Notably, one of the most sophisticated automated supply chain attacks in open source history happened, where a tenacious, self-propagating cyber worm compromised over 17+ software packages across npm and PyPI registries.
The campaign “Mini Shai- Hulud” is a supply chain attack which was initiated in late April 2026 and surged in mid- May. The threat group, TeamPCP, has deployed this automated system, called a worm that operates without any human intervention. These packages have hundreds of millions of downloads and are supported by tens of thousands of repositories.
The Threat Actor/Group: TeamPCP
TeamPCP is an organized cyber criminal group that has been engaged in high-velocity cross-ecosystem campaigns through supply chains since February 2026. The group focuses explicitly on security adjacent software and trusted development platforms like GitHub, Docker Hub, npm, Open VSX and PyPI.
How the Attack Works: Fully Autonomous Propagation
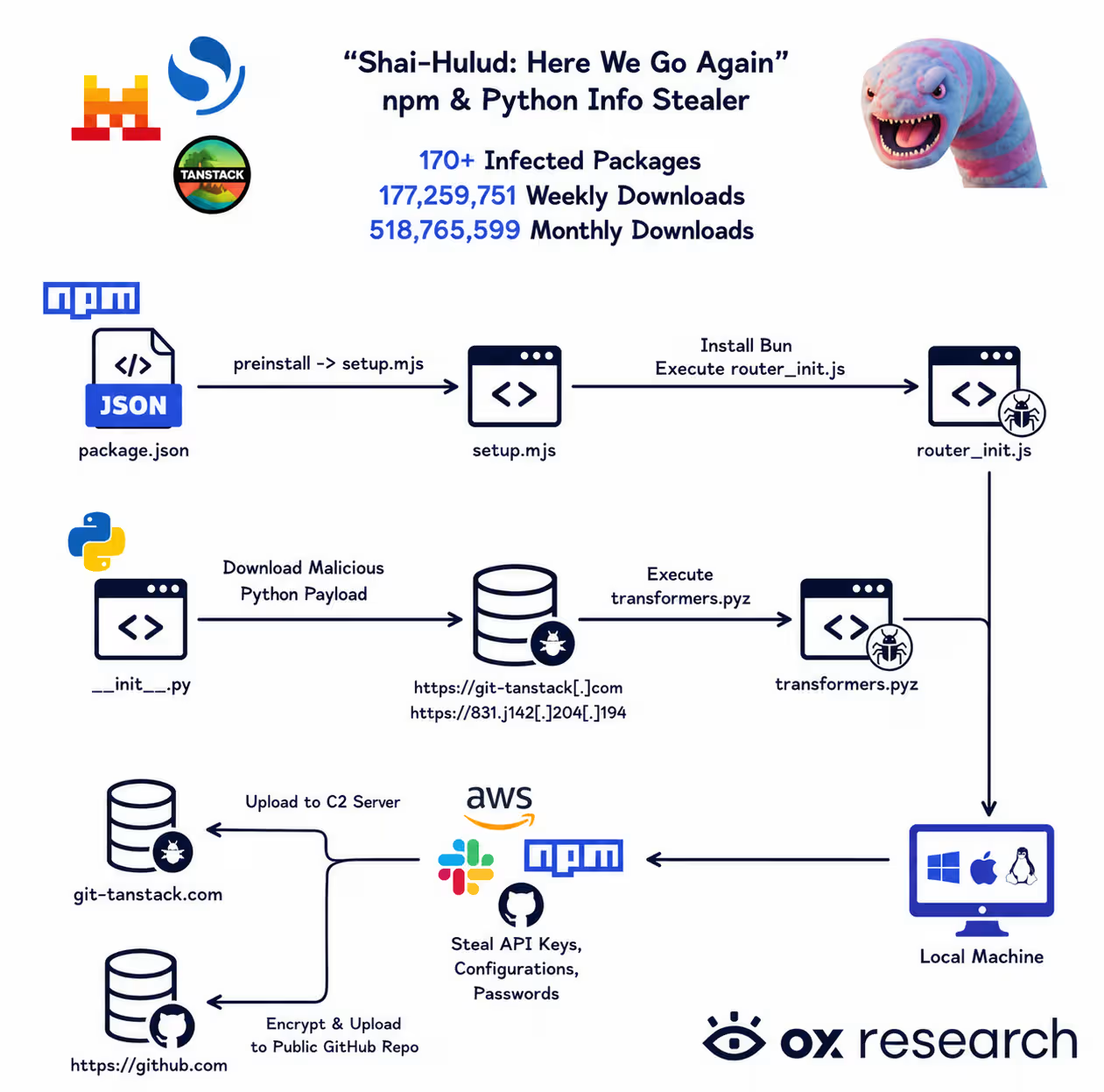
Named after the sandworm from Frank Herbert’s Dune (following earlier “Shai-Hulud” and “Sha1-Hulud” variants from 2025), Mini Shai-Hulud is a true worm designed for modern CI/CD and developer environments. It requires no ongoing human control once seeded.
