Key Takeaways
- CTEM (Continuous Threat Exposure Management) is a Gartner framework with five stages that run in a loop.
- It goes beyond CVE-based scanning to cover misconfigurations, identity risks, and credential leaks.
- Threat exposure management ties every finding to business context and impact.
- Only 16% of organisations have fully implemented a CTEM program as of 2026.
- Cyber exposure management helps meet compliance goals under ISO 27001, PCI DSS, and HIPAA.
- Combining CTEM security with penetration testing creates the strongest defence posture.
Introduction
CTEM (Continuous Threat Exposure Management) is a five-level security model designed by Gartner. It aids organisations in locating, ranking, verifying and remediating security exposures on an ongoing basis. In comparison to traditional scanning, continuous threat exposure management is a continuous process that links the technical risks to actual business impact.
The majority of businesses continue to use periodic vulnerability scans. Nevertheless, these scans tend to overlook the things that are important. According to Gartner, in 2026, the likelihood of a breach occurring in a company that has a continuous threat exposure management program will be three times lower (Gartner). This is a good reason to learn about what CTEM is and how it functions.
The average price of a data breach in the world was USD 4.44 million in 2025 (IBM Cost of a Data Breach Report). In the meantime, in 2025, 61% of the vulnerabilities used were weaponised within 48 hours of disclosure (Vectra AI). Quarterly scans are just too slow to do this. CTEM security fills this gap by ensuring it runs continuously and is dynamically adjusted.
What Are the 5 Stages of CTEM?
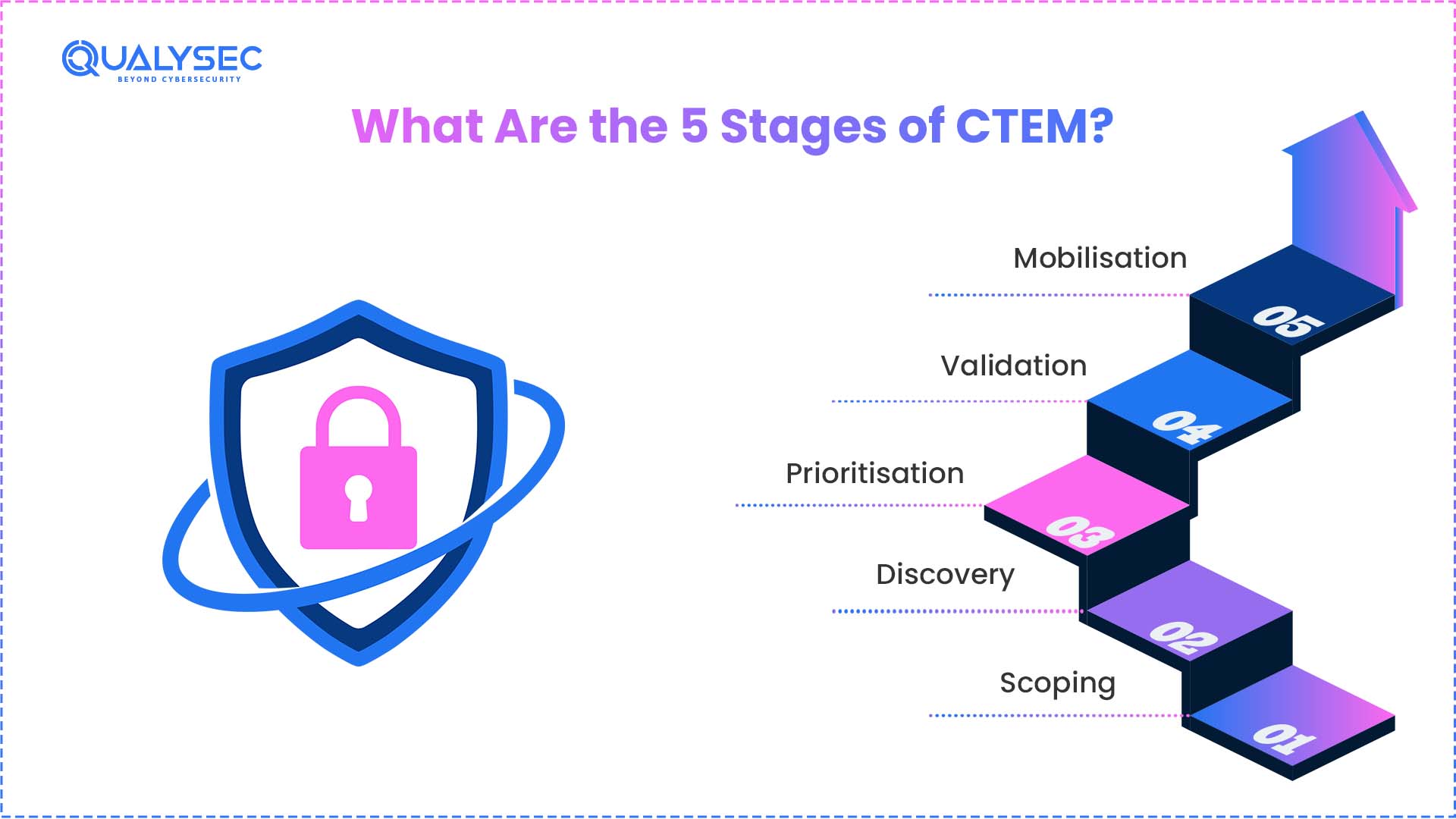
The CTEM (Continuous Threat Exposure Management) model is based on five steps. One stage is founded on the other. They all create a circle that keeps on repeating. It is this continued loop that makes the CTEM powerful over single-time measurements. This is the operation of each stage.
Stage 1: Scoping
This phase determines what is to be safeguarded. Teams determine the business assets and processes that are of utmost importance. It looks beyond conventional IT resources. It consists of cloud workloads, SaaS applications, APIs, and even social media accounts. Here begins threat exposure management of aligning security objectives with business priorities.
Stage 2: Discovery
In this phase, all exposures within the given scope are discovered by the teams. It contains well-known vulnerabilities, misconfigurations, weak credentials and identity risks. Continuous threat exposure management relies on automated tools and manual analysis. It is aimed to map the entire surface that can be exploited (Palo Alto Networks).
