Key Takeaways
- Network security audit helps to find weak points, improper configurations, and any other gaps within the regulations before attackers exploit them.
- Illustrating 6 types of audit procedures, compliance, and cloud audits among them, there is no unanimous way of selecting the most effective one; however, it all depends on your risk profile.
- The audit procedure has adopted a time-tested 7-step model: scoping, asset discovery, scanning, manual testing, policy review, reporting, and remediation.
- The majority of organizations are supposed to undergo audits at least once a year; the fields of finance, healthcare, and government are also expected to undergo audits at least once in a quarter or after a significant change in the infrastructure.
- There is a difference between a network security audit and even a security risk assessment – understanding how to make the difference ensures an organization does not end up spending on security one more time.
Introduction
Check Point Research noted that cyberattacks grew 75 percent in Q3 2024 with respect to Q3 2023. Global cybercrime costs were USD 11.3 trillion in 2026, and the IBM 2025 India breach cost was estimated at 22 crores. According to Statista, cybercrime is expected to reach a cost of 15.63 trillion all over the world by the year 2029. These statistics are an indication of a fact that any organization must deal with: your network has been susceptible to attack, and simply succeeding once has to be enough on their part. The best way to locate and address security vulnerabilities before the malicious actors take advantage of them is to conduct a network security audit. However, there are numerous organizations that either avoid any auditing or make the process on the surface, or a checkbox exercise, to be able to comply with standards.
In this guide, the reader has a clear understanding of what entails a network security audit, how one should carry out the audit, the tools and frameworks used, and how one can ensure to avoid the pitfalls that leave organizations vulnerable yet the audit is conducted.
What Is a Network Security Audit?
A network security audit is an official, systematic examination of network infrastructure, which includes its hardware, software applications, settings, access rules, and security regulations of an organization to help identify vulnerabilities, confirm adherence, and enhance overall cyber resilience.
A full security audit uses a scan, unlike a single automated scan, to analyse your overall security stance: device settings, firewall policies, user access privileges, encryption policies, patch status, incident response policies, and institutions with regulatory requirements.
The cost of a 2024 DIB report, the IBM Cost of a Data Breach Report, estimated that the median breach would cost $4.88 million, the highest since the report existed. According to Check Point Research, the number of cyberattacks around the world have risen by 75 percent per year. Companies that do not engage in routine network security audits are not simply engaging in a calculated risk, but opening the door.
Network security audit includes:
- VLAN settings, WLAN segmentation, and architecture.
- Firewall policies and access control policies.
- MFA, access privileges, and user identity.
- Endpoint and device scanning of vulnerability.
- Status of patch management in OS, firmware and applications.
- At rest and in transit encryption standards.
- Ready and testing Incident response plan readiness.
- The agreement mapping in relation to GDPR, HIPAA, PCI-DSS, ISO 27001, NIS2, DORA, NIST CSF 2.0, and CMMC 2.0.
Network Security Audit vs. Risk Assessment vs. Penetration Test
These three terms are used interchangeably and incorrectly. Buying the wrong service wastes budget and leaves real gaps unaddressed.
| Features | Network Security Audit | Security Risk Assessment | Penetration Test |
Primary Purpose | Verify controls against known standards | Identify & quantify business risk | Simulate real-world attacks |
Scope | Pre-defined network infrastructure | Entire security program | Specific systems or segments |
Output | Pass/fail findings, remediation list | Risk register, risk ratings, roadmap | Exploitation report, proof-of-concept |
Frequency | Annual or compliance-driven | Annual or when risk changes | Annual or post-change |
Best For | Compliance validation | Strategic security planning | Technical gap validation |
Quick Rule: When it is obligatory for a regulator, then it is an audit. In case the leadership is interested in knowing about risk, it is an assessment. There is something to be hacked, in case you need to know about it – it is a penetration test.
Types of Network Security Audits
Audits are not all-purpose-built alike. The selection of a type to use hinges on your industry, compliance requirement and infrastructure.
Compliance Audit
Confirms that your network has been shown to achieve a particular regulatory standard – HIPAA, PCI-DSS, ISO 27001, GDPR, NIS2 (a compulsory EU directive, effective in October 2024), or DORA ( EU financial sector, live in January 2025). Generates evidence to be provided by regulators and auditors.
