APIs serve as the fundamental infrastructure for contemporary applications, providing hassle-free data communication to power mobile applications and enterprise-level integrations. Security of APIs remains essential since these interfaces attract attacker focus as primary targets. To defend their APIs and sensitive data, organizations must implement this API Security Checklist containing 15 fundamental protection steps, as listed below by Qualysec Technologies.
15-Step API Security Checklist
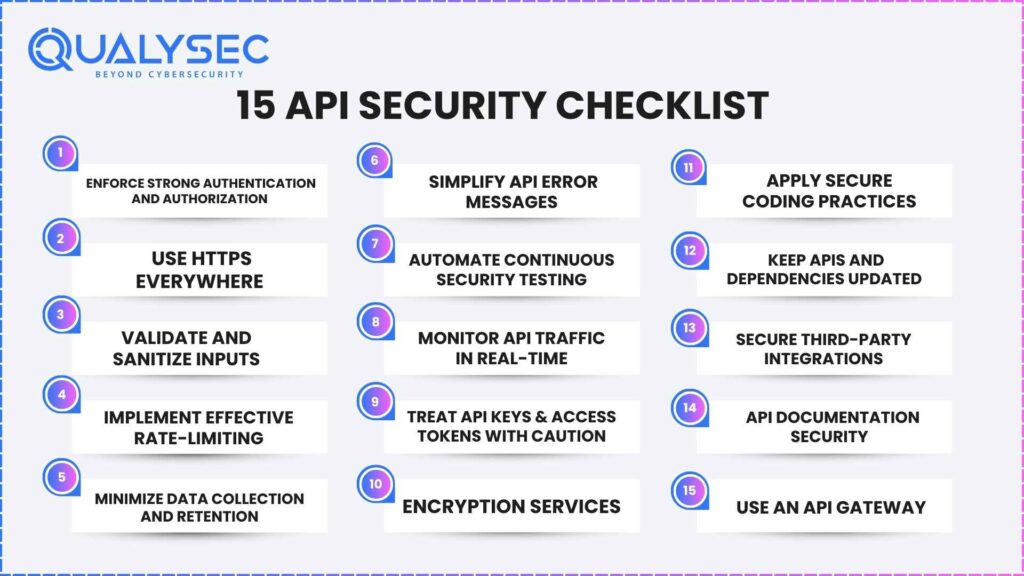
1. Enforce Strong Authentication and Authorization
Implementing both strong authentication protocols and authorization controls with precise access rules will shield your API Security Checklist system. Your organization should use industry-standard authentication systems such as OAuth 2.0 or OpenID Connect to authenticate user identities securely. Role-based access control (RBAC) allows administrators to define exact permission rules that determine what resources users within each role can access. A scheduled key and token rotation process should exist with a protocol for instant credential revocation for all compromised or outdated API authorizations. Deploying mutual TLS (mTLS) as a mandate establishes trust between interacting services through mutual authentication, which secures a zero-trust operational environment.
2. Use HTTPS Everywhere
Every API Security Checklist transmission needs HTTPS protocols as their mandatory standard because this protects information from eavesdroppers and transit-based malicious modification. All API communication must use TLS 1.2 or stronger versions, which must be paired with sturdy cipher suites to provide secure encryption. Secure your API interactions with HSTS to force browser clients to communicate with your platform through HTTPS, which blocks downgrade attacks. The implementation of certificate pinning is an advanced security measure that actively prevents certificate spoofing attacks. HTTP endpoints must always remain encrypted without exception for both internal and external API interfaces because they create redundant weak points.
Read More: What are API Security Risks and How to Mitigate Them?
3. Validate and Sanitize Inputs
Organizations that extensively validate and sanitize their inputs achieve protection from numerous security breaches, including injection attacks, and maintain data integrity. The API Security Checklist uses OpenAPI schemas to define strict request specifications, which trigger automatic rejection of all undefined format requests or requests having content that deviates from expected patterns. Before processing or storage, all incoming user data must undergo thorough sanitization, which identifies and removes potentially damaging content, including malicious scripts and SQL statements. Your API security posture improves through this preventive strategy, which minimizes potential points of attack.
4. Implement Effective Rate-Limiting
API Security Checklist depends heavily on rate-limiting systems, which protect against brute-force attacks while defending against credential compromise attempts and denial-of-service incidents. API endpoint sensitivity determines appropriate rate limit assignment because critical functions need tighter regulation, yet general usage endpoints require more flexibility. Repeat API violations should be handled through penalties implemented through exponential backoff systems. API responses should include informative rate limit headers that reveal client status and available allowances to users while promoting responsible consumption and maintaining transparency.
