API penetration testing keeps the APIs safe from cyberattacks and data breaches. APIs or Application Programming Interfaces are those software that help different apps communicate with each other. APIs have revolutionized the digital landscape by playing a key role in the rapid advancement of software and application development within DevOps teams.
However, due to their critical nature and the way they handle sensitive data, they have become a prime target for attackers. In fact, research shows that insecure APIs may cause a loss of up to $75 billion globally.
In this blog, we will cover the importance of API penetration testing, its checklist, its process, and how it is different from other penetration testing services. If your application uses APIs, you need penetration testing.
What is API Penetration Testing
An API penetration test is done by pen testers to ensure that the APIs are properly secured from various cyber threats. The tester may use automated tools and manual testing methods to find security vulnerabilities on the interfaces and all components of the API. This is an offensive security practice where the testers subject the APIs to real attacks to check if they are strong enough to prevent them.
The goal of API pen testing is to identify security vulnerabilities, ensure compliance, enhance its security, and build trust among customers. After testing, the pen testers will provide you with a detailed report that will include identified vulnerabilities in APIs, their impact level, and how to address them.
What is the Difference Between API Pentest and web Pentest?
Different types of applications require different security testing approaches. API pen testing, including Rest API pentesting, GraphQL API pentesting and SOAP API pentesting, differs significantly from the methodologies used in web applications and other software. Given the specialized nature of the APIs, let’s understand how it is different from traditional application testing.
| Aspect | API Penetration Testing | Web App Penetration Testing |
| Focus | Testing interfaces and data exchanges between systems. | Testing web pages and server-side functionalities. |
| Methodology | API-specific vulnerabilities and authentication mechanisms. | OWASP Top 10 web vulnerabilities, including XSS and SQL Injection. |
| Tools | Uses specialized tools for API endpoints and data formats. | Uses tools like vulnerability scanners for web apps. |
| Attack Surface | Targets endpoints, headers, parameters, and API schemas. | Targets URLs, forms, cookies, and server configurations. |
| Challenges | Handling various data formats and authentication methods. | Dealing with complex client-side interactions and DOM manipulation. |
| Security Considerations | Focuses on securing API keys, tokens, and rate limiting. | Focuses on session management, input validation, and secure authentication. |
Why API Penetration Testing is Important
API penetration testing is important primarily to secure the application it is integrated into. It also ensures the data processed by the API is also safe from breaches. Testing the API will help the developers know the potential security vulnerabilities it has. As a result, they can be remediated before attackers can exploit them.
By conducting regular API pen tests, organizations can significantly reduce the risk of security breaches and protect their data and applications. Additionally, API penetration testing services can also help organizations with necessary compliance.
Benefits of API Penetration Testing
As discussed above, organizations can enjoy several benefits by conducting API penetration testing, such as:
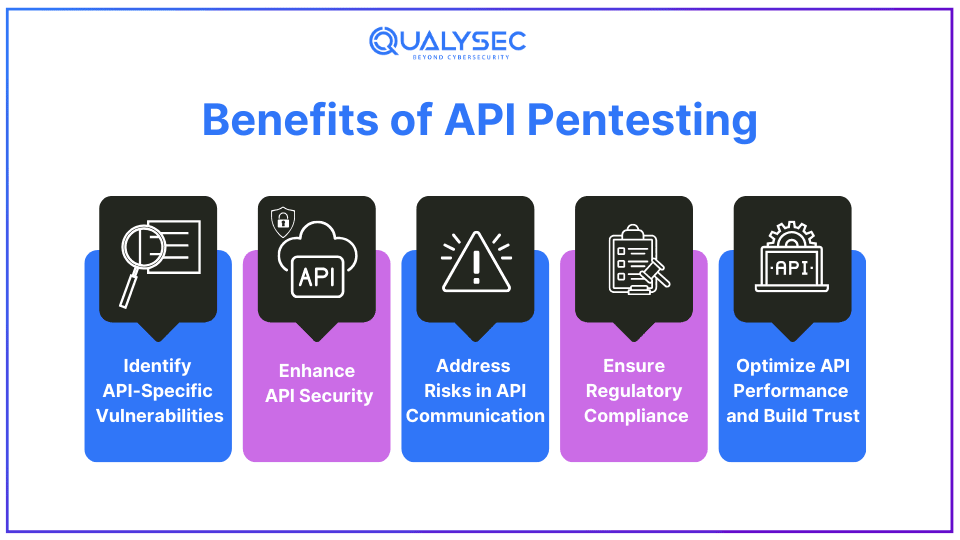
1. Identify API-Specific Vulnerabilities
API penetration testing thoroughly examines endpoints, authentication mechanisms, input validation procedures, and authorization controls. It uncovers both common and API-specific vulnerabilities, such as insecure API endpoints, inadequate authentication methods like weak tokens or keys, and improper handling of sensitive data formats like JSON or XML.