Stage 3: Prioritisation
All exposures are not equally harmful. This phase prioritises findings in terms of business impact and exploitability. A vulnerability that is a critical issue in a payment gateway is more important than a low-risk issue in an internal test server. This ranking is informed by CTEM based on business context. This is what makes it different from simple vulnerability scoring.
Stage 4: Validation
Teams now determine whether or not the identified exposures are actually exploitable. This includes simulated tests, breach and attack simulation and penetration testing. CTEM security applies validation to validate real risk and reject false positives. In the absence of this step, teams will end up wasting time on things which are irrelevant.
Stage 5: Mobilisation
The last step transforms discoveries into practice. Teams liaise between security, IT and development to rectify known problems. Stakeholders are provided with the information on threat exposure in clear language. It is concerned with seamless remediation processes, rather than automated patching (SentinelOne).
The cycle re-initiates after mobilisation. This is what renders CTEM a continuum. The rounds enhance the overall security posture of the organisation.
Get a Free Sample Pentest Report

How Is CTEM Different From Traditional Vulnerability Management?
The most common question raised by many teams is what CTEM is and how it compares to their current practice. The gap is huge. Conventional vulnerability management is primarily concerned with the identification of CVEs by periodical scan. Continuous Threat Exposure Management is an area that encompasses a far wider spectrum of hazards.
Here is a clear comparison:
| Feature | Traditional Vulnerability Management | CTEM (Continuous Threat Exposure Management) |
| Scope | Known CVEs and software flaws | CVEs, misconfigurations, identity risks, credential leaks, and shadow IT |
| Frequency | Periodic (quarterly or annual) | Continuous and ongoing |
| Prioritization | CVSS score-based | Business impact and exploitability-based |
| Validation | Rarely included | Built-in through simulations and testing |
| Remediation | Patch and move on | Coordinated mobilization across teams |
| Business alignment | Minimal | Central to the framework |
Non-technical risks are also a part of cyber exposure management via CTEM. A leaked employee credential on the dark web is not a CVE, for example. Nonetheless, exposure is a severe threat that might result in a breach. Conventional scanners would not detect it. Similarly, ongoing threat exposure management alone can resolve blind spots such as shadow IT assets and lost cloud instances.
