The ever-increasing costs incurred by organizations due to data breaches emphasize the need for reliable and efficient cybersecurity posture assessment. Businesses can no longer afford to rely on assumptions about their resilience.
Evolved threats leveraging AI for malicious attacks further drill down the need to conduct a security posture assessment. With this report, businesses can assess their readiness to defend against, detect, and recover from cyber threats.
In this guide, we provide a complete walkthrough of what a cybersecurity posture assessment involves, the step-by-step process, and a practical checklist.
What is a Cybersecurity Posture Assessment?
A cybersecurity posture assessment is a detailed evaluation of an organization’s overall security. Unlike a one-time penetration test or vulnerability scan, it provides a 360-degree view of the systems, policies, technologies, and people that make up your defense strategy.
The cybersecurity posture assessment measures:
- Preventive strength – how well your defenses can block attacks.
- Detection capability – how quickly your systems and teams can identify a threat.
- Response plan – how efficiently the business counters the attack and ensures everything is safe.
Test Your Security With Qualysec, Contact today!
Is Cybersecurity Posture Assessment Essential?
In today’s world, the question isn’t if you need a cybersecurity posture assessment. It’s more about how quickly you can get one done and ensure it is conducted at regular intervals.
Here’s why cybersecurity posture assessment is extremely important:
– Increasing Threats
Every new SaaS platform, connected endpoint, and API increases exposure. A posture assessment ensures visibility across this sprawling digital ecosystem. Without it, blind spots multiply and adversaries exploit them first.
– Alignment With Compliance Standards
One of the main reasons why a security posture assessment is absolutely essential is that it helps your business maintain compliance standards. For instance, companies in the USA face strict regulations from HIPAA< CCPA, PCI DSS, and more. If you fail to comply with and document your security, it can lead to severe financial losses for your company.
– Business Reputation
When your business handles sensitive data, protecting it at all costs is crucial. A well-documented assessment ensures you can store and protect data effectively for your customers. It also helps in boosting your reputation and gives you a competitive edge over others.
– Risk Prioritization and Budget Justification
Investing in cybersecurity is no longer optional. However, the pressure to justify the allocated budget remains. Here, a detailed security posture assessment can help a great deal. It explains the gaps, their severity, the impact of the risk on the business, and why investing is necessary. This evidence makes budget conversations with boards and executives far more effective.
Challenges of Cybersecurity Posture Assessment
Opting for a cybersecurity posture assessment is only the first step. That is not the end of the road. Implementation of the fixes and ensuring that the gaps do not exist anymore is far more challenging.
Take a look at these common challenges and why they matter:
1. Different Systems
Nowadays, businesses use a wide variety of systems. These include cloud, third-party, IoT, remote workers, etc. No matter the time or money needed, all of these assets need to be mapped with absolute clarity. Gaps here leave hidden vulnerabilities unassessed.
2. Lack of Resources and Expertise
To conduct an effective security posture assessment, time and expertise are of great importance. You cannot really hurry the process and get it done anyhow. Proper knowledge of the process and accuracy remains key while making the evaluations.
3. Outdated Tools
Sometimes, tools are not advanced enough to produce the results that are needed for the assessment. In other cases, the automated scanners do help, but the volume of the alerts requires human analysis. Without clear priorities, the team is likely to struggle with decision-making, leading to delays in addressing critical issues.
4. Not Understanding the Process
Some organizations treat posture assessments as one-off exercises for compliance checkboxes. It is important to understand that the process has to be continuous and done at regular intervals.
Read more about top cybersecurity services for 2025!
Steps for Cybersecurity Posture Assessment
It is critical to make sure that the cybersecurity posture assessment follows a systematic process.
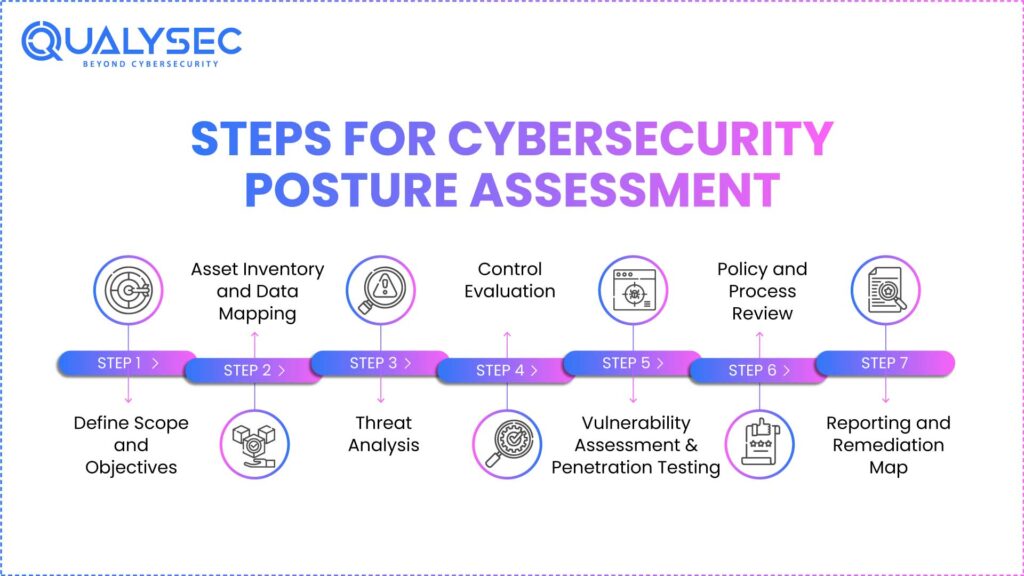
Take a look at the structured approach we follow:
1. Define Scope and Objectives
The first step is to identify the objective and what needs to be done. For this, it is important to know what systems, networks, and data to analyze. After that, it is critical to ensure that the objective aligns with the priorities of the business. If the scope is not clearly defined, the security posture assessment can become wasteful.