Related content: Read our guide to Api Security Solution.
5. Minimize Data Collection and Retention
Make sure to collect data only to the necessary amount needed to operate your API correctly and efficiently. A reduced attack surface directly results from less stored data, so organizations must establish specific data storage policies that include secure deletion and anonymization protocols for data after its functional requirements expire. Safeguard sensitive information by keeping it restricted to essential log cases, while you need to apply advanced cryptographic methods that encrypt data during rest periods. The deployment of secure handling practices together with data minimization continues to increase user privacy and diminish the potential damage from data breaches.
6. Simplify API Error Messages
The creation of API error responses requires engineers to strike a precise balance between delivering clear direction while also securing protected data. When clients encounter errors during validation, you should present direct feedback that explains the particular problem. When server-side issues occur, you should display standardized messages that include “Internal Server Error” or “Something went wrong.” To establish semantic context, every error must receive its proper HTTP status code alignment, such as using 400 for client errors, together with 500 for server-based errors. Add a correlation ID to each response to help developers monitor particular requests within their internal logs while maintaining error secrecy from external users. Authorize specific personnel to view and record complete error logs in a secure system.
7. Automate Continuous Security Testing
Installing security assessment systems directly within the software development process is essential for preventing future risks. Businesses should utilize Static Application Security Testing (SAST) and Dynamic Application Security Testing (DAST) tools that provide code- and runtime-based security assessments. Secret detection tools should be integrated into the system to stop sensitive credential leakage. New code submitted in pull requests should activate automated scans through proper configuration. This mechanism executes immediate code scrutiny. Security experts should conduct periodic manual penetration tests to identify complex vulnerabilities because automation establishes a good baseline.
Learn more in our Complete Guide to API Penetration Testing.
Latest Penetration Testing Report

8. Monitor API Traffic in Real-Time
API traffic monitoring in real time functions as a security threat detection tool, which also helps prevent performance-related issues from arising. Language orchestration techniques that combine centralized logging with sophisticated analytics platforms help organizations obtain complete visibility into API use patterns, request error counts, and geographical sourcing. Your system should implement automated detection protocols to warn about atypical events, such as rapid traffic increases, multiple authentication failures, and unusual request source locations. Rigorous log analysis must happen to detect malicious access attempts and unauthorized usage within these logs. With robust real-time monitoring capabilities, your organization can detect security incidents swiftly and respond immediately.
9. Treat API Keys & Access Tokens with Caution
API keys and access tokens operate as fundamental authorization mechanisms that determine who accesses your system’s valuable resources and features. Your system security depends on unique key distribution for every client or service interacting with your system. The keys need thorough permission control, including minimal privileges essential for carrying out intended tasks. Implementing short-lived tokens serves security purposes because they create a shrinking risk window for potential malicious attacks. To prevent unauthorized entry, secure mechanisms should exist to deactivate access when keys are compromised automatically. Give your highest priority to maintaining strict security measures for your sensitive secrets while never disclosing them in client-side code because this exposure makes them easy targets for interception.
10. Encryption Services
Protecting vital data requires end-to-end encryption strategies for data movement and storage functions. Establishing secure data transmission through HTTPS implementation must be balanced by encrypting all sensitive data stored through proven cryptographic systems. Applied to passwords and other highly sensitive identifiers, hash algorithms using salting should be deployed because they create permanently unrecoverable data. Secure key management becomes just as important as encryption techniques. The organization should use key management systems while following least privilege guidelines for all key access activities. A robust security posture depends on periodic security audits, guaranteeing encryption practices stay current with industry standards and best practices.
11. Apply Secure Coding Practices
A fundamental requirement for creating resilient applications involves embedding security evaluations throughout the entirety of the software development lifecycle. The entire development cycle requires strict adherence to existing secure coding regulations. Your system needs reliable input validation and continuous output encoding to stop malicious data injection and prevent cross-site scripting (XSS) attacks. The system should react to errors by keeping sensitive information secret. Build defense-in-depth security through multiple defensive measures, including input validation and output encoding, so individual vulnerabilities cause reduced impact. A secure development lifecycle (SDLC) lets your organization place security requirements into all software design stages to create a workplace culture focused on building secure applications.
Read More: What Is OWASP API Security Top 10.