According to industry surveys, 71% of organisations might be benefiting from CTEM. However, 16% have fully implemented it by 2026 (Vectra AI). This vulnerability is a threat and an opportunity to the security teams across the world.
Schedule a Free Consultation — Contact Qualysec Now
What Is the Difference Between CTEM and SIEM?
It is a frequent question since the two are dealing with security threats. Nevertheless, they are used for different ends.
CTEM is a proactive model. It locates and corrects exposures before exploitation. Continuous threat exposure management views outwardly to what might go wrong and acts to avert it.
SIEM (Security Information and Event Management) is a responsive tool. It gathers and examines post-event logs and alerts. SIEM assists in the identification of current incidents and aids in investigations.
Consider it in this manner. CTEM security poses the question: Where are we vulnerable at this point? SIEM poses the question, What just happened in our environment? Both are required, yet they operate at different stages of the security lifecycle.s
Those organisations that integrate CTEM and SIEM achieve the most. Incidents are avoided by threat exposure management. SIEM intercepts the slip. They combine to create a multi-layered defence that operates 24/7.
What Is the Difference Between ASM and CTEM?
Attack Surface Management (ASM) and CTEM are two related terms. But ASM is not the only component of the CTEM cycle.
ASM concentrates on the discovery. It scans external assets such as domains, IPs, APIs and cloud services. ASM tools are constantly searching for new assets and modifications in the external surface.
CTEM (Continuous Threat Exposure Management) uses ASM during the discovery phase. But it is more than that. CTEM also covers:
- Prioritisation based on business risk, not just technical severity.
- Validation through testing and simulations.
- Mobilisation to coordinate remediation across teams.
- Internal threat exposure, like identity risks and misconfigurations.
Simply put, ASM informs you of what is exposed. Continuous threat exposure management will inform you on what to fix and ensure that the fix works. Both are required in cyber exposure management, and CTEM offers the entire lifecycle (CTEM.org).
Why Should Organisations Adopt CTEM Security in 2026?
The threat scene continues to evolve. Every day, new vulnerabilities emerge. AI-driven threats are increasing rapidly. Organisations cannot rely on periodic evaluations in this environment. Herein lies the reason why CTEM security is more crucial than ever before.
- The rate of exploitation is increasing. In 2025, more than 61% of the vulnerabilities had been weaponised in less than 48 hours. The management of threat exposure is at this pace.
- Breach costs are climbing. In 2025, the average breach cost in the world was USD 4.44 million. Proactive threat exposure management mitigates this financial risk.
- Compliance requirements are tightening. The current security validation is a requirement in frameworks such as PCI DSS 4.0, HIPAA, and the EU-based NIS2 directive. CTEM helps in these requirements.
- Traditional tools leave gaps. Scanners do not detect business logic errors, identity risks, and shadow IT.CTEM cyber exposure management addresses these blind spots.
In 2023, CTEM was declared by Gartner as one of the top cybersecurity trends. In 2025, Gartner released its first exposure assessment platform, Magic Quadrant. This indicates that the industry acknowledges CTEM as one of the fundamental security program requirements in contemporary security programs.
This approach is useful in organisations in the fintech, healthcare, SaaS, and government sectors. The exposure to threats within these industries is more weighty because of sensitive information and stringent rules. Implementing CTEM security today will equip your organisation against tomorrow’s threats. All security teams are supposed to know what CTEM is and how to implement it within their environment.
Why Is Qualysec the Best Partner for CTEM Implementation?
