As Software as a Service (SaaS) applications gain recognition, more and more customers are requesting expert examinations and advice on SaaS security assessments. Many businesses are concerned regarding the safety of SaaS apps when they embrace fresh innovations and consequently are looking for an assessment of safety that identifies potential dangers. As the usage of SaaS has increased, more and more information that had been previously saved in physical environments is currently kept in the clouds by SaaS providers on behalf of the customers they serve. This emphasizes the necessity for businesses to analyze the safety capabilities and risks of every SaaS solution. Although businesses firmly support a holistic plan, this blog will primarily concentrate on the steps and what to look for when performing a SaaS security Assessment.
What is SaaS Security?
SaaS security is a broad phrase that encompasses various protective and reactive procedures used by service suppliers to keep business applications and products secure for consumers. Penetration tests, evaluating vulnerabilities, firewalls, and entry restrictions are just a few examples. Because our topic will be covering SaaS security assessment, our conversation will mostly focus on VAPT. However, we will include the basic standards for SaaS security, as well as numerous concepts and guidelines, in our blog.
Why Is Security Assessment Important for SaaS Organizations?
SaaS is the logical choice for organizations looking to do better with the least. Implementing software as a service involves enhancing efficiency, boosting velocity, and accelerating development. One can’t eliminate these functions from SaaS systems, regardless of the purpose of safety.
However, if a SaaS service provider is hacked and abused, it has implications for many organizations that rely on the service in some capacity.
Because of this, SaaS apps are constantly running, typically available, overshared, and unnecessarily acknowledged by customers who misinterpret security check reports that frantically attempt to keep an eye on fragmented data.
It is precisely as unclear the way it seems in the preceding statement. Consequently, SaaS applications represent ongoing security hazards to both the companies that offer them as well as the countless numbers of enterprises that utilize them.
Top Security Guidelines for SaaS Consumers and Companies
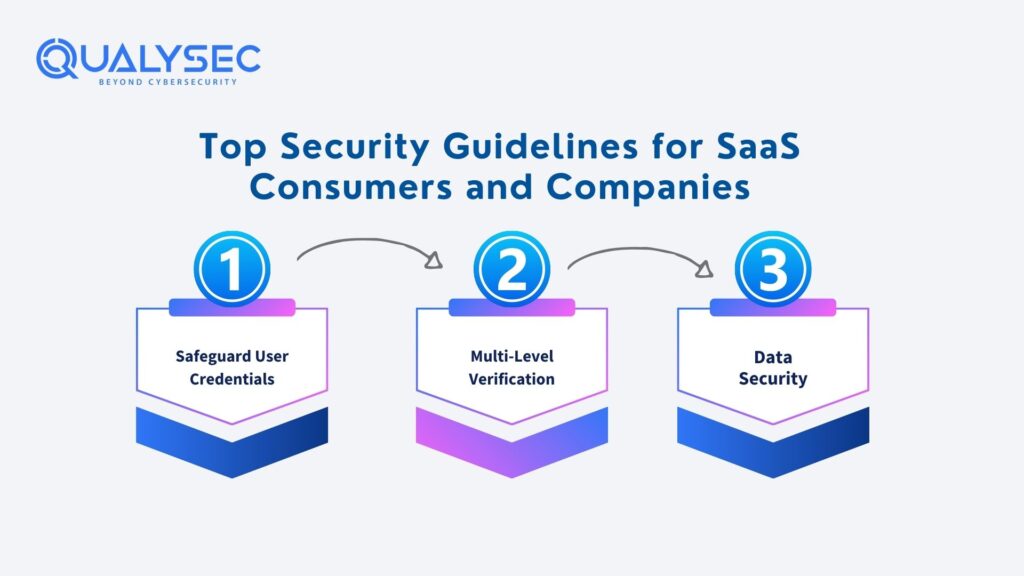
1. Safeguard User Credentials
It is usually best for businesses to provide people permission for a set amount of time and later extend this privilege as required. This guarantees that a person whose identity is no longer connected with the organization does not maintain accessibility. Apart from that, one must check accessibility frequently. Keep an eye on the rights assigned to particular workers and how they behave on the application. Encouraging and facilitating suitable use is the company’s responsibility. Making it simpler for individuals to have accessibility to a service whenever they desire it, ensuring that they won’t have to be afraid to give it up when they do not need it.
2. Multi-Level Verification
We’ve all heard about multiple-layer verification, which means you are unable to sign into the account you have with a single pair of identification, which is due to Gmail’s subsequent adoption of the two-step procedure. Multilayered verification has evolved into a variety of formats.
3. Data Security
By using a software as a service (SaaS) approach users entrust the information you provide to the software company that provides it. Should a user provide your information? If the company employs 3-4 software as service applications and consumers have the opportunity to evaluate their confidentiality agreements and accomplish a supplier evaluation, one can rely on the SaaS suppliers to maintain information securely; yet based on Netskope, the typical business employs 900+ SaaS programs.
All of the information one gives the supplier of software as a service must be secured. Confidentiality usually operates in three distinct manners.
- Customer-side Authentication
- Fully Homomorphic Encryption (FHE)
- Enterprise key management (EKM)
- Discovering and inventorying SaaS use.
One can not evaluate or safeguard anything that you cannot perceive. This is precisely what occurs when using SaaS applications. Companies frequently become distracted by the sheer number of things that utilize at any given moment. The primary component of any SaaS security evaluation is to identify each of the technologies in usage and develop a database of them.
Frequent vulnerability evaluations and Penetration Testing
This holds the same importance for SaaS suppliers and consumers. Frequent VAPT might help companies detect safety risks in their SaaS applications. Software as a service company should undertake frequent penetration testing as a component of its safety protocols to guarantee that its web app remains vulnerable to large-scale assaults.
Employing a VAPT supplier to perform frequent SaaS security management is an ideal choice because it reduces the burden and provides a reliable inspection of the systems one uses.
What function does penetration testing perform in SaaS security assessments?
The term penetration testing, usually shortened as pentest, represents the process of performing a hacker-style assault on infrastructure to identify security holes. Give it some time pen testing not only detects risks, but also leverages vulnerabilities to get knowledge about how they work, how difficult they are to take advantage of, what kind of destruction a hacker could cause through abusing them, and precisely what the possible price for an intrusion entails. A SaaS security company may guarantee that its solutions are secure for customers by doing frequent pen testing. They may also provide the pentest accreditation as a guarantee to customers about the security of the SaaS product. Many SaaS consumers demand to acquire a SaaS supplier security assessment study before moving their company to a SaaS service.
QualySec Technologies—The Best SaaS Security Assessment Company
There are several things that a SaaS developer has to undertake. That is precisely why it is vital to choose a company that you can completely rely on to supply over 100 percent of the items you need to keep your company secure and troubleless. Here’s when QualySec kicks up. Our professional crew is fully capable of applying the highest SaaS security requirements listed before, alongside others. Our thorough evaluation experience will provide you with suitable safety features depending on the functions performed by our SaaS, what you want, and your domain of specialization.
Conclusion
The majority of today’s organizations are held jointly through SaaS apps, that serve as an adhesive. Because one cannot comprehend doing a full day of labor with no login onto any SaaS support, one must be conscious of SaaS risk factors and the significance of regular SaaS security assessments.
We’ve addressed a variety of SaaS safety standards and rules, and every one of them breaks up into a few basic guidelines: provide permission only in cases where it is required to recognize abuse, analyze, and clean up.
A competent SaaS security assessment solution can help you with all of these tasks effortlessly. The real issue is whether or not you are prepared to apply boundaries to the software as a service intake.



































































































































































































































































































































0 Comments