PCI DSS is a compliance requirement that was first created in 2004 and is likely recognizable by yourselves if your company accepts payments made with credit cards. Still, more businesses are handling and conserving credit card data on the public internet as the cloud becomes more widely used. This creates new compliance issues because cloud security necessitates a whole different strategy than on-premise security. Incorporating PCI compliance penetration testing into your security strategy is critical to addressing these challenges effectively. This piece of writing will cover PCI DSS compliance in full, including its significance and how you can achieve it.
What is the PCI DSS?
To safeguard cardholder information and stop scams, companies that handle credit cards must adhere to a set of safety guidelines known as the Payment Card Industry Data Security Standard (PCI DSS). To protect and strengthen the data associated with payment cards during processing, handling, storage, and distribution, PCI DSS contains comprehensive technological requirements. All companies handling credit card information, regardless of dimensions, have to adhere to these guidelines and stay in compliance with PCI. Noncompliance can lead to substantial penalties, legal consequences, and harm to one’s credibility.
“Explore more: What is PCI DSS Compliance? Requirements and Best Practices
Understanding PCI DSS in the Cloud Environment
1. Cloud Computing and the Payment Sector:
Cloud computing is having a big and complicated impact on the payment sector as it continues to change the corporate landscape and becomes a key component of how organizations store and handle data. For businesses that handle sensitive credit card data, integrating cloud services with PCI DSS Cloud Compliance Testing is very important.
2. Challenges of Cloud Scalability:
Although advantageous, the cloud’s scalability and flexibility present unique data security and compliance challenges. To solve these issues, the PCI DSS has changed to take into account the particular security threats presented by cloud systems. This development aims to guarantee that, even while utilizing the extensive capabilities of the cloud, all parties engaged in the payment process can maintain a secure environment for cardholder data.
3. PCI DSS Updates for Cloud Security:
The most recent revisions to the PCI DSS standards demonstrate a greater comprehension of the complexities of cloud computing. These changes are intended to guarantee adherence to strict security protocols and offer precise instructions on how to protect cardholder data in the cloud. For instance, incorporating PCI compliance penetration testing has become essential for identifying vulnerabilities and addressing potential threats specific to cloud environments. The standards now include more stringent criteria for vulnerability management, authentication, authorization, and ongoing monitoring that are especially suited to cloud computing methods of operation.
4. Securing Data Across Environments:
This emphasis guarantees that businesses are prepared to successfully safeguard critical data irrespective of where it is stored—on real servers or in virtualized environments. The PCI SSC is contributing to risk reduction and increased confidence throughout the financial ecosystem by creating comprehensive recommendations and compliance criteria for cloud security. These initiatives facilitate a safe shift to cloud-based payment processing platforms by addressing the changing nature of cloud services in addition to supporting the security of conventional on-premises infrastructures.
5. Flexibility in Cloud Deployment Models:
The adaptability given by PCI DSS v4.0 is essential for cloud services due to the variety of deployment methods, which range from public and private clouds to hybrid and multi-cloud settings. Because each of these models has different risks and constraints, customized security controls are needed rather than a one-size-fits-all strategy. By offering foundations that let companies tailor their security procedures to their unique cloud deployments, PCI DSS penetration testing plays a crucial role in ensuring robust security in diverse environments.
Certain Shifts Affecting Cloud Environments
Modifiable Execution: PCI DSS v4.0 gives businesses the freedom to adopt more creative and appropriate technology solutions that fit their unique cloud architecture by enabling them to create bespoke controls that satisfy the standards’ objectives. Utilizing cloud-specific technologies like virtualization, containerization, and dynamic provisioning requires this flexibility.
Combining Cloud Security Best Practices: Integration with well-known cloud security best practices and frameworks, including those suggested by the Cloud Security Alliance (CSA), is encouraged by the latest edition of PCI DSS. This keeps safety measures current with the most recent developments in risk management and cloud computing.
Increased Management over Cloud Privacy: PCI DSS v4.0 incorporates more stringent criteria for encryption and tokenization both at rest and in transit, as well as a greater focus on data protection, particularly in the cloud. This guarantees that private payment data is protected at every stage of its lifespan, regardless of the cloud service paradigm (IaaS, PaaS, or SaaS) that is being used.