Internal Network Audit
Issued by your internal security staff regularly. Economical in terms of continuous hygienic supervision between external audits. Weakness: internal teams are predisposed to blindness on the issues that they created or accepted.
External Network Audit
Conducted by a registered third-party company. Delivers unbiased results, state-of-the-art equipment, and enhanced trust by the regulators, clients, and insurers. Mandated on formal compliance cycles, post-breach auditing, and M&A security due diligence.
Vulnerability Assessment Audit
Appeals towards automated scanning to list recognized CVEs based on CVSS score. Frequently, the initial step in a larger audit engagement is not a substitute for the complete process.
Wireless Network Audit Investigates Wi-Fi Networks
SSID, encryption algorithms (WPA3 vs WPA2), rogue access points, guest networks, wireless network segmentation, and wireless network intrusion.
Cloud Network Audit
Just more than 45% of all breaches of cloud assets (IBM 2024), which is an asset that is now inherently required whenever an organization utilizes AWS, Azure, or GCP. Includes IAM misconfigurations, insecure open storage buckets, unencrypted data, unsecure API gateways, and cloud-native firewall rules.
Why Network Security Audits Matter in 2026
- Prevent Known Vulnerabilities: Before the Attackers Identify The 2024 Known Exploited Vulnerabilities landings by CISA demonstrated that 88% of breaches had vulnerabilities that were known and had a patch. These gaps are closed proactively by the regular audit.
- Meet Regulatory and Legal Obligations: GDPR fines minus EUR20 million or 4% global annual turnover. The non-compliance with PCI-DSS may lead to the termination of the card network. NIS2 encompasses formal audits of operators of critical services. Audits in the case of regulated industries are mandatory, not optional.
- Cut Cyber Insurance Premiums: In 2025, insurers will become habitual and mandatory to preserve evidence of security audits when issuing policies. Those organizations that submit annual reports on their audits are eligible to get reduced premiums and increased coverage limits.
