Web apps in the USA are under a new threat: the investment in cybersecurity of businesses went up by 15 percent in 2025, which signals the pressure to protect the digital ones. Web-facing surfaces become operationally important, firms in industries such as e-commerce, financial, SaaS, and healthcare organisations are turning to pen testing vendors to help them fend off such advanced attacks.
Assured penetration testing vendors assist in simulating actual-world threats and in securing weaknesses in log-in procedures, APIs, and third-party combinations. When dealing with companies that fall under regulations such as PCI DSS or HIPAA, knowing the weakness as effectively as possible, in advance, means that they will be in the clear as far as compliance goes, and that the reaction to the weakness will instill customer confidence in the company.
Want experts to uncover hidden risks before it’s too late? Start with a free security audit today.
Who Are Pen Testing Vendors?
Pen testing vendors are niche cybersecurity companies or service providers who complete a simulated cyberattack called penetration testing to test the security of your IT systems, applications, networks, or cloud environments.
They have the mission to discover weaknesses before they are exploited by actual hackers and assist a company in reinforcing its security.
What Do Pen Testing Vendors Do?
Here’s what typical penetration testing vendors offer:
- Network Penetration Testing: Locates vulnerabilities in its internal and external network
- Web & Mobile App Testing: Tracks and simulates the attack of websites and applications, and exposes code or logic weaknesses
- Cloud Penetration Testing: Exercises the cloud security position of the platform, such as AWS, Azure, or Google Cloud
- IoT & Embedded Device Testing: Tests smart devices, sensors, and firmware to identify unstable points
- Wireless Network Testing: Checks problems in WiFi access points, encryption, or rogue access devices access
- Social Engineering Attacks: established phishing simulates to exploit human susceptibility
Learn how Qualysec simulates real-world attacks to protect your web, mobile, cloud, and APIs. Explore our comprehensive penetration testing services.
Common Features Offered by Top Pen Testing Vendors
- Professionally qualified testers (for example, OSCP, CEH, CREST)
- Making up a custom scope and methodology
- Manual and automated testing
- Risk rating and correction reporting, Faster remediation reporting
- Penetration Testing as a Service (PTaaS) access platform
Why Organizations Use Pen Testing Vendors
- Pass various compliance (PCI DSS, SOC 2, HIPAA, ISO 27001)
- Avoid data leakages
- Exploitability of real-world vulnerabilities
- Sustainable development/deployment assurance
- Obtain outside, impartial protection analysis
Why Choosing the Right Pen Testing Vendor Matters
Not all pen testing vendors are created equal. The difference between a skilled team and an underqualified provider can determine whether your business detects critical vulnerabilities in time or becomes the next breach headline.
Here’s why choosing the right penetration testing vendor is crucial:
1. Expertise and Domain Focus
The vendors usually focus on various forms of testing. Selecting one that matches your infrastructure would make the test more precise and effective.
- Cloud Security: AWS, Azure Websites, and Google Cloud environment
- Web app security: Custom portals, SaaS, APIs
- Testing mobile application: iOS and Android
- IoT & embedded systems: Embedded systems, hardware testing
- Enterprise networks: Prem-working, hybrid, and remote workforce architectures
2. Industry Certifications
Reliable best pen testing vendors are usually the ones who are certified and are considered competent technically as well as ethically. Look for:
- Quality CREST-certified business on a global grounds
- Respectively, OSCP or OSCE-certified testers in practical exploitation skillsets
- Data security and testing governance certification firms are ISO 27001-certified
3. Modern Delivery with PTaaS
Penetration Testing as a Service (PTaaS) is transforming the way business organizations are consuming security tests. This method is a hybrid one that integrates conventional pentesting with:
- Ongoing analysis of vulnerability
- Instant dashboards
- Integration with the testers within ticketing systems
- More rapid remediation sets with DevSecOps incorporated
PTaaS enables security teams to stop one-off tests and adopt an agile and iterative approach.
4. Compliance and Business Impact
Using the wrong vendor is not only a worry about your security:
- Audit failures: An Ineffective testing approach would not satisfy PCI DSS, SOC 2, and HIPAA controls
- False negative: Important problems become unnoticeable
- Generic reports: Support without contexts may slow down the remediation
- Liability risks: Mismanaged tests will lead to an outage or a violation of SLAs
As a startup or a regulated business, the decision to choose the correct provider to assist in the penetration testing exercise is one of the security decisions that affect your brand, uptime, and legality.