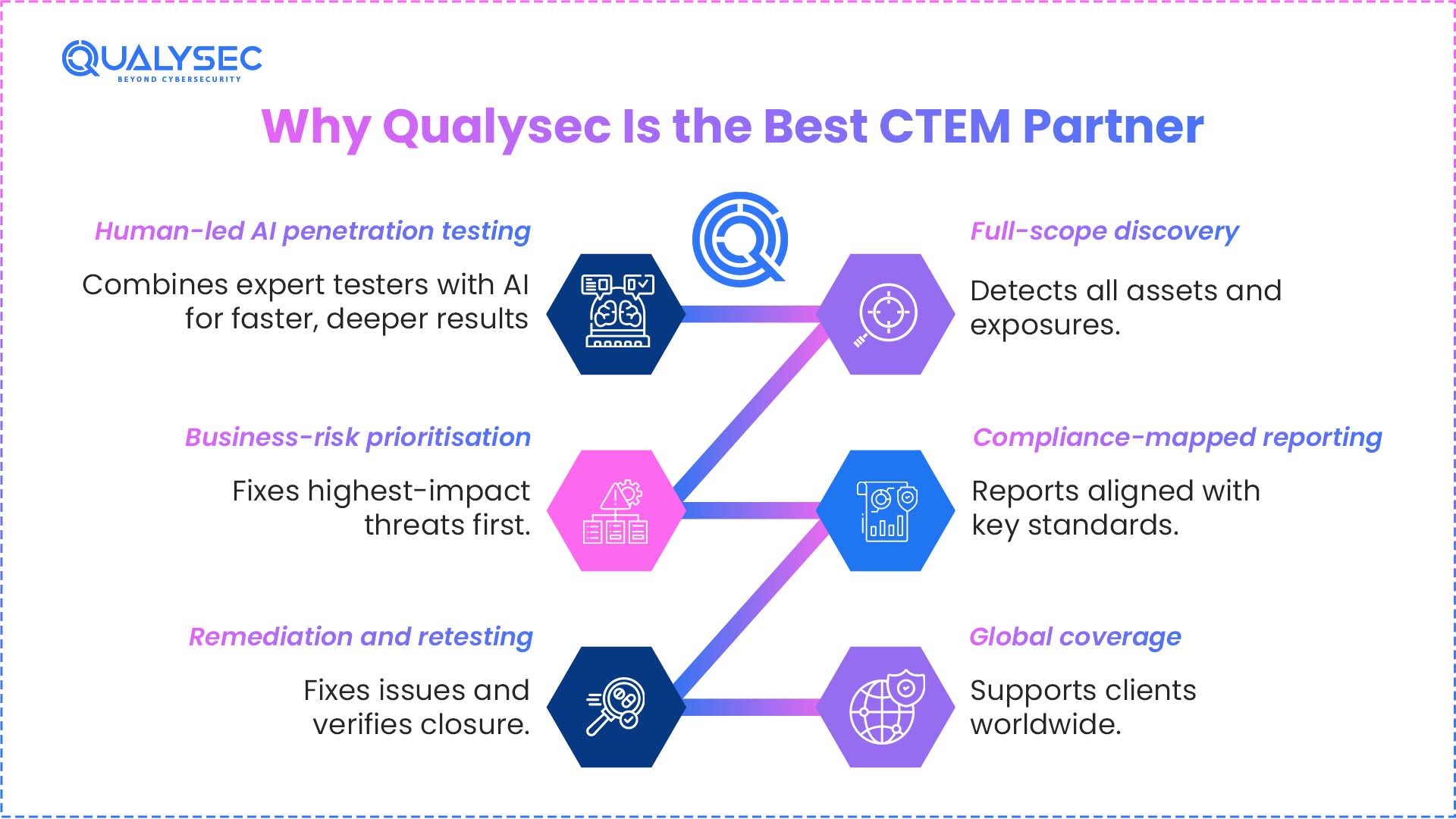
Qualysec assists the organisations in developing and executing powerful CTEM (Continuous Threat Exposure Management) programs.The company integrates expert-led with formal processes, which are aligned to the five stages of CTEM.
What makes Qualysec stand out:
- Human-led AI-powered penetration testing. The testers at Qualysec test exposures by performing human-led AI testing. This aids the validation phase of CTEM and makes it real-world accurate.
- Full-scope discovery. The team evaluates web applications, APIs, cloud environments, mobile applications, and network infrastructure. This involves the discovery phase of the end-to-end continuous threat exposure management.
- Business-risk prioritisation. Results are prioritised based on the real business impact. This is the same as the CTEM prioritisation phase and assists teams in correcting what is important.
- Compliance-mapped reporting. Reports are in line with ISO 27001, PCI DSS, HIPAA, SOC 2, and GDPR. This helps in achieving audit preparedness and cyber exposure management objectives.
- Remediation and retesting. Qualysec collaborates with development teams to address findings.
The team retests after fixes to ensure the problem is resolved. This is the end of the mobilisation phase.
- Global coverage. Qualysec has customers in finance, healthcare, SaaS, retail and enterprise fields globally.