- Cover Business Reputation and Client Trust: A single breach of the customer information results in long-term reputational damage. Organizations that have regular audits and publish them establish verifiably greater levels of trust among clients in the company, especially with B2B sales cycles.
- Enable Faster Incident Response: Audits test and actually stress your incident response plan – not merely your technology. Your team has become practiced, your playbooks are up to date, and the times of containment are significantly shorter when an incident happens.
Benefits & Importance of Network Security Audits for for Businesses
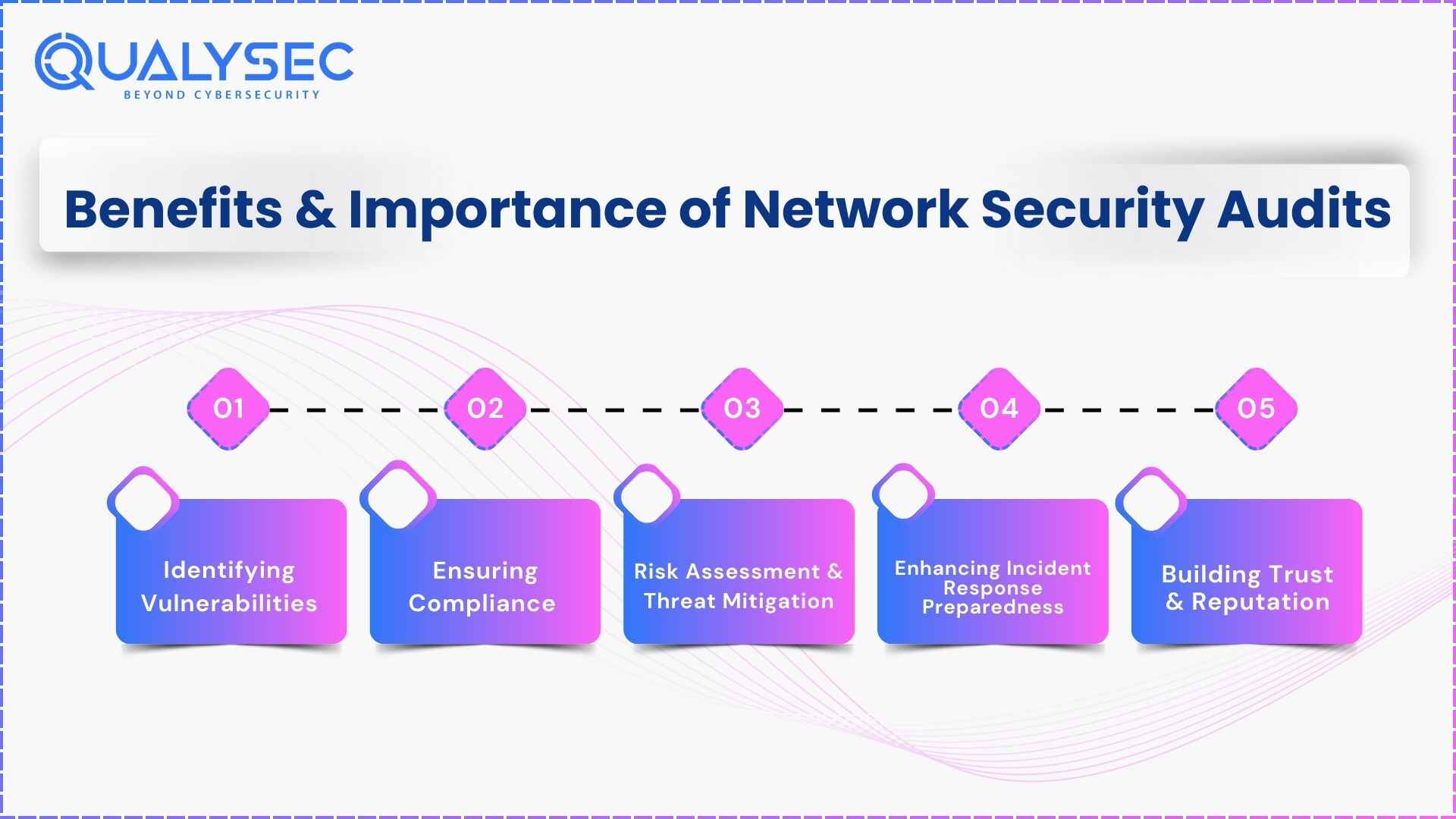
The benefits and importance of network security audits are:
1. Identifying Vulnerabilities:
A network security audit helps detect potential security flaws such as outdated software, weak authentication protocols, and misconfigurations that could be exploited by cybercriminals. Addressing these vulnerabilities proactively strengthens the organization’s security posture.
2. Ensuring Compliance
Many industries must comply with regulatory frameworks such as GDPR, HIPAA, PCI-DSS, ISO 27001, and SOC 2. Regular security audits help organizations stay compliant, avoid hefty fines, and build trust with customers and stakeholders.
3. Risk Assessment & Threat Mitigation
By evaluating the security risks associated with network infrastructure, businesses can prioritize security efforts and allocate resources effectively to mitigate potential threats before they lead to cyber incidents.
4. Enhancing Incident Response Preparedness
A security audit helps organizations fine-tune their incident response and disaster recovery plans, ensuring they are well-prepared to detect, contain, and recover from cyber threats swiftly.
5. Building Trust & Reputation
Regular security audits demonstrate a commitment to cybersecurity, fostering trust among clients, partners, and regulatory bodies while protecting sensitive data from cybercriminals.