2. Asset Inventory and Data Mapping
List every device, endpoint, application, and third-party service. Then, map data flows to understand how sensitive information moves across the organization. This step prevents the common pitfall of leaving shadow IT or cloud instances unassessed.
3. Threat Analysis
Use real-time intelligence to identify active threats relevant to your industry and infrastructure. Tailoring assessments to your threat model maximizes accuracy.
4. Control Evaluation
In this step, a complete evaluation of the security controls is done. These include assessing firewalls, identity and access management, endpoint protection, encryption, and other security measures. This step highlights gaps between policy and execution.
5. Vulnerability Assessment and Penetration Testing
Automated scans help in exposing common gaps. After that, it is necessary to conduct penetration testing to test the security posture in real-world scenarios.
6. Policy and Process Review
Strong technology controls fail without effective policies. Review governance documents, incident response procedures, employee training programs, and vendor risk management practices.
7. Reporting and Remediation Map
It is important to present the findings in a detailed report. The report must clearly explain the risks and possible fixes. Moreover, it is critical to build an efficient roadmap outlining long-term plans and quick fixes.
Schedule a Posture Assessment Call With Our Experts.
Our experts at Qualysec have helped secure fintech, SaaS, and enterprise systems across 25+ countries. Manual + Automated Pentesting. No false positives. Actionable reports.

Cybersecurity Posture Assessment Checklist:
Having a security posture assessment checklist is handy. When you have the checklist ready, you can jump to execution right away.
Take a look at this security posture assessment checklist:
- Identify and classify assets: Create an exhaustive inventory of all devices, applications, data repositories, and cloud services. It is important to assign classification levels for smooth assessment.
- Data flows: One of the most crucial aspects to consider in a security posture assessment checklist is the flow of data and its tracking. You need to know how and where the data is stored, the transmission process, and people who can access it.
- User access controls: It is important to give access only to people who need it. Giving unnecessary access can result in massive security concerns.
- Cloud security: One of the most common causes of data leakage is cloud misconfigurations. That is why experts need to review encryption, IAM roles, API security, and more.
- Vulnerability scans and pen testing: A hybrid approach combining automated scans and manual testing is a great idea. Regular pen testing is needed to ensure the system is secure.
- Audit third-party risks: It is critical to ensure that third-party contracts, security practices, and other relevant agreements are perfectly secure. External risks can cause massive security breaches.
- Checking all access points: Another important thing to check is to analyze all the potential access points. Missing any one of them can lead to massive security gaps.
- Compliance maintenance: Businesses need to maintain compliance depending on the industry. If your organization doesn’t comply with the standards, it can face hefty fines.
- Security training: Simply conducting an assessment is not enough. All the team members across various departments need to be aware of the security protocols. That’s the only way to ensure your system remains safe.
- Resolutions: After the assessment is done, potential fixes are listed. That needs to be done immediately to close the gaps as soon as possible.
- Remediation Map: It is also important to create a remediation plan. In case an attack occurs, the business should be prepared to counteract it smoothly.
Conclusion
A cybersecurity posture assessment is not merely a technical scan. It is much more than that – it’s a strategic move. By systematically reviewing assets, risks, and controls, organizations can ensure complete security. That way, you can create a robust security framework and reduce exposure to different risks. It also helps in establishing customer trust and boosting market reputation.
At Qualysec, we deliver tailored assessments that uncover blind spots before attackers exploit them. Our team ensures organizations are not just audit-ready but equipped to combat real-world attacks.
Request Your Cybersecurity Posture Assessment Today.
Talk to our Cybersecurity Expert to discuss your specific needs and how we can help your business.
FAQs:
Q: What is a cybersecurity posture assessment, and why is it important?
A cybersecurity posture assessment is a detailed check of the overall security of the business.
This is important as it helps businesses identify their strengths and weaknesses. It also helps to work on fixes that are essential and reduce devastating cyber attacks.
Q: How can organizations identify gaps in their current cybersecurity posture?
Organizations can identify gaps in their current cybersecurity posture by conducting assessments, penetration tests, vulnerability scans, and other similar security evaluations.
Q: What tools or frameworks are recommended for conducting a posture assessment?
Some of the frameworks that are highly recommended for conducting a cybersecurity posture assessment are ISO 27001, NIST cybersecurity framework, CIS controls, etc.











































































































































































































































































































































































































































































































































































































































































































0 Comments