Today, cloud services are being used by organizations across the globe to keep pace with data and business needs in a world that is evolving rapidly digitally. Amazon Web Services (AWS), known for its strong AWS Cloud Security, is considered one of the leading cloud service platforms available. Accordingly, it provides various means by which you can cater to your business requirements.
Furthermore, the goal of AWS cloud security services is to prevent potential threats, attacks, and risks to its data, applications, and infrastructure. As we go through this blog it will explain what AWS Security is, why it matters (especially if you are learning or working on these cloud systems), how they function, ways in which effective use of them can be made, and the benefits that follow when recommendations are properly followed.
What is AWS cloud security?
AWS Cloud Security provides a secure environment in which to run your applications and store data that satisfies the strictest compliance requirements. Therefore, AWS security is an approach that gives more flexibility to users.
Security and flexibility are combined so that customers can select their preferred level of security with AWS’s strong foundational model. Because of all this, AWS cloud security services have become a great choice to cover the loopholes in vital business data stored in external servers — especially during crises.
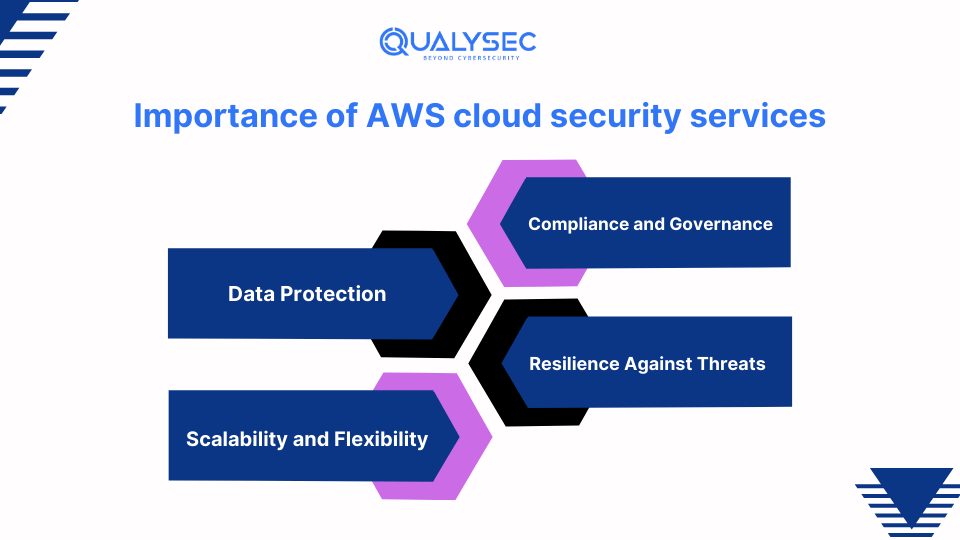
Importance of AWS cloud security services
AWS Cloud Security services provide the tools and frameworks to address issues and ensure that data is kept secure for operation. Here are some key reasons why security is so critical to organizations:
1. Data Protection:
It is crucial to prevent unauthorized access to data. AWS provides encryption, access controls, and other tools to maintain the confidentiality and integrity of data.
2. Compliance and Governance:
Many industries are subject to regulations that they must adhere to. The reports help them demonstrate to auditors and obtain the necessary compliance certifications using AWS Cloud Security services.
3. Scalability and Flexibility:
Businesses are dynamic, meaning business requirements change constantly. AWS offers security solutions that can scale with demand, enabling organizations to increase security measures as needed.
4. Resilience Against Threats:
The cloud environment is under constant threats of various cyber risks. AWS Security services offer several products to detect threats and secure against cyber threats.
Would you like to protect your AWS applications from all these security threats? Get in touch with us for the best penetration testing services that will enable you to enhance your general AWS security.
Talk to our Cybersecurity Expert to discuss your specific needs and how we can help your business.
How does Amazon AWS Cloud Security work?
AWS Cloud Security is based on security measures, services, and standards. This platform delivers layer upon layer of security to data and applications within the cloud landscape. For instance, here is a breakdown of what it includes:
1. Identity and Access Management (IAM):
IAM is the security foundation in AWS, determining who can do what with the services. Abiding by the least privilege principles, strict password policies, and multi-factor authentication are ways to improve your IAM landscape.
2. Data Security:
This is vital because data traveling through different networks and servers can lead to potential breaches. Leverage AWS services like Amazon S3 and DynamoDB to ensure data security.
3. Security Groups & Network Access Control Lists (ACLs):
These tools control inbound and outbound network access, permitting only certain services or applications. Use security groups carefully to set appropriate network boundaries.
4. Logs and Monitoring:
Security should be monitored 24/7, with all logs recorded to detect threats promptly. Use CloudTrail, Amazon CloudWatch, and other AWS cloud security tools to track user activity and resource changes, and identify suspicious actions.
5. Compliance and Regulatory Requirements:
Businesses in highly regulated industries must ensure that cloud environments meet regulatory mandates. Look for compliance rules like HIPAA and PCI DSS and use Amazon Web Services-compliant solutions and tools.