Key Aspects to Check During Network Security Audit
When you carry out a network security audit, you must explore various components to guarantee the security, confidentiality, and availability of the network. Here are key aspects to check:
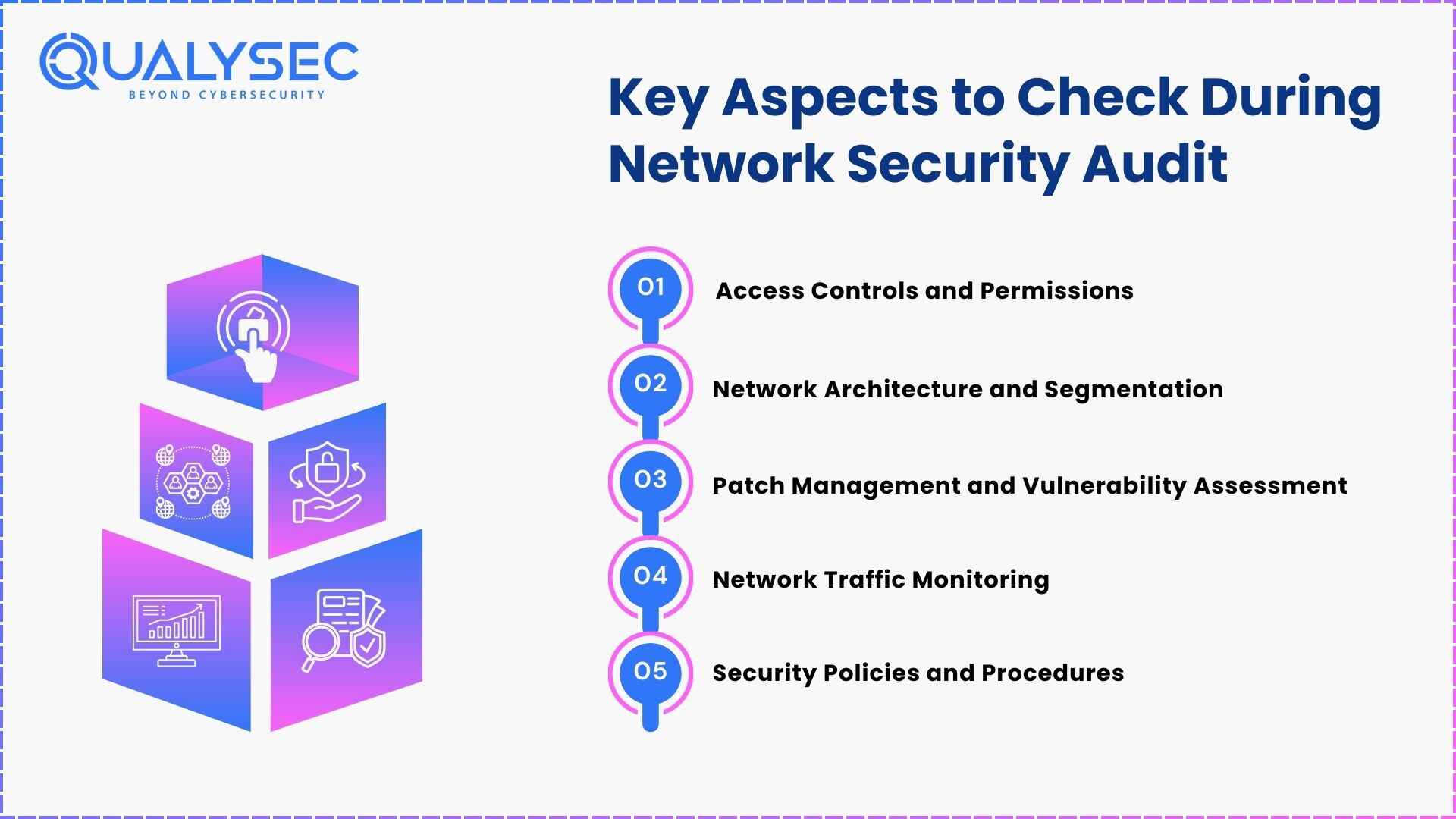
1. Access Controls and Permissions:
Examine access controls and permissions configured on network devices, servers, and applications. Configure access privileges correctly by adhering to the principle of least privilege, ensuring that people or systems have only essential access permissions and avoiding overly permissive access.
2. Network Architecture and Segmentation:
Evaluate the network architecture that guarantees correct segmentation and isolation of valuable data and critical network resources. Ensure proper implementation of segmentation controls by using firewalls, VLANs, and ACLs correctly to prevent unauthorized communications and lateral movement within the network.
3. Patch Management and Vulnerability Assessment:
Measure the efficiency of the patching management structure and process for the network devices, servers, and application endpoints. Hence, conduct vulnerability assessments to find and eliminate security vulnerabilities in network infrastructure components involving routers, switches, and firewalls.