Want testing that’s continuous and ticket-integrated? Check out Qualysec’s PTaaS model built for agile security teams. Learn more about PTaaS here.
Key Evaluation Criteria for Top Pen Testing Vendors
After knowing what pen testing vendors are doing and why it is important to make the correct decision, the next question you should know is the way of dealing with them. In addition to domain knowledge and certification, the following are other important aspects that divide the top tier and others:
1. Cross-Industry Experience:
The leading vendors are used to working in any industry, such as fintech, e-commerce, healthcare, SaaS, and government, among others. This is important because every line of business possesses individual data processing threats and regulatory requirements.
2. Comprehensive Testing Methodology:
Powerful vendors do more than simple scans. They also combine manual penetration tests with automation and are based on a set of structured frameworks such as OWASP, MITRE ATT&CK, or NIST 800-115 in their coverage.
3. Compliance Mapping and Documentation:
Compliant Vendors whose finding meets these regulatory requirements give you an easier time during an audit. They are supposed to have distinct evidence trails of controls associated with either PCI DSS, HIPAA, SOC 2, ISO 27001, or FedRAMP.
4. Credible Team Credentials:
It is one thing to have certifications, but another to use them. Search not only teams with offensive security certifications (OSCP, GPEN, CRT) but also those with platforms specific to skills and knowledge (AWS Certified Security, Google Cloud Security Engineer).
5. Reporting Maturity:
Leading vendors do not only give a list of findings. Seek well-organized risk ratings, remediation recommendations that apply to your stack, graphical proof-of-concept when applicable, and summarized executive plans.
6. Post-Engagement Support:
Respectable vendors will support you after the test; they explain the findings, assist with remediation prioritization, and retest after remediation. This makes sure security improvements are indeed vindicated.
7. U.S. Operational Presence:
In instances when an organization is headquartered in the United States, having a vendor with U.S.-based support/operations can help with legal, compliance, and time-slotted cooperation.
Need testing that aligns with HIPAA, PCI DSS, SOC 2, or ISO 27001? See how Qualysec maps every finding to compliance standards.
Top 15 Pen Testing Vendors in the USA (2025 Edition)
After evaluating dozens of providers across technical capability, industry focus, compliance readiness, and post-test support, here are the top penetration testing vendors trusted by U.S. businesses in 2025:
1. Qualysec
Headquarters: Global Presence
Best For: Startups, SMEs, and compliance-focused enterprises
Why Qualysec ranks #1 in 2025: Qualysec is a hybrid manual plus automated pen testing company providing deep-level assessments on web, mobile, cloud, and API. As the company is capable of implementing PTaaS delivery in combination with compliance-first approaches, Qualysec provides vulnerability mapping against such frameworks as PCI DSS, SOC 2, HIPAA, and ISO 27001.
What sets Qualysec apart:
- Certified ethical hacker (OSCP, CEH, CREST-aligned)
- Large-scale GCP, AWS, and Azure testing (GCP pentesting)
- The reproduction steps describe and score risks
- Free Retest and audit aids
- Real-time dashboard and ticket-based collaboration with PTaaS access
- U.S. support availability and 24/7 turnaround for critical findings
See how Qualysec goes beyond standard testing by providing cloud, mobile, IoT, and network assessments, all mapped to compliance. Get a detailed scope of the solutions we offer.
Our experts at Qualysec have helped secure fintech, SaaS, and enterprise systems across 25+ countries. Manual + Automated Pentesting. No false positives. Actionable reports.