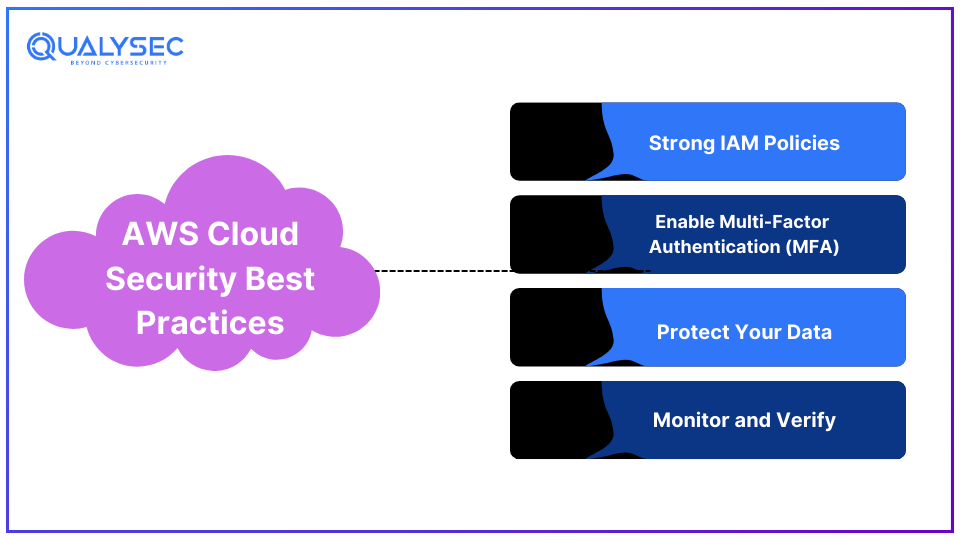
AWS Cloud Security Best Practices
Proactively following best practices can dramatically reduce vulnerabilities in your environment while making it more secure. Here are some key tips:
1. Strong IAM Policies:
Give users only the permissions they need to perform their tasks. Regularly review and update IAM policies.
2. Enable Multi-Factor Authentication (MFA):
MFA adds another layer of security by requiring users to authenticate with multiple mechanisms before accessing AWS resources.
3. Protect Your Data:
Use AWS encryption services to secure data at rest and in transit. Regularly rotate encryption keys.
4. Monitor and Verify:
AWS CloudTrail and Amazon CloudWatch are used to track user activities and resource management. Set up alerts for unusual activities.
Benefits of Compliance on AWS
Adhering to industry standards and protocols, including AWS cloud compliance, is another benefit companies gain by adopting AWS cloud security services. Here are some key advantages:
1. A More Secure Environment:
Following standards like GDPR, HIPAA, and PCI DSS ensures the cloud environment adheres to best security practices, providing a haven for sensitive information.
2. Increased Trust:
Compliance reassures individuals that their data and information are safe.
3. Reduced Risk:
Adherence helps mitigate risks from identified vulnerabilities, preventing data loss or other threats.
4. Help for Auditors:
AWS provides documentation and resources to simplify audits, making compliance meet urgency and severity requirements easier.
Conclusion
AWS Cloud Security services are essential for securing cloud systems, applications, and data, ensuring customers maximize their investments. By following AWS’s built-in security measures, industry standards, and current trends, companies can safeguard their cloud environments from cybercrime’s adverse effects. As technology advances and new threats and opportunities emerge, AWS continually offers practical security features, enabling clients to leverage the cloud’s benefits while staying fully secure.
FAQs
1. What are AWS security services?
A. AWS security services encompass a variety of tools and features that AWS offers to assist in safeguarding cloud environments. The services include managing user identities and access (IAM), encrypting data, protecting networks, detecting threats, and aiding in compliance and auditing.
2. What are common vulnerabilities in AWS?
A. Some of the common vulnerabilities in AWS are:
- Misconfigured access control
- Unpatched software
- Exposed data storage
- Insufficient monitoring
3. How many types of security are there in AWS?
A. Types of AWS are:
- Identity and access management
- Data protection
- Network security
- Compliance management
- Threat detection
4. What AWS services can I use to protect my cloud?
A. AWS provides a wide range of services to protect the cloud. Some of them are:
- AWS Identity and Access management
- AWS key management services
- AWS Shield
- AWS Configuration






















![Top 20 Network Security Companies in USA [2025 Updated List]](https://qualysec.com/wp-content/uploads/2025/05/Top-20-Network-Security-Companies-in-USA-2025-Updated-List-scaled.jpg)

























































































































































































































































































































































































































































































0 Comments