No matter whether it is your initial CTEM security program or an enhancement of an existing one, Qualysec can offer the experience and framework that you require. Their methodology continuously manages threats, validates them, and linked to actual business performance.
Get Your Free ISO Readiness Score + Expert Consultation — Contact for a free consultation with Qualysec now.
Conclusion
CTEM (Continuous Threat Exposure Management) provides organisations with a well-understood, repeatable method of staying ahead of threats. It transforms security into a cycle of periodic scans into a continuous cycle. The different stages, such as scoping to mobilisation, relate technical findings to actual business risk.
Reactive approaches are inadequate as the exposure to threats is increasingly becoming complex across the cloud, AI, and hybrid environments. CTEM (Continuous Threat Exposure Management) bridges this gap by improving and ascertaining actual risk, and aligning with teams.
Begin the process of developing your ongoing threat exposure management programme. Prioritise what matters. Authenticate what is actual. Repair what might harm. The modern cyber exposure management of any organisation, small or big, belongs to any industry, and is based on a robust CTEM program.
Get Your Free ISO Readiness Score + Expert Consultation — Schedule a Free Consultation with Qualysec.
Speak directly with Qualysec’s certified professionals to identify vulnerabilities before attackers do.
FAQs
What are the 5 stages of CTEM?
There are five stages of CTEM, which include Scoping, Discovery, Prioritisation, Validation and Mobilisation. These phases are an endless cycle that enhances threat exposure management over time. The first thing one has to learn before understanding what CTEM is is learning these five stages.
What is the difference between CTEM and exposure management?
Exposure management is a broad concept that covers identifying security risks. The CTEM (Continuous Threat Exposure Management) is a particular five-step system that introduces structure, validation and business alignment to exposure management.
What is the difference between CTEM and SIEM?
CTEM security is proactive, seeks exposures and their exploitation before they occur. SIEM is dynamic and aims at identifying and investigating security events once they occur.
What is the CTEM methodology?
The CTEM (Continuous Threat Exposure Management) approach is based on a five-stage cycle of Gartner. It never stops scanning assets, finding exposures, ranking by business risk, testing and assembling teams to fix them.
What is the difference between ASM and CTEM?
ASM concentrates on finding external-facing assets and their exposures. CTEM (Continuous Threat Exposure Management) is a generalisation of ASM, with the addition of prioritisation, validation, and coordinated remediation throughout the entire lifecycle of threat exposure. Whoever poses the question of what CTEM is must be aware that it is the entire program, and ASM is a part of it.












































































































































































































































































































































































































































































































































































































































































































0 Comments