2. Rapid7
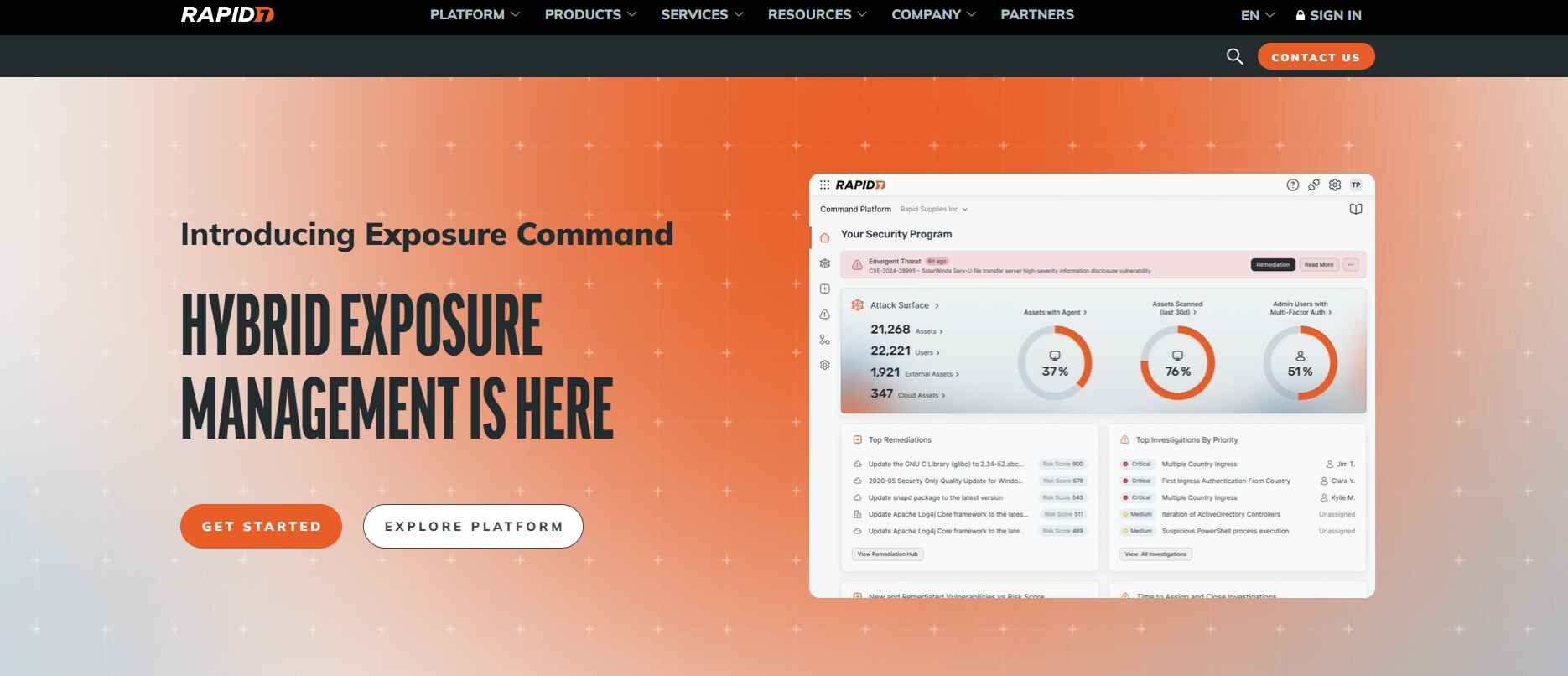
- Based in Boston, MA
- Offers InsightAppSec and Metasploit tools
- Strong in hybrid cloud and network security
- Suitable for large enterprises
3. Synack
- Headquartered in Redwood City, CA
- Crowdsourced penetration testing via vetted ethical hackers
- Combines AI with human-led testing
- Real-time vulnerability insights
4. Coalfire
- Based in Westminster, CO
- Specializes in compliance-driven testing (FedRAMP, HIPAA, PCI)
- Offers red team and cloud assessments
- Works with federal and enterprise clients
5. Cobalt
- San Francisco-based PTaaS provider
- On-demand testing via its Pentest as a Service platform
- Ideal for agile SaaS teams
- Offers tester collaboration and fast reporting
6. NetSPI
- Headquartered in Minneapolis, MN
- Focused on enterprise security and CI/CD pipeline testing
- Provides advanced manual assessments
- Offers Attack Surface Management (ASM)
7. Bishop Fox
- Based in Tempe, AZ
- Red teaming, application pentests, and cloud testing
- Clients include Fortune 100 companies
- Known for its continuous security testing model
8. CrowdStrike
- Located in Austin, TX
- Integrates threat intelligence with penetration testing
- Strong in endpoint and cloud security
- Supports proactive threat hunting
9. Trellix
- Based in California, United States.