4. Network Traffic Monitoring:
Review network traffic monitoring and intrusion detection systems to identify and respond to malicious activities and security incidents efficiently. Evaluate the network traffic logs, alerts, and anomalies for indicators of unauthorized access or uncommon activities on the network.
5. Security Policies and Procedures:
Evaluate the effectiveness of security procedures and policies covering network security practices, such as password management, encryption standards, and authorization. Make sure that security rules follow the industry standards and the rules of a regulatory body and that all employees know their roles and responsibilities concerning network security.
How to conduct a comprehensive network security audit?
A network security audit is an essential procedure that aims to improve an organization’s security posture. The following is a complete guide to an organization’s IT security audit process.
Steps involved in a network security audit process
Step | Phase | What Happens | Key Output |
1 | Scoping & Planning | Define audit boundaries, objectives, frameworks, and methodology. Agree on what’s in scope: on-prem, cloud, OT/IoT, remote endpoints. | Scope document, rules of engagement |
2 | Asset Discovery & Inventory | Enumerate all network devices, servers, endpoints, cloud assets, and shadow IT. You cannot audit what you cannot see. | Complete asset register |
3 | Automated Vulnerability Scanning | Run tools across all in-scope assets to identify known CVEs, open ports, and misconfigurations. | Vulnerability report with CVSS scores |
4 | Manual Configuration Review | Examine firewall rule sets, ACLs, VPN configs, AD/LDAP policies, and cloud IAM policies that automated tools miss. | Configuration audit findings |
5 | Penetration Testing | Simulate real-world attacks against prioritized findings to confirm whether vulnerabilities are actually exploitable. | Exploitation report with proof-of-concept |
6 | Policy & Compliance Review | Audit security policies, incident response procedures, data classification standards, and compliance evidence. | Policy gap analysis, compliance mapping |
7 | Reporting & Remediation | Document all findings with severity ratings, business impact, and actionable remediation steps. Schedule retesting. | Formal audit report, remediation roadmap |
Pro Tip: The audit report is not a one-time project. Re-test the schedules within 30-60 days after remediation to prove that the fixes were working, and no regression took place.