Security testing APIs is essential for identifying and mitigating vulnerabilities, ensuring strong protection against cyber threats.
2. Enhance API Security
By finding and addressing security vulnerabilities, API pen testing strengthens its overall security. It ensures that the API is resilient against emerging threats that target sensitive data and API operations. Additionally, since API is directly integrated with the applications, its security is also important for the application’s security.
3. Address Risks in API Communication
API pen testing helps in identifying and mitigating risks associated with API communication, including unauthorized access, data breaches, and man-in-the-middle attacks. It helps organizations protect sensitive data managed by transmitted through the APIs and ensures compliance with data protection laws.
4. Ensure Regulatory Compliance
API penetration testing helps organizations comply with regulatory requirements by verifying the security measures for API data handling and privacy. Not complying with these laws may result in legal fines and loss of business reputation. As a result, pen testing assures that the APIs adhere to standards such as PCI-DSS for payment processing APIs or HIPAA for healthcare data APIs.
5. Optimize API Performance and Build Trust
Apart from security, API penetration testing also tests the reliability and performance of the API. It helps identify and address security-related performance issues such as latency, throughput bottlenecks, and scalability concerns. Additionally, a secure API builds trust among its customers, partners, and stakeholders, as there are fewer risks of security incidents.
Want to make your API and applications secure? Partner with Qualysec for customized penetration testing for all your security needs.
Talk to our Cybersecurity Expert to discuss your specific needs and how we can help your business.
API Penetration Testing Checklist
This API penetration testing checklist is a comprehensive guide that outlines essential security measures required to enhance API security. It is based on established security standards, such as the OWASP Top 10 API Security Risks.
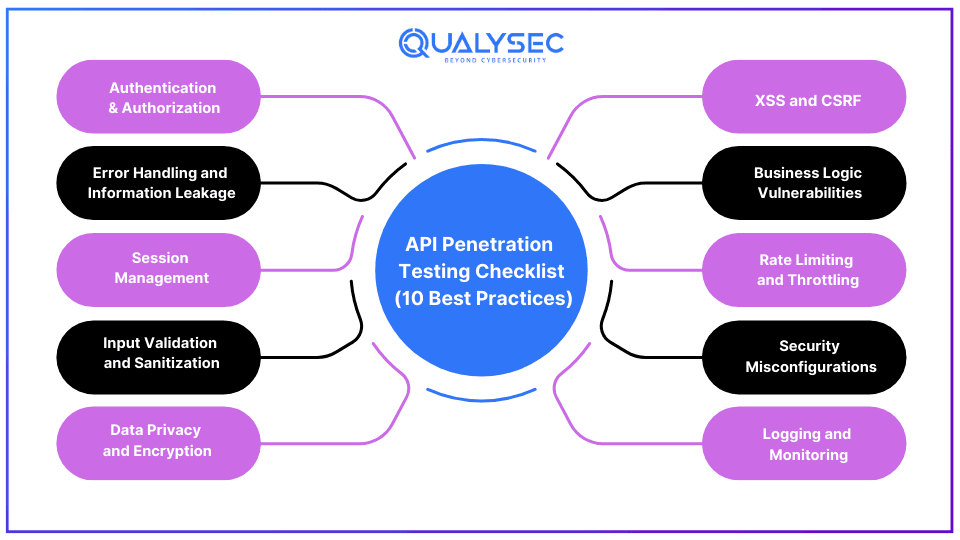
1. Authentication & Authorization
Verifying whether the authentication mechanisms are effective and that only authorized users or applications can access the API. Also, check if the API has proper authorization measures to prevent unauthorized access to resources.
2. Input Validation and Sanitization
Attempting to exploit common vulnerabilities like SQL injection and other injection attacks to examine how the API handles user input. It checks whether the API properly validates and sanitizes the data supplied by the user.
3. Error Handling and Information Leakage
Evaluating how the API handles errors and whether it provides detailed error messages. Without an error-handling system, it can result in information leakage, potentially helping attackers understand the API’s structure and attack vectors.
4. Session Management
If the API has session management, check the session handling mechanisms for vulnerabilities like session fixation, session hijacking, and session timeout settings.
5. Data Privacy and Encryption
Reviewing how sensitive data is stored, processed, and transmitted within the API. Ensuring the data is encrypted and using protocols like HTTPS. Additionally, checking whether the data is adequately protected at rest.