- Focused on PCI-DSS, HIPAA, and PII compliance
- Offers network, application, and wireless pentests
- Tailored for healthcare and retail
10. Trustwave SpiderLabs
- Headquartered in Chicago, IL
- Offers ethical hacking and forensics
- Deep experience in the financial and e-commerce sectors
- Includes vulnerability management services
11. A-LIGN
- Based in Tampa, FL
- Offers penetration testing aligned with SOC 2, ISO 27001
- Works closely with mid-market businesses
- Strong in audit-ready reporting
12. TestBytes
- Located in NY, USA
- Specializes in social engineering and wireless testing
- Offers physical security assessments
- Works with both the public and private sectors
13. Qualitest
- Based in FL, USA
- Offers advanced cyber security testing
- Known for hands-on, highly technical assessments
- Best for high-security environments
14. CyberDuo

- Located in California
- Offers managed IT security services including pen testing
- Help organizations secure their resources and data
- Strong in endpoint protection and incident response
15. Veracode

- AppSec platform with integrated pentesting
- Supports DevSecOps through automation
- Good for code scanning plus manual validation
- Suited for software development teams
Latest Penetration Testing Report

Benefits of Using U.S.-Based Pen Testing Vendors
In the case of organizations that are located in the United States, the choice of a local penetration testing provider can facilitate operational as well as compliance processes. Such vendors are familiar with the environment of cybersecurity in the place, and they are better suited to the legal, logistics, and regulatory requirements.
Here’s why the U.S.-based vendors are often preferred:
- Stronger compliance alignment: The domestic providers are more conversant with the regulatory requirements specific to the region, including CMMC, FedRAMP, and GLBA. This helps in scoping and implementation of testing, keeping these frameworks in consideration, and thus reducing any loopholes that the foreign providers may miss.
- Data residency assurance: The vendors are usually U.S.-based and store data in the country. This constrains jurisdictional issues and backs organizations that are subject to local data sovereignty and breach notification requirements.
- Time zone compatibility: When working with similar time zones, there is a possibility to move swiftly when in the active testing, reporting, and retesting cycles. Teams have an opportunity to work without delays that originate from the geographic dispersion.
- Faster service level commitments: Service level commitments provided by domestic providers are frequently limited to a short response time and identifiable escalation processes when high-risk findings occur or emergency revalidations are required.
Such advantages justify the U.S. based penetration testing vendors in offering strategic solutions to industries that seek efficiency in operations, quicker turnaround around and assurance of compliance with regulations.
Need a proven partner to secure your business against modern threats? Talk to Qualysec’s certified ethical hackers today.
Common Mistakes to Avoid When Hiring Pen Testing Vendors
Avoiding these missteps helps you get real value from your penetration testing engagement and ensures your security investments translate into measurable risk reduction.
You will find a solution with a compliance-checking mark, and this does not point only to the choice of the penetration testing vendor. Your test needs to be of quality and effectiveness based on the structure of your engagement and with whom you engage. The following are some of the common pitfalls that companies make when selecting a vendor, and the way to overcome the pitfalls:
Choosing based only on price:
The low-cost vendors might reduce their costs by utilizing only automated tools, recycling standards, or more complex, manual testing. Attend the approach followed by the vendor, and their credentials as a team, and how they fit into your environment.
No clear scope definition:
Not defining the scope tightly enough or not defining the scope at all may lead to someone obtaining nothing or overlooking a vulnerability of importance. Before signing off, formally specify the specific systems, endpoints, and data flows in scope, and ensure that testing boundaries will be observed.
Not asking for manual validation:
Manual validation in the real world reveals itself as cumbersome to work out, but effective. Ensure your vendor performs manual testing, which would identify logic defects, chain attacks, and business-related exposure that automated scanning equipment is unable to identify.
Ignoring post-assessment support:
A test report should not be the finish of the ‘interaction’. Make sure that the vendor provides remediation advice, clarification telephone calls, as well as retesting. Without this assistance, your internal teams might not prioritize or appropriately resolve vital findings.
These pitfalls can be evaded so that you can derive genuine worth out of your penetration testing engagement, and so that your security investment yields prior organizational risk reduction.
Explore how Qualysec helps U.S. businesses identify hidden vulnerabilities with real-time dashboards and deep-dive assessments.