Want to see a real network security audit report? Download by clicking the link below!
Latest Penetration Testing Report

Network Security Audit Checklist
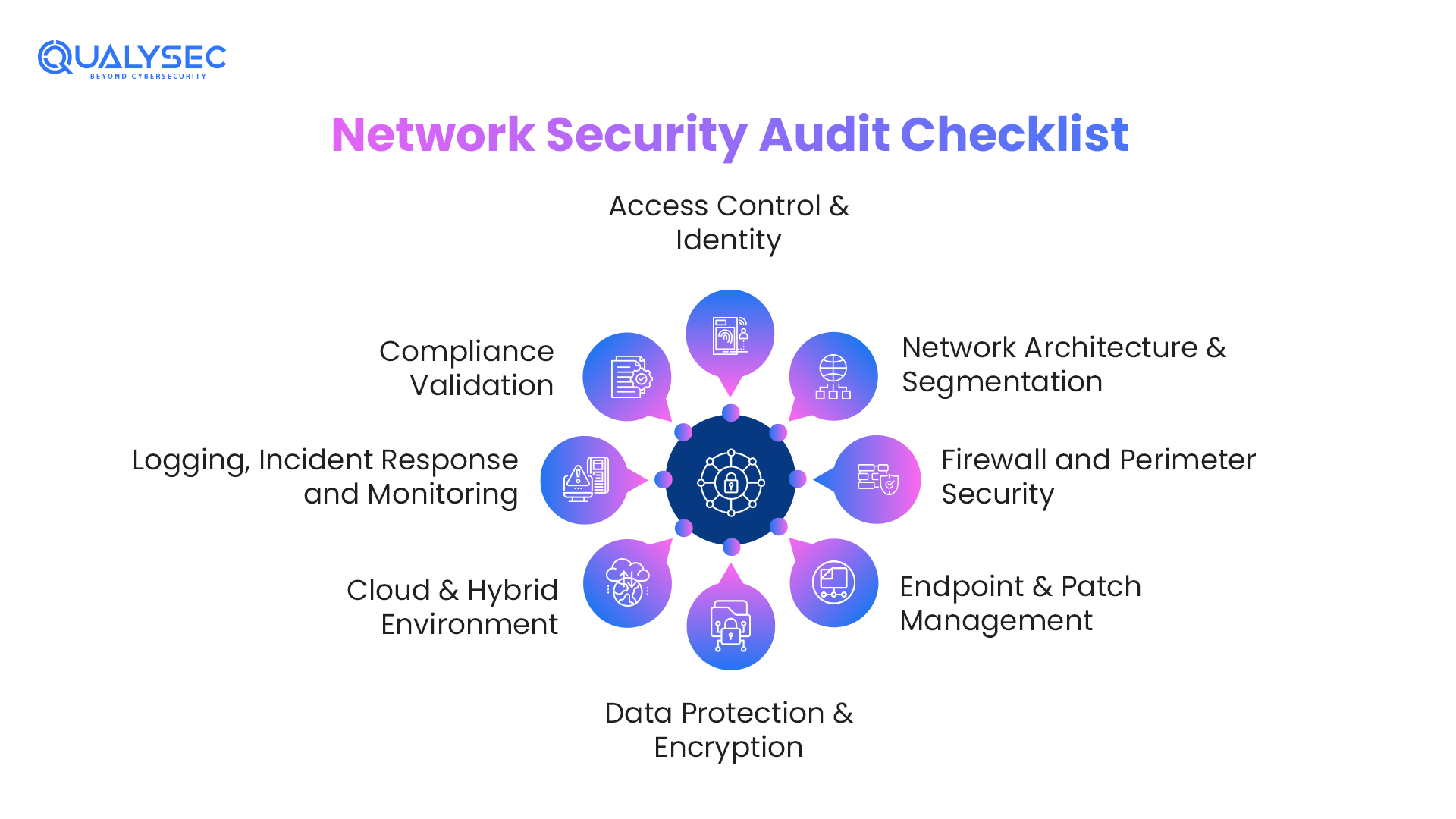
Apply this as your base control validation system before, during, and after any audit engagement.
i. Access Control & Identity
- MFA was imposed on all privileged and remote accounts.
- Accounts of inactive users are terminated within 30 days of leave.
- The least-privilege principle was used — there were no extra rights of the administration.
- Inventoried and reviewed access to shared/service accounts.
- A Privileged Access Management (PAM) solution is available.
ii. Network Architecture & Segmentation
- Critical assets (PII, financial data, OT systems) are segregated into different segments.
- Guest WIFI is not connected to the corporate network.
- Principles of Zero Trust Architecture are reported and at least partially implemented.
- ACL-limited inter-VLAN routing was used in configuring VLANs.
- DMZ is applied to all services that face the internet.
iii. Firewall and Perimeter Security
- Reviewed firewall rule sets – no any-any rule sets, no old shadow rule sets.
- Active and signature databases up to date.
- VPN/Zero Trust Network Access (ZTNA) Remote access, no open RDP.
- Any unutilized ports and services are disabled.
iv. Endpoint & Patch Management
- All OS and application patches implemented in the context of SLA (critical patches: 24-72 hours)
- Endpoint Detection and Response is installed on all terminals.
- All network hardware (routers, switches, firewalls) would be updated with firmware.
v. Data Protection & Encryption
- Encrypted ad-hoc data (AES-256) and in transit with minimum settings: TLS 1.2 and best settings: TLS 1.3.
- Not only in the case of back-ups, but also every quarter, the integrity tests were implemented and encrypted.
- No production expired certificates.
vi. Cloud & Hybrid Environment
- Reviewed cloud IAM policies; no excessively liberal roles.
- Audited public cloud storage buckets. No accidentally public buckets.
- Cloud Security Adobe is in place.
- Third-party API keys inspected and changed.
vii. Logging, Incident Response and Monitoring
- SIEM is an active alert on the critical event types.
- Log retention complies with retention requirements (1-7 years usually)
- The Incident Response Plan has undergone a tabletop exercise within 12 months.
Viii. Compliance Validation
- Relevant framework mapped (HIPAA / PCI-DSS / ISO 27001 / GDPR / NIS2 / NIST CSF 2.0 / CMMC 2.0)
- Records of the final audit were recorded and stored.
