detailed control implementation strategies.
How Does NIST Cybersecurity Framework Implementation Improve Your Security Posture?
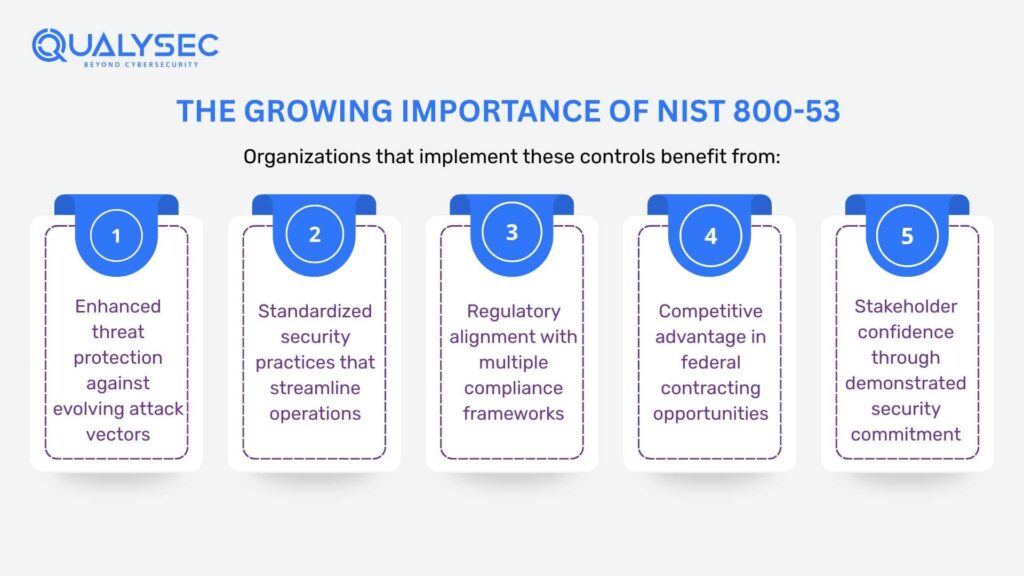
In addition to basic compliance, there are a lot of benefits derived from the NIST cybersecurity framework implementation. As a result, organisations can benefit from more secure operations and increased levels of efficiency.
Significant Value of NIST 800 53 Adoption
- Improved Security Posture: NIST 800-53 controls organisations offer significantly more defence against cyber attacks. Additionally, the framework encompasses contemporary assets, including IoT and IoT devices. Thus, full protection is extended to different system environments.
- Federal Market Access: This is achieved through compliance, which results in government contracts. Indeed, it usually becomes a prerequisite to conducting business with the federal government. In this way, organisations will have access to lucrative market opportunities.
- Detailed Risk Analysis: The Risk Management Framework by NIST facilitates the overall risk examination. In addition, it helps to establish standards of baseline security. Moreover, organisations will be able to shorten the maturity of the processes themselves in the long run.
- Trust and Credibility: Security is maintained through adherence to acceptable standards. Consequently, it builds trust amongst partners and customers. Thus, organisations enhance their image within the markets.
- Correlation with Other Standards: The breadth of it renders it central in other compliance standards. In particular, it is positively correlated with PCI DSS, CMMC, NIST 800-171, and ISO 27001. Multi-framework compliance is also made easier and quicker since compliance framework crosswalk software is available.
Tools and Resources for Success
To achieve compliance with NIST 800-53, the appropriate tools and resources are necessary:
- Automated compliance Software: Requirement translation to actionable requirements.
- Security Information and Event Management (SIEM): Monitoring and analysis in real-time.
- Configuration Management Database (CMDBs): Refers to approved configurations.
- Professional Consulting services: It is the advisory service of expertise throughout the compliance process.
- Training Programs: This involves training the employees on security best practices.
Tools should be selected depending on the dimensions and character of the organization and its current security posture. Also, solutions should be able to adapt to changing threats and regulations.
Why Qualysec Leads in NIST 800-53 Compliance Services
In terms of strong NIST 800 53 compliance, Qualysec is the top partner for organisations throughout the United States. In addition, their holistic approach balances technical expertise with a thorough understanding of federal IT compliance standards.
Unmatched Expertise in Federal Compliance
Qualysec has a long history of implementation of the risk management framework NIST and security control assessment. In addition to this, their team of certified security experts are well aware of the intricacies of government compliance requirements. As a result, they offer you solutions that are specially tailored to your specific needs.
- Comprehensive Vulnerability Assessment for NIST 800 53 Compliance: Finds security gaps across all 20 control families.
- Penetration Testing for NIST 800 53 Compliance: Simulates realistic attacks to test control efficacy
- Security Control Assessment: Assesses the implementation of all necessary controls
- Risk Assessment Services: Complete analysis using NIST methodologies
- Continuous Monitoring Solutions: Guarantees Continuous Compliance and Security
See our work in action: Download a sample Qualysec penetration testing report to understand our thorough methodology and actionable findings.
Why Organizations Choose Qualysec
- Proven Track Record: Qualysec has successfully assisted many federal agencies and contractors to meet NIST 800 53 compliance. In addition to that, their clients report a consistent increase in security posture and streamlined audit processes.
- Comprehensive Approach: Rather than focusing on compliance as a check-box exercise, Qualysec focuses on creating sustainable security programs. Further, they also integrate the implementation of the NIST cybersecurity framework into your current operations smoothly.
