If you have just launched a new app, your website traffic is booming, and everything seems to be going great, then, out of the blue, a cyber attack strikes, leaking sensitive data and tarnishing your hard-earned reputation. Could this have been prevented? The answer is likely yes, with proper cyber security testing.
Cyber security testing is the unsung hero of our connected world. It is the process of identifying vulnerabilities in your systems, applications, and networks to make sure your defenses can stand up to threats.
Whether you are a business owner, IT professional, or someone curious about how everything online stays relatively safe, this blog will walk you through the importance of cyber security testing, the main types, and steps to get started. By the end, you will know why it matters and how to use it to protect your organization and data.
Why is Cyber Security Testing Important?
You have probably heard of data breaches involving major companies like Target, Equifax, or Capital One. These incidents highlight just how devastating cyber attacks can be. Beyond the immediate financial losses, breaches can ruin customer trust, invite legal consequences, and damage reputations for years to come.
Cyber security testing addresses this issue by proactively identifying weaknesses before malicious actors can exploit them. Here is why it is necessary:
- Stay One Step Ahead of Hackers: Cybercriminals constantly evolve their tactics. By regularly testing your systems, you can foresee and fix vulnerabilities.
- Protect Sensitive Data: Whether it is customer information, trade secrets, or personal data, keeping this information secure is important to maintaining trust.
- Ensure Regulatory Compliance: Many industries have data protection laws, like GDPR in Europe or HIPAA in healthcare. Cyber security testing ensures you are meeting these requirements.
- Save Money: Prevention is cheaper than recovery. According to IBM’s Cost of a Data Breach Report, the global average cost of a data breach is $4.45 million. Testing reduces the risk of incurring such costs.
The Main Types of Cyber Security Testing
Cyber security testing isn’t a one-size-fits-all approach. Different types of testing target specific areas of vulnerability in your systems. Below are the most common ones:
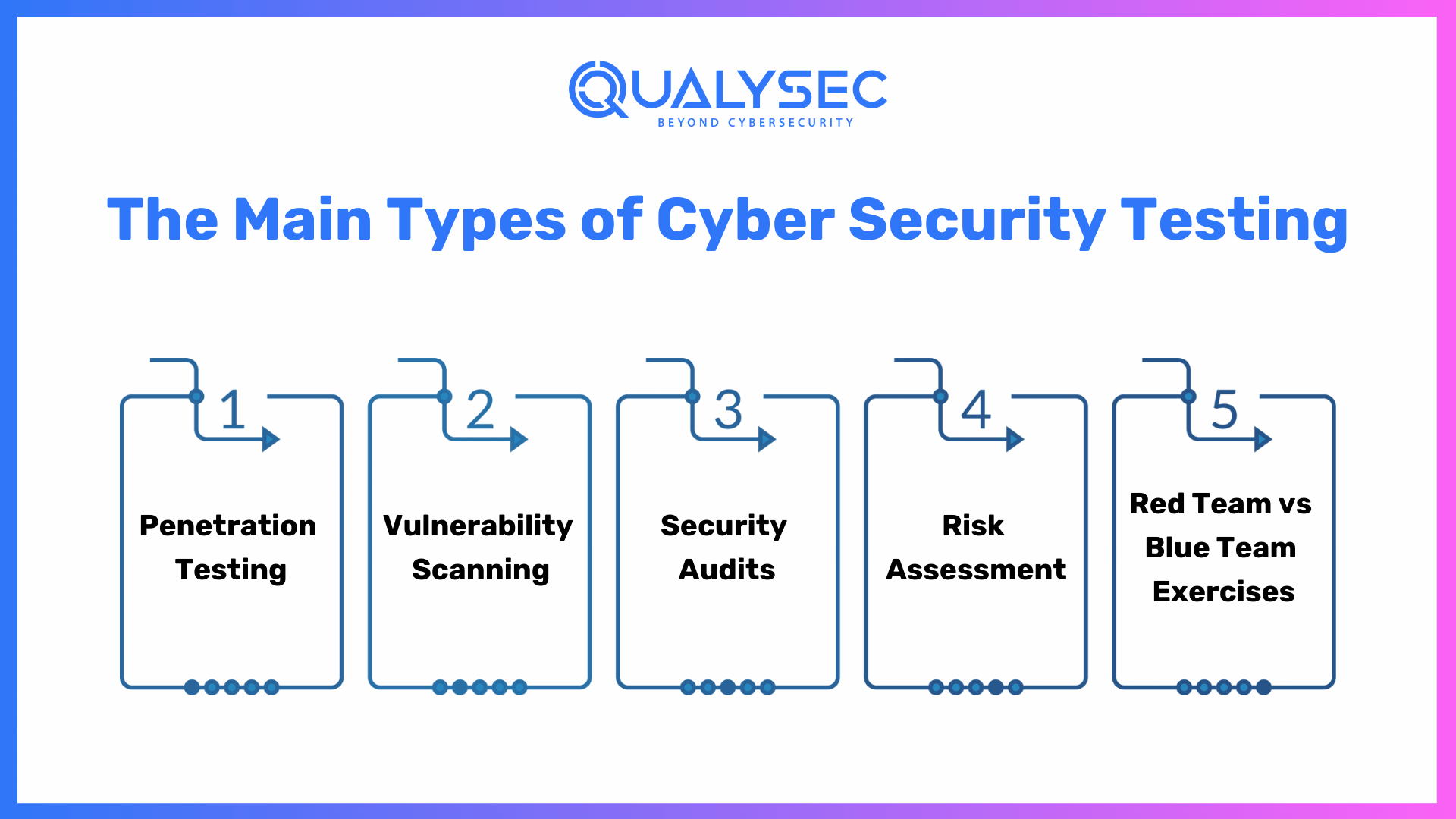
1. Penetration Testing
What it is: Sometimes called “pen testing,” this approach simulates a real-world cyber attack to identify vulnerabilities in your infrastructure. Ethical hackers, also known as penetration testers, try to break into your systems just like malicious hackers would.
Benefits:
- Identifies exploitable vulnerabilities
- Provides a detailed report of security weaknesses
- Tests your organization’s response to attacks
Example in use: A major e-commerce platform might use penetration testing to uncover how hackers could exploit payment systems.
2. Vulnerability Scanning