The attack starts by hijacking a legitimate workflow on GitHub, especially those that run on the pull_request_target trigger, or orphaned commits with an OpenID Connect (OIDC) trusted publishing set. Attackers obtain short-lived OIDC tokens from CI runners (sometimes via process memory scraping to defeat secret masking) to authenticate themselves for npm publish access using valid SLSA Build Level 3 attestations. This circumvents 2FA and conventional detection.
Once a package is poisoned, it employs multiple vectors:
- preinstall hooks and optionalDependencies pointing to malicious orphan GitHub commits (e.g., in a TanStack router fork).
- A massive obfuscated payload (router_init.js, ~2.3-11.7MB when deobfuscated, SHA-256: ab4fcadaec49c03278063dd269ea5eef82d24f2124a8e15d7b90f2fa8601266c and related) that uses the Bun JavaScript runtime (smuggled as a living-off-the-land binary) to evade traditional Node.js environments.
- Heavy custom encryption: Strings obfuscated via PBKDF2 (200,000 iterations, salt “svksjrhjkcejg”), AES-256-GCM with RSA-4096 key wrapping for exfiltration.
The payload conducts a thorough credential theft attack on:
- GitHub PATs, npm tokens, GitHub Actions secrets
- AWS IMDSv2, GCP, and Azure credentials for the cloud provider.
- They use Kubernetes service accounts and HashiCorp Vault tokens.
- On local secret files and SSH keys (100+ paths)
Exfiltration occurs through redundant channels: encrypted JSON files committed to attacker-controlled public GitHub repos with Dune-themed names (e.g., “kralizec-phibian-314”) and description “A Mini Shai-Hulud has Appeared.” Additional C2 includes Shai–hulud, Supply_chain_technique, Credential_stealing_technique, Trufflehog_tool, Typosquatting_technique, git-tanstack.com, Session P2P messenger, and “dead-drop” commits using phrases like “OhNoWhatsGoingOnWithGitHub:” for base64-encoded tokens.
Self-Propagation Without Human Intervention:
This is the worm’s most dangerous feature. Using stolen tokens, it:
- Displays all packages that can be published by a compromised maintainer.
- Clones repos, injects payload in tarballs/workflows.
- Raises the patch version.
- Auto Publishes malicious versions.
It also adds persistence to developer IDEs (.claude/settings.json, .claude/router_runtime.js, .vscode/setup.mjs) and implements “dead-man’s switches. These daemons (systemd services on Linux, LaunchAgents on macOS) are checking for these GitHub tokens every 60 seconds. Upon revocation of a token (40x error), the script will run rm -rf ~/ with that sinister warning “IfYouRevokeThisTokenItWillWipeTheComputerOfTheOwner”. It’s a 24-hour timeout to avoid any accidental triggers. There are geofenced and ignored Russian-language systems.
The worm entered PyPI to target related Python ecosystems and used the feeds from GitHub as a propagation vector and exfil channel.
Scope of Impact
The person or persons who were affected and what they were affected by.
Initial wave (April 29, 2026) hit SAP Cloud Application Programming Model (CAP) packages: @cap-js/sqlite (v2.2.2), @cap-js/postgres (v2.2.2), @cap-js/db-service (v2.10.1), and mbt (v1.2.48). These reliable packages allowed for speedy spreading.