Responsibility and openness on the part of customer service providers: The revised standard requires providers of cloud services to give more thorough proof of compliance. This involves thorough documentation and openness in security procedures, allowing companies to confirm that their cloud-based systems successfully comply with PCI DSS regulations.
Additionally, performing PCI compliance penetration testing has become critical for identifying vulnerabilities and ensuring that cloud-based systems meet compliance standards.
Cloud-Based PCI DSS Compliance Best Practices
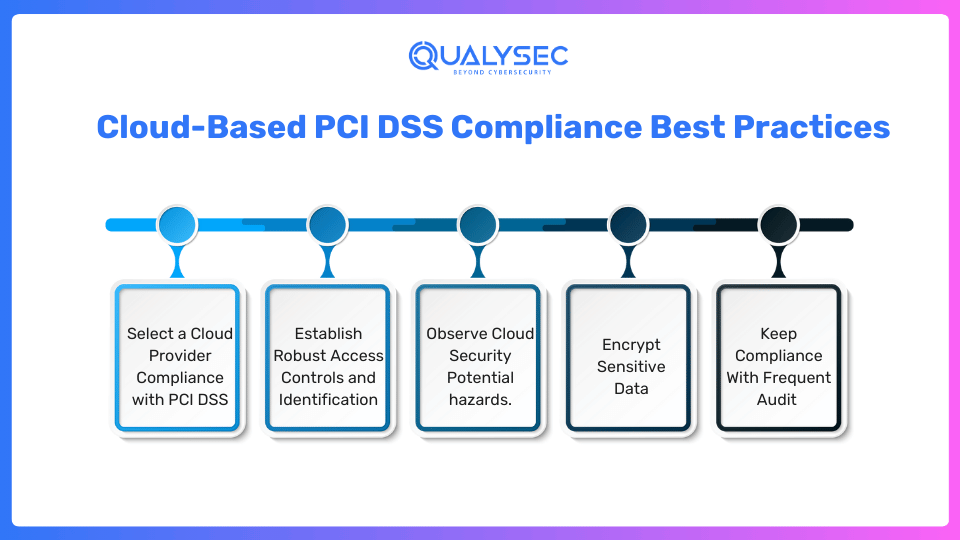
1. Select a Cloud Provider Compliance with PCI DSS:
Your ability to comply with the PCI DSS setup is based on the choice of cloud provider. Choose a cloud operator who has a current PCI DSS accreditation and an excellent record of compliance and safety. This guarantees that your cloud environment gains from robust security procedures and guidelines that conform to the standards of the industry. Your company will have less work to do because an approved cloud provider takes on a large amount of safety responsibilities.
2. Establish Robust Access Controls and Identification:
To comply with PCI DSS, it is critical to secure access to your cloud environment. Select strong authentication methods, such as multi-factor authentication (MFA), which guarantees that confidential information can only be accessed by authorized personnel. Users’ rights are further restricted to particular positions and duties via role-based access control (RBAC). These steps reduce the possibility of information theft and unauthorized access.
3. Observe Cloud Security Potential hazards:
Sustaining PCI DSS compliance in the cloud requires constant observation. Put in place a complete protection surveillance system with threat analysis, vulnerability analysis, detection of breaches, and current time detection of threat features. Timely identification of questionable activity or possible breaches of security enables you to take immediate action and neutralize risks prior to they become more serious.
Regular PCI compliance penetration testing helps identify vulnerabilities and ensure ongoing compliance.
4. Encrypt Sensitive Data:
protecting all the sensitive data while it’s in transit and at rest to prevent unauthorized access to cardholder information. With a minimum key length of 256 bits, use robust encryption techniques like Advanced Encryption Standard (AES). In the event of a breach, keep the encryption keys apart from the encrypted data in a safe place to avoid any possible compromise. To maintain the confidentiality of data, encryption provides an extra degree of security.
5. Keep Compliance With Frequent Audit:
To verify and prove compliance with the PCI DSS in the cloud, regular audits and evaluations are essential. Regularly hire certified safety professionals to carry out in-depth audits of your cloud system, policy, and practices. The audits include information about possible issues with security as well as suggestions for enhancements. Being active guarantees that your operations stay in compliance and are prepared for any legal inspection.