What it is: Vulnerability scanning involves using automated tools to detect known security weaknesses in your systems, applications, and networks. Unlike penetration testing, this method doesn’t simulate actual attacks.
Benefits:
- Efficient for ongoing monitoring
- Identifies outdated software and misconfigurations
- Provides a snapshot of security posture
Example in use: A small business might run monthly vulnerability scans to ensure their website and email systems are secure.
3. Security Audits
What it is: A systematic evaluation of your organization’s security policies, controls, and procedures. Audits ensure that your cybersecurity measures comply with both external regulations and internal policies.
Benefits:
- Helps meet regulatory requirements
- Identifies gaps in compliance
- Ensures alignment with best practices
Example in use: A financial institution conducting annual audits to comply with PCI DSS (Payment Card Industry Data Security Standard) requirements.
4. Risk Assessment
What it is: This involves analyzing the likelihood and impact of potential cyber threats to prioritize resources effectively.
Benefits:
- Allocates efforts where they’re most needed
- Quantifies risks for better business decisions
- Reduces unnecessary spending on low-priority areas
Example in use: An enterprise with multiple locations might evaluate risks to focus on high-impact threats like database breaches.
5. Red Team vs. Blue Team Exercises
What it is: A red team simulates attackers (offensive team), while a blue team defends against them (defensive team). These exercises test detection and response capabilities.
Benefits:
- Improves incident response
- Tests team preparedness
- Identifies weaknesses in real time
Example in use: A healthcare organization might use red team exercises to simulate ransomware attacks.
How to Get Started with Cyber Security Testing
Implementing cyber security testing can feel overwhelming, but breaking it down into clear steps can simplify the process:
Step 1: Define Your Goals
Determine what you want to achieve with testing. Are you aiming to tighten compliance, protect sensitive data, or improve response times? Clear objectives will guide the type of tests you need.
Step 2: Assess Current Security Measures
Take inventory of your existing security tools, software, and protocols. This will help you identify gaps and areas that require immediate attention.
Step 3: Choose the Right Testing Method
Select the type(s) of cybersecurity testing most relevant to your organization’s size, industry, and risks. For example, if you are in retail, penetration testing on payment systems should be a priority.
Step 4: Engage Experts
Hire certified cybersecurity professionals or ethical hackers to conduct tests. Automated tools are useful, but skilled experts bring added value by uncovering nuanced vulnerabilities.
Step 5: Act on Findings
Testing is useless if you don’t act on the results. After receiving a report, prioritize the most critical vulnerabilities and address them. Create an action plan with deadlines to stay on track.