12. Keep APIs and Dependencies Updated
Security depends radically on maintaining an updated status for APIs along with their supporting dependencies. Unpatched systems create holes that cyber attackers use as entry points to exploit present vulnerabilities. Live updates of APIs and dependencies require an established proactive patching system with automated tools that continuously detect outdated components within your API ecosystem. You should immediately deploy critical security updates after vulnerability detection takes place. API framework maintainers and library developers should inform you about security notices through their official advisories. The immediate implementation of essential updates remains vital because it lets you fight off risks while keeping your API security powerful.
13. Secure Third-Party Integrations
API Security Checklist functionality gains significant benefits from working with third-party libraries and services at the cost of exposing security vulnerabilities. Always use caution when selecting third-party components by choosing providers who demonstrate a solid reputation for security. Review security practices in depth for all third-party systems to guarantee they match your organization’s established security criteria. Supervise third-party integration systems while ensuring their software stays current with available updates. Identity management strategies through least privilege access ensure third-party components receive only essential data and functional permissions. Your organization should track all third-party system activity to detect suspicious or non-standard behavior that signals possible system breaches.
Also Explore: 10 Must-Know API Security Testing Tools for 2025.
14. API Documentation Security
API documentation, which provides full and current details, proves essential for protecting API consumption. Present your API security mechanisms in API documentation by explaining authorization methods, authentication frameworks, rate limitation frameworks, and error code definitions. Your API documentation reveals every security detail to developers who work with your API so they can integrate safely while minimizing security incidents by oversight or unintentional abuse. The documentation must receive quick updates when security changes happen to your API so that developers can get accurate, timely guides for secure API integration.
15. Use an API Gateway
API Security Checklist is a fundamental security protocol that protects backend services during deployment. A centralized component implements various security policies, which include secure authentication and authorization protocols for API endpoint access control. Your API gateway lets you set up rate measures that stop denial-of-service attacks and perform strong security checks on incoming data to shield your backend. In addition to security features, an API gateway delivers usable capabilities for centralized logging and comprehensive monitoring alongside efficient traffic management, decreasing your API infrastructure’s attack surface and improving its resilience.
How Qualysec Technologies Can Help
Qualysec Technologies delivers expert penetration testing services that help your API Security Checklist become more resilient against current and upcoming threats. Our detailed API infrastructure analysis methods detect security weaknesses that basic protection strategies cannot find.
Our simulations of real-life cyberattacks reveal vulnerabilities that lead to actionable recommendations and repair plans for you to implement. Through detailed reports from Qualysec, your development teams can establish secure development practices that meet industry standards. After partnering with our team, you will get ahead of threats through proactive defense methods, which enhance your API security performance to protect critical data while establishing better trust relationships with users and stakeholders.
Talk to our Cybersecurity Expert to discuss your specific needs and how we can help your business.
Conclusion
API Security Checklist should be considered an absolute requirement within the present interconnected digital world. Your attack surface will decrease strongly when you properly execute these 15 steps, which start with robust authentication and authorization before focusing on meticulous input validation and rate limiting. Protecting APIs represents an enduring workflow that evolves beyond single immediate responses. Your API ecosystem requires continuous monitoring, regular security audits, and keeping up-to-date on the latest threats to preserve resilience and trustworthiness. Your essential data and application integrity remain safe when you prioritize these security measures with leaders like Qualysec Technologies!





























































































































































































































































































































































































































































































































0 Comments