- Advanced Testing Methodologies: Their penetration testing for NIST 800 53 compliance is more than a simple scan. Specifically, they use sophisticated methods to find hidden vulnerabilities that are not found by automated tools. Thus, you get authentic assurance regarding the security posture.
- Customised Solutions: Every organisation has different challenges. As a result, Qualysec creates custom strategies to fit with your risk profile, business environment and compliance goals.
- Continuous Support: Compliance is not a destination, but a journey. Therefore, Qualysec offers ongoing compliance support to ensure that you are always compliant as threat and compliance standards change.
- Strategic Location and Accessibility: Qualysec is based in the USA and is aware of the particular compliance landscape that American organisations face. In addition, their staff is easily accessible to offer in-home evaluations and consultations throughout the country.
Schedule Your Free NIST Compliance Assessment with Qualysec →
- Assess your current compliance status
- Identify critical gaps and vulnerabilities
- Provide a customized roadmap to compliance
- Offer transparent pricing with no hidden costs
- Answer all your questions about the NIST framework
Conclusion
NIST 800 53 compliance is not just a compliance activity. Indeed, it creates a holistic foundation for safeguarding sensitive information and creating resilient information systems. In addition, the risk management framework offered by NIST allows organisations to approach the problem of cybersecurity systematically.
Implementing NIST 800-53 controls is not a simple task that requires commitment, resources and expertise. However, the investment is far outweighed by the benefits received, including improved security, federal market access and stakeholder trust. Additionally, the use of proper tools and working with experienced partners like Qualysec can make the whole process much easier.
Keep in mind that initial compliance is only the start. After that, organisations need to be constantly up for monitoring, assessment and updating. Therefore, the adoption of a good security culture and the ability to utilise automation tools become a key to long-term success.
Whether you are a federal agency, contractor or private organisation looking at ways to strengthen security, the NIST approach to implementing the framework is a proven roadmap for cybersecurity. Insufficient compliance with NIST now may cost your organisation money and could cost you your future.
Contact Qualysec today to begin your journey toward robust NIST 800 53 compliance and superior cybersecurity.
Frequently Asked Questions (FAQ)
Q. 1: What is Nist 800-53 and why is it important for Cybersecurity?
Ans: NIST 800-53 is a general framework for cybersecurity created by the National Institute of Standards and Technology that is in place to provide security and privacy controls for federal information systems and organizations. It is important for cybersecurity as it offers holistic guidelines on how to defend against a variety of threats, including cyber attacks, natural disasters, and human error, and it is the basis for federal compliance requirements, such as FISMA and FedRAMP.
Q. 2: How can organizations implement NIST 800-53 controls effectively?
NIST 800-53 controls can be implemented effectively by three means: common control implementation (common controls managed centrally), system-specific implementation (system-specific controls managed by system owner) and hybrid implementation (a mixture of the two managed together by security and system owners). In addition to these, organizations should conduct gap analyses, prioritise critical vulnerabilities, train staff and ensure that things are monitored for good implementation.
Q. 3: What are the main differences between NIST 800-53 and NIST CSF?
NIST 800-53 is an extensive catalogue of security controls, primarily for federal information systems, and contains more than 1,000 controls broken up into 20 families. The NIST Cybersecurity Framework (CSF) is a more flexible framework that is organised around 5 high level functions (Identify, Protect, Detect, Respond, Recover) and is more general and simpler than the other frameworks, so it is likely to be a good choice for organisations of any size and sector.
Q. 4: How does NIST 800-53 help meet federal and industry compliance standards?
NIST 800-53 is utilized to comply with federal compliance standards and industry compliance standards as the basis for compliance requirements for FISMA and security standards for federal contractors and cloud service providers as FedRAMP. Its comprehensive nature also means it’s workable for adherence to many other compliance requirements such as HIPAA, PCI DSS and CMMC, so organisations can align a number of compliance efforts through framework crosswalking.











































































































































































































































































































































































































































































































































































































































































































0 Comments