6. XSS and CSRF
Detecting vulnerabilities that could lead to Cross-Site Scripting (XSS) and Cross-Site Request Forgery (CSRF). XSS refers to malicious scripts injected into the API responses and CSRF refers to unauthorized actions performed on behalf of authenticated users.
7. Business Logic Vulnerabilities
Examining the API’s business logic to identify security issues, which can be exploited by attackers for unauthorized access, manipulation, or data exposure.
8. Rate Limiting and Throttling
Verifying that the API has sufficient rate-limiting and throttling controls to prevent excessive traffic and malicious overload attempts. Additionally, it helps prevent denial-of-service (DoS) attacks and abuse.
9. Security Misconfigurations
Reviewing the API’s configuration settings to ensure they are up to date and do not expose sensitive data or create security weaknesses. Since misconfigurations are the most common source of vulnerabilities, addressing them is critical.
10. Logging and Monitoring
Assessing the API’s logging and monitoring capabilities to ensure that security incidents can be promptly detected and responded to. It helps to quickly respond to security threats and minimizes potential damage to the API.
API Penetration Testing Methodology
While different companies may follow a distinctive process, Qualysec combines automated scanning with manual testing as part of their API penetration testing methodology to provide accurate and detailed reports.
- Information Gathering: First, we gather as much information about the API’s architecture and interfaces to know what we are working with.
- Planning/Scoping: Then we create a plan for the test and define its scope. This includes what areas to test, what vulnerabilities to target, what API penetration testing tools to use, etc.
- Automated Scanning: We use automated vulnerability scanners to test common vulnerabilities on the API’s surface level.
- Manual Pen Testing: Then our skilled ethical hackers manually test the API for each defined vulnerability and check if it is possible to hack or not.
- Report: Then we create and share a detailed pen test report that includes identified vulnerabilities, their severity, and steps to fix them.
- Remediation: The development/IT team uses this report to address the identified vulnerabilities. If they need to, we help them locate the vulnerabilities.
- Retest: Then we retest the API to check whether all the necessary patches have been applied or not, and if any new vulnerabilities are present.
- LoA/Security Certificate: Finally, we provide a letter of attestation, which is proof that the client has successfully conducted API pen tests.
Ever seen a real API pen test report? If not, here’s your chance! Tap the link below and download a sample report in seconds!
Latest Penetration Testing Report

Conclusion
When it comes to finding and fixing security vulnerabilities, the sooner you do it, the better. Attackers are always looking for loopholes in interfaces so that they can hack and access the data and resources. With API penetration testing, organizations can protect their APIs from evolving cyber threats, and eventually their applications. Hack your own applications before real hackers do and avoid significant loss.
FAQs
Q: How API Penetration Testing is Different from Others?
A: The main difference is that API penetration testing involves testing interfaces and data exchanges between systems while web penetration testing focuses on internet-facing assets.
Q: Is API testing the same as automation testing?
A: Automated testing is a part of API testing that focuses on securing the performance and functionality of APIs. The process uses automated tools that scan the API for common vulnerabilities, such as broken authentication, lack of encryption, etc.
Q: How often should we do API pen testing?
A: The recommended number is 1 – 2 times a year. However, you should also do API pen testing if there have been significant changes or if you have faced a cyberattack recently.

























































































































































































































































































































































































































































































































0 Comments