“Discover more in our article: The Ultimate Guide to Compliance Security Audits
Other Cloud-Based PCI DSS Compliance Techniques
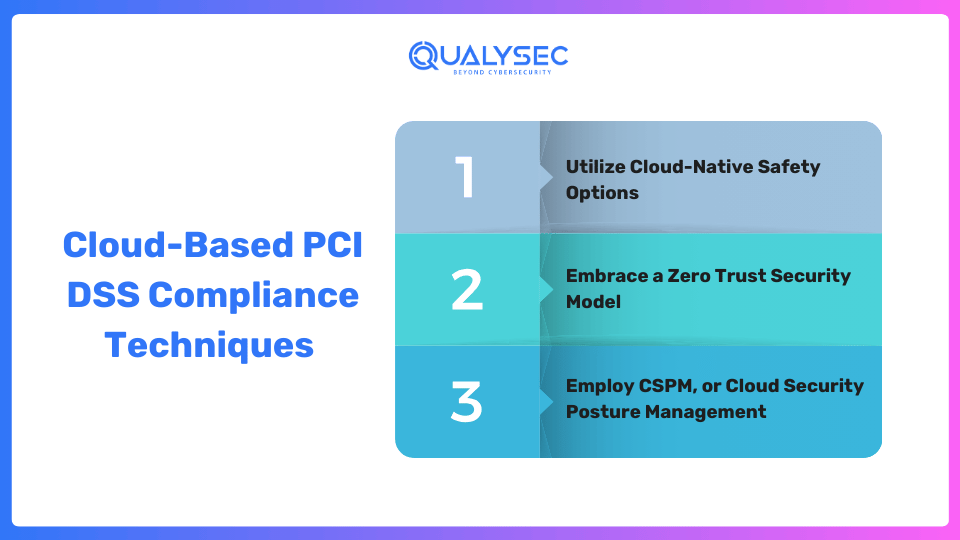
Utilize Cloud-Native Safety Options:
Examine cloud-native safety measures designed to handle the particular difficulties associated with safeguarding cloud environments. These products guarantee a smooth transition to PCI DSS compliance by automating compliance chores, improving the identification of threats, and streamlining safety oversight procedures.
Embrace a Zero Trust Security Model:
According to a lack of confidence security concept, no entity—user or device is intrinsically reliable. Using this strategy guarantees that, regardless of the case of a compromise, the cloud infrastructure you use will be safe. Because each access request is thoroughly checked, the assault’s area and possible harm are reduced.
Employ CSPM or Cloud Security Posture Management:
An invaluable tool for your PCI DSS compliance path is a CSPM system. It finds issues and errors in your cloud environment so you can quickly fix them. CSPM guarantees adherence to compliance standards and assists in preventing information theft by reducing threats to security.
Getting the Most Out of PCI DSS Compliance
-
- Improved Security of Data: Complying with PCI DSS ensures that strong safeguards are in place, shielding cardholder data from incidents, attacks via the internet, and unauthorized access.
-
- Client confidence and Status: By assuring clients that their data is in competent custody, compliance promotes confidence and improves the standing of the business you run.
-
- Legal and Regulatory Compliance: PCI DSS compliance guarantees conformity to legal and regulatory requirements, hence reducing the risk of penalties and fees.
-
- Decreased Information Breach Risk: By adhering to standard procedures, companies can significantly decrease the chance of data theft while protecting your company from possible monetary losses and harm to its brand.
-
- Operational Efficiency: Implementing strong security controls improves productivity and reduces delays from safety threats, resulting in savings in expenses.
Important Updates to PCI DSS That Impact Cloud-Based Computing
-
- PCI DSS enables more customizable safety precautions to match the various and dynamic nature of cloud systems. This implies that companies can improve productivity and effectiveness by putting in place security policies created especially for the cloud.
-
- PCI DSS puts a greater value on reliable authorization procedures and cutting-edge encryption methods to safeguard information exchanges because of the nature of the cloud, which frequently involves data transmission over multiple networks.