- Annual third-party vendor security inspection.
Did You Know?
Shadow IT is the cause of about 40 percent of network vulnerabilities, as workers use unauthorised cloud applications or personal routers as invisible points that system security does not detect.
How Often Should You Conduct a Network Security Audit?
Audit frequency should be driven by your industry risk profile and compliance obligations — not just budget convenience.
Organization Type | Recommended Frequency | Key Driver |
All organizations (baseline) | Annually | General hygiene and compliance |
Financial services (PCI-DSS, DORA) | Quarterly | Regulatory requirement |
Healthcare (HIPAA) | Semi-annually | HIPAA Security Rule |
Government / Defense (CMMC 2.0) | Annually + post-change | Federal mandate |
Critical infrastructure (NIS2) | Annually at minimum | NIS2 Directive (EU) |
Post-breach / post-M&A | Immediately (event-triggered) | Risk response |
After a major infrastructure change | Within 30 days | Change management |
Roles in Network Security Audits – Who Conducts Them?
Network security audits are performed by certified cybersecurity professionals and third-party security firms specializing in IT security. Key roles include:
- Certified Information Systems Auditors (CISA)
- Certified Information Security Managers (CISM)
- Certified Ethical Hackers (CEH)
- Network Security Engineers
These experts work closely with IT teams to perform audits, analyze results, and implement security enhancements based on industry standards.
Costs Associated with Network Security Audits
The cost of a network security audit varies depending on factors such as:
- Scope and complexity of the audit
- Size of the organization’s network
- Compliance requirements
- Security tools and software licenses
How Much Does a Network Security Audit Cost?
Organization Size | Audit Type | Estimated Cost (2025) |
Small Business (<100 employees) | Basic external audit + vuln scan | Less than $5,000 |
Mid-Market (100–1,000 employees) | Full audit + penetration test | Less than $25,000 |
Enterprise (1,000+ employees) | Comprehensive audit + compliance | Less than $100,000+ |
SaaS / Automated Scanning Only | Continuous monitoring tools | Less than $2,500/month |
PCI-DSS QSA-led Compliance Audit | QSA engagement | Less than $50,000 |
Investing in a security audit can save businesses from the financial and reputational damage caused by cyberattacks.
Tools For Performing Effective Network Security Audits
Security testing, which includes tasks like vulnerability scanning, code analysis, penetration testing, and security audits, employs a variety of tools. Therefore, here’s a list of frequently used tools to help you better understand the technologies used in network security audits:
Audit Phase | Tool | Type | Best For |
Asset Discovery | Nmap | Free / Open Source | Network mapping, port scanning |
Asset Discovery | Lansweeper | Commercial | Full IT asset inventory incl. cloud |
Vulnerability Scanning | Nessus (Tenable) | Commercial | Comprehensive CVE detection |
Vulnerability Scanning | Qualys VMDR | Cloud SaaS | Enterprise vulnerability management |
Vulnerability Scanning | OpenVAS | Free / Open Source | SMB entry-level scanning |
Penetration Testing | Metasploit | Free / Commercial | Exploitation and validation |
Penetration Testing | Burp Suite | Commercial | Web application and API testing |
Traffic Analysis | Wireshark | Free / Open Source | Packet capture and analysis |
SIEM / Monitoring | Splunk | Commercial | Log correlation, threat detection |
SIEM / Monitoring | Microsoft Sentinel | Cloud SaaS | Azure-native AI-driven SIEM |
Cloud Audit | Prowler | Free / Open Source | AWS, Azure, GCP posture checks |
AI-Driven Detection | Darktrace | Commercial | Autonomous AI threat detection |
Qualysec’s Security Audit Solution
To provide accurate and trustworthy results, network security audits demand knowledge and experience. Being a pioneer in the penetration testing industry, Qualysec is unique. Further, to offer thorough security audit services, we use both automated tools and manual testing methods. With the help of Qualysec, you can be confident that you will receive high-quality security audit services that match your specific requirements.
As a leading penetration testing and security audit firm, Qualysec provides services such as:
- Comprehensive network security audits using automated and manual testing techniques
- Detailed audit reports with prioritized vulnerabilities and remediation steps
- Compliance support for GDPR, HIPAA, PCI-DSS, and more
- Continuous security monitoring and retesting services
What must a Network security auditing report include?