It turned into a big deal by May 11-12:
- TanStack (npm): The popular open-source data fetching library TanStack is impacted by hundreds of packages (npm).
- Mistral AI: AI/ML library ecosystem breached. (2.4.6 on PyPI)
- OpenSearch: Search and analytics framework impacted (3.5.3, 3.6.2, 3.7.0, 3.8.0 (1.3M weekly downloads)
- SAP Developer Packages: Four npm packages that can be used to steal secrets
- UiPath: New libraries for the automation platform released by UiPath were compromised.
- The Guardrails AI: AI safety framework has been hacked. (0.10.1 on PyPI)
Total Impact
- 170+ packages breached on npm and PyPI.
- According to some reports, there are 400+ package artefacts reported on npm, PyPI, and Composer repositories.
- The NHS (UK National Health Service) issued a cyber alert CC-4781 in reference to the incident.
Data at Risk
The worm systematically collects:
- AWS, GCP and Azure cloud keys
- GitHub Personal Access Tokens
- HashiCorp Vault tokens
- Kubernetes secrets
- AI coding tool secrets revealed.
Immediate Remediation Steps
1. Audit Dependencies: Check for updates in package-lock.json, yarn.lock, poetry.lock, requirements.txt, and lock files from April 29, 2026. Use tools such as Snyk, npm audit or dependency scanners to search for vulnerable versions (e.g. GHSA-g7cv-rxg3-hmpx, CVE-2026-45321).
2. Rotate Credentials: Revoke and rotate all GitHub tokens, npm, cloud access keys (AWS, GCP, Azure), Vault tokens and K8S secrets. Assume exposure.
3. Inspect Environments:
- Look for persistence files: .claude/, router_init.js, setup.mjs, gh-token-monitor.sh, com.user.gh-token-monitor.plist.
- Look for suspicious repos on GitHub with Dune names or commit patterns.
- Monitor for files with SHA hashes listed in IOCs (e.g., 2ec78d556d696e208927cc503d48e4b5eb56b31abc2870c2ed2e98d6be27fc96).
4. Rebuild CI/CD Runners: Assume that all the latest CI runs are compromised. Reprovision Containers and Runners.
5. Dead-Man’s Switch Mitigation: Do not remove tokens out of the blue without isolating machines. Apply canary credentials, and watch for wipe scripts.
6. NHS/Healthcare Specific: UK health services are alerted to check systems using SAP, TanStack or AI Library and adhere to NCSC guidance to supply chain integrity.
Industry Response
TanStack has since withdrawn all of the affected versions and scrubbed their GitHub Actions cache, hardened workflows, and worked with npm security to eliminate malicious packages. Security researchers suggest exploring exposed credential activity, setting strict OIDC least-privilege policies, removing unwanted workflow triggers, and implementing SLSA higher levels and external attestations not on GitHub.
Why This Matters
Mini Shai Hulud is a new, dangerous type of supply chain attack: wormable (self-replicating), autonomous (no human required), and cross-ecosystem (npm, PyPI, Composer). By using legitimate SLSA Build Level 3 certifications, the packages are passed by typical security measures, thus making it extremely hard to detect the attack.
Affected packages should be considered a critical incident and be immediately used to prompt credential rotation and a forensic investigation. The campaign is still going strong, and the number of infected packages could increase if containment is not rapid.
“This is no compromise package-it’s a living being in our dependency graphs,” one researcher said. As AI coding assistants and AI agents without humans begin to be more common, worms like this may be seen more often than not.
Developers and organisations need to act on supply chain security – know for sure the version of everything, use SBOMs, vet dependencies and use air-gapped or vetted rebuilds of critical software. The list of impacted packages is growing as researchers are analyzing. TeamPCP isn’t stopping any time soon; the next big attack might be even deeper.
Qualysec’s Mechanism for Strengthening Supply Chain Integrity
The speed of this attack highlights a fundamental weakness in modern CI/CD trust models. Specifically, around OIDC token leakage and memory safety, that autonomous worms now exploit with surgical precision, as was already planned.
QualySec Technology identifies these vulnerability patterns through deep-tier technical audits and rigorous VAPT. By eliminating these blind spots, it ensures that automated pipelines stay a tool for deployment, not a channel for self-propagating malware.