-
- The importance of continuous risk assessment and control stems from the cloud’s fluid features, which necessitate regular risk assessments. Ongoing risk evaluation is required by PCI DSS to quickly detect and manage threats, which is essential in cloud systems that are subject to rapid change.
-
- By encouraging service providers to be open and honest about their security procedures and making sure they satisfy PCI DSS’s strict requirements, the revised rules hold them more accountable.
How QualySec helps in cloud PCI DSS compliance
QualySec provides a wide range of cybersecurity services, including cloud security solutions, compliance assessment services, and PCI DSS penetration testing services. Through our experience and customized remedies, we can help your company achieve and sustain cloud PCI DSS compliance. Join us on your compliance journey to protect your brand and the trust of your consumers. Do not take chances with PCI DSS compliance. Make QualySec your reliable cybersecurity partner.
Speak with our experts for cybersecurity pentesting services and PCI DSS compliance requirements. To Schedule a call, click on the box below!
Talk to our Cybersecurity Expert to discuss your specific needs and how we can help your business.
Qualysec Technologies excels in this domain, delivering high-quality cybersecurity audits that enhance trustworthiness while ensuring the safety of applications remains intact. Its robust presence in multiple regions worldwide reflects its commitment to offering cybersecurity-related services, reinforcing its strength.
QualySec also offers an extensive length of other major services that are as follows:
- Cybersecurity Audit
- Web Application Penetration Testing
- Mobile Application Penetration Testing
- Cloud Pentesting
- API Pentesting
- Thick Client Pentesting
- AI/ML Pentesting
- IoT Device Pentesting
In addition to providing security solutions and suggestions to enhance the security of their systems, apps, networks, and software, Qualysec plays a major role in helping businesses and organizations uncover vulnerabilities and security threats. Qualysec’s exceptional services are therefore the best option for cybersecurity audits and website security evaluations.
Download our latest penetration testing report now!
Latest Penetration Testing Report

Conclusion
The continuous dedication to protecting sensitive information about cardholders is known as PCI DSS compliance. By incorporating these methods including PCI compliance penetration testing, and other tactics into the cloud, you can improve the safety of your data, strengthen your safety measures, and manage the challenges of complying with regulations.
FAQ:
Q. What are the major complications in cloud-based PCI DSS compliance?
A. Implementing security controls in fluid cloud-based settings, and ensuring data confidentiality, while upholding appropriate access rules and regulations with regular monitoring and auditing systems are some of the difficulties that come.
Q. Which are the top methods for cloud-based PCI DSS compliance?
A. Selecting a compliant cloud provider and putting safe authentication and access restrictions in place, keeping an eye out for the risks to the cloud environment, encoding dangerous data, and carrying out frequent audits and evaluations are the top practices.
Q. Why is PCI DSS compliance so important for cloud-based businesses?
A. Achieving PCI DSS compliance in the cloud is crucial for safeguarding sensitive data and maintaining client trust in the provider. Failure to comply can result in serious data holes, drawbacks, and major destruction of the organization’s name.
























































































































































































































































































































































































































































































































0 Comments