An action-oriented professional audit is required, not merely a list of a report, but also a requirement. A report listing the list of the vulnerabilities without context, business impact, and explicit remediation recommendations is incomplete.
- Executive Summary: 1-2 page business-level summary of highlights, overall security posture rating, and the top 3 suggestions. C-suite and board-oriented.
- Scope & Methodology: It should be clearly documented what was tested, how it was tested, as well as what has been specifically left out.
- Asset Inventory: Full inventory of all the systems and assets involved in the audit.
- Findings Register: Each vulnerability, vulnerability severity (Critical/High/Medium/Low), CVSS score impacted, affected asset, description, business impact, and recommended fix.
- Compliance Mapping: Framework-by-framework information on compliance status, passed, failed, or not applicable.
- Remediation Roadmap: Key action plan with ownership, schedules (immediate /30-day / 90-day/ long-term), and approximate effort.
- Retestation: In a follow-up engagement, confirmation of the successful completion of critical and high findings.
By choosing Qualysec, businesses can ensure their networks remain secure, compliant, and resilient against cyber threats.
Talk to our Cybersecurity Expert to discuss your specific needs and how we can help your business.
Conclusion
With cyber threats evolving rapidly, network security audits are more critical than ever in 2025. They help organizations identify vulnerabilities, enhance security measures, ensure compliance, and build trust with stakeholders.
Partnering with a trusted cybersecurity firm like Qualysec ensures that your network remains secure, compliant, and resilient against cyber threats.
Ready to secure your network? Schedule a free consultation with Qualysec’s cybersecurity experts today!
FAQs
Q. What is a security audit?
Ans: A security audit is a thorough examination of a business infrastructure including its information systems, processes, and security policies. The main purpose is to identify the weak spots, assess the risks, and prepare measures to improve the whole level of security.
Q. Who does security audits?
Ans: Security audits are usually done by authorized cybersecurity professionals or firms specializing in the field. They check the efficiency of the safety measures, detecting weak spots and giving development proposals. Therefore, these audits are vital for the preservation of the integrity and security of digital systems and networks.
Q. What should a network security audit report include?
Ans: The network security audit report must cover the vulnerabilities, risks, compliance state, and remediation suggestions. Furthermore, it will highlight the network architecture, security policies, assessment methodologies, and a detailed action plan for enhanced security measures.












































































































































































































































































































































































































































































































































































































































































































0 Comments