Step 6: Test Regularly
Cybersecurity isn’t “set it and forget it.” Threats evolve constantly, so schedule regular scans, audits, and penetration tests. Quarterly or biannual reviews are common practices.
“You may find it interesting to explore: What is a Cybersecurity Audit and How to Conduct One.“
Cyber Security Testing Best Practices
To maximize the benefits of cyber security testing, always keep the following best practices in mind:
- Create a Testing Schedule: Regular tests will ensure that no new vulnerabilities are overlooked.
- Document Everything: Maintain detailed records of test results, actions taken, and improvements made to track progress over time.
- Invest in Training: Employee errors remain a common vulnerability. Educate staff on recognizing phishing attempts and securing sensitive data.
- Combine Methods: Using a mix of penetration tests, vulnerability scans, and audits ensures broad coverage.
- Monitor Continuously: Use real-time monitoring tools to alert you to suspicious activity immediately.
Building a Proactive Cybersecurity Culture
Cyber security testing is just one piece of the puzzle. To truly protect your organization, refining a proactive security culture is key. Encouraging team collaboration, conducting training sessions, and giving emphasis to cybersecurity is everyone’s responsibility.
By doing this, organizations can fight against one of the leading causes of breaches, i.e. human error. According to IBM’s data breach report, 95% of breaches involve human mistakes. A proactive culture can significantly reduce these risks.
Why You Should Choose QualySec for Cybersecurity Testing
Managing cybersecurity internally can be overwhelming, especially if your business lacks a dedicated IT security team. That is where services like QualySec come in, providing expert cybersecurity testing tailored to meet your needs.
What Sets QualySec Apart?
- Process-based Penetration Testing: From data-driven penetration testing to security audits, QualySec covers all bases to evaluate and fortify your defenses.
- Specialized Expertise: QualySec’s team consists of ethical hackers and certified testers with years of experience across diverse industries.
- Tailored Recommendations: Receive a clear and actionable report post-testing so you know exactly what steps to take.
- Customer-Centric Approach: QualySec doesn’t stop at testing; they recommend ongoing solutions to help you maintain a state of security readiness.
Thousands of businesses trust QualySec to protect their digital footprints.
Latest Penetration Testing Report

How Can You Contact Us?
- Schedule a free consultation with QualySec’s experts to discuss your goals.
- QualySec conducts data-driven cybersecurity evaluations based on your systems, industry, and testing needs.
- Receive a detailed report with prioritized recommendations to boost security.
QualySec makes cybersecurity simple and accessible so you can focus on growing your business, knowing your systems are in good hands.
Talk to our Cybersecurity Expert to discuss your specific needs and how we can help your business.
Final Thoughts on Cybersecurity Testing
Cybersecurity testing is no longer a luxury, it is an essential step in protecting your business, data, and customers. With the increasing frequency and complexity of cyberattacks, proactive measures are fundamental.
Start by understanding the types of cybersecurity testing and identifying which are most relevant to your organization. Whether it is penetration testing or a full security audit, regular assessments will strengthen your defenses against known and emerging threats.
Why wait for an attack when you can take action today? Protect your business with QualySec. Schedule a free consultation now and take the first step toward unbreachable security.























































































































































































































































































































































































































































































































0 Comments