Final Thoughts
Since the cybersecurity environment evolves in the USA and is becoming highly regulated, selecting an appropriate penetration testing vendor is no longer an option. It is a choice that influences your regulatory status, customer confidence, and the ability to resist the threat in the real world. In case you are a fintech startup, a SaaS company, or a healthcare provider, your security posture should change accordingly with the threats facing your digital resources.
When qualifying the vendors, do not just stop at what is on the surface. Those teams that provide manual validation or contextual risk reporting and post-assessment services should be prioritized. The objective is not only to score a point but to find relevant weaknesses and plug these before the attacks.
In case you require a vendor with technical expertise and an approach of compliance first, Qualysec has already become a reliable option in 2025. Not only do they provide testing with their unique hybrid manual plus automated testing model, U.S. support coverage, and dedication to such frameworks as PCI DSS, HIPAA, and SOC 2. They provide security.
Ready to take security seriously? Partner with Qualysec for a consultation that uncovers real risks and real solutions. Start your consultation now!
Talk to our Cybersecurity Expert to discuss your specific needs and how we can help your business.
FAQ
Q: What is the difference between a penetration test and a vulnerability scan?
Ans: A vulnerability scan is machine-based and determines the known vulnerabilities within systems. Penetration test is a set of manual methods that are in to study the actual risk status of a vulnerability, the consequences of this problem, and understand whether one can be subject to the risk of unauthorized access or not.
Q: How much does a penetration test cost in the USA?
Ans: It will cost between 5,000 to 100,000, depending on the scope, type of the test (web, network, cloud, mobile), and whether retesting and reporting are the same. The mid-sized companies usually invest between 15,000 and 40,000 dollars per engagement.
Q: How long does a typical pen test take?
Ans: 1 to 4 weeks is the approximate time of most penetration tests. That is determined by how complex your environment is, how many systems fall within the scope, and whether you are considering manual testing.
Q: Do I need a pen test for compliance (PCI DSS, HIPAA, SOC 2)?
Ans: Yes. Periodic penetration tests are a major requirement of most regulatory frameworks. PCI DSS needs to be tested once a year, HIPAA demands a risk assessment, which may involve pen testing, and SOC 2 usually involves it in reviews of control effectiveness.
Q: What is PTaaS (Penetration Testing as a Service)?
Ans: PTaaS is a new-fangled process that unites classical pen testing with a SaaS-like experience. It provides real-time dashboards, persistent monitoring of vulnerabilities, and easier cooperation of your team and testers using the platform.
Q: What should I expect to see in a good penetration test report?
Ans: A good report contains an executive summary, finer technical reporting, ranking of risks, proof-of-concept findings, suggestions on remedial action, and gaps against compliance requirements. Some vendors provide retesting verification after fixing.











































































































































































































































































































































































































































































































































































































































































































0 Comments