Global cybersecurity leader DigiCert has been the victim of a recent cyberattack. This is a major concern in the cybersecurity industry, as attackers were able to gain access to the issuance of 60 Extended Validation (EV) Code Signing certificates in a clever social engineering scheme.
A Fatal “Screenshot”
The attack started on April 2 when a sophisticated threat actor reached out to DigiCert’s support system through a Salesforce-based chat system. The threat actor appeared to be a customer, requested technical assistance, and eventually sent a ZIP file, claiming to be a message from a screenshot of an error.
An “.scr (screensaver) file” was found in the archive of the file. On Windows, the system runs or stores .scr as native code. DigiCert’s endpoint defenses thwarted the first four attempts, but at the fifth attempt, the attackers were able to get past the security via the support analyst’s workstation, giving them a foothold.
A Ten-Day Blind Spot
A later investigation found a major containment failure. DigiCert was able to isolate the first compromised machine (ENDPOINT1) within 24 hours, but the attackers had already pivoted to an additional machine (ENDPOINT2). The second compromise was not discovered for 10 days, during which time the hackers were able to move freely about his company’s internal tools, from April 4 to April 14.
The Theft of “Gold Standard” Trust
The hackers took advantage of a “view-as-customer” function as part of the support portal. The developers created this tool for troubleshooting purposes, but it inadvertently provided the codes for the initialisation of accepted, but not delivered, EV Code Signing orders.
The attackers were able to steal these codes and then:
- Activate legitimate certificates in their own names.
- Bypass the rigorous identity verification usually required for EV status.
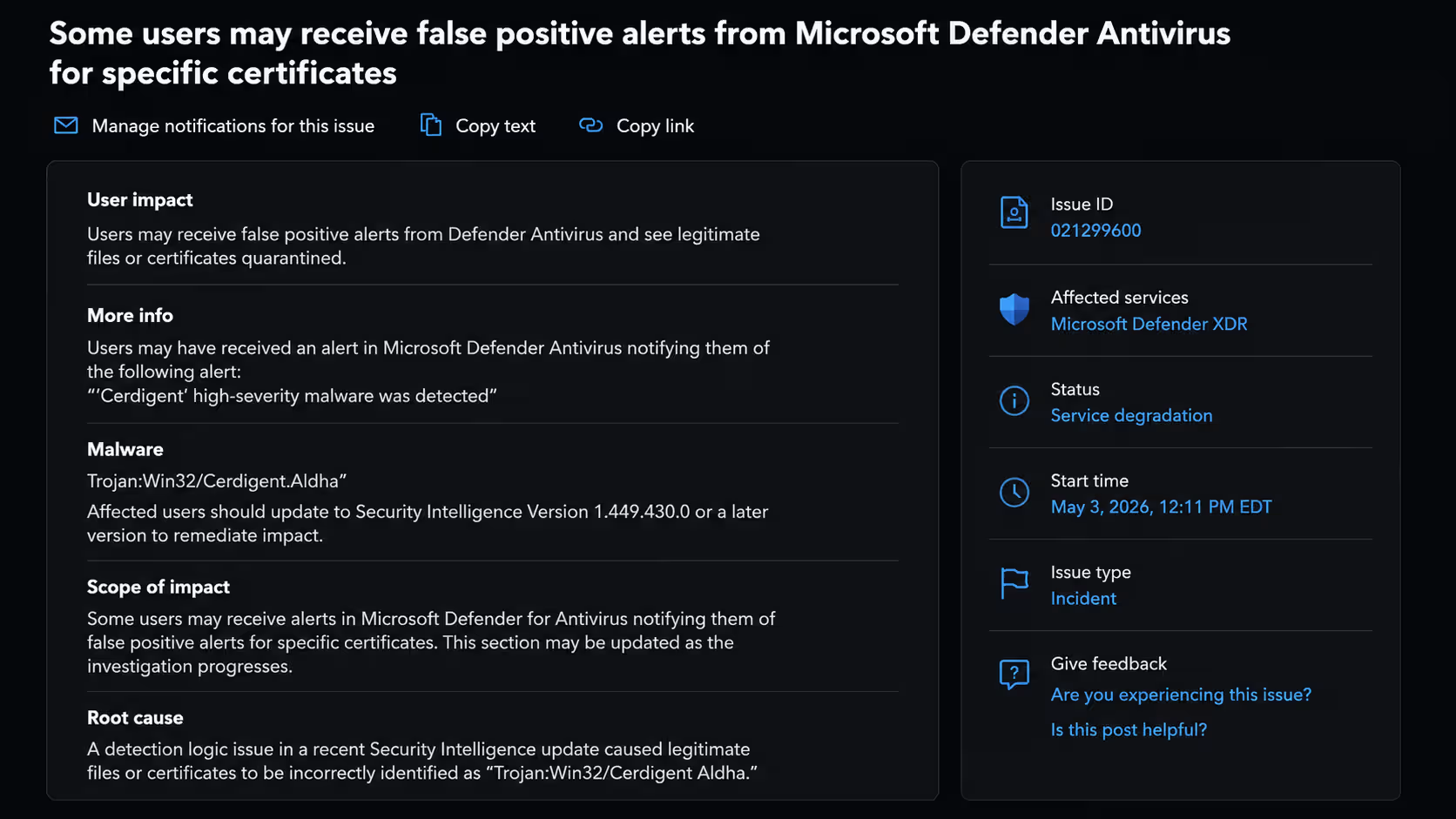
- Sign malicious software with “trusted” credentials that bypass Windows SmartScreen and antivirus filters.
The Impact: Stealing Certificates to the Zhong Stealer
The stolen certificates have been identified as part of the “Zhong Stealer” malware family by security researchers. This “stealer-RAT” combination is used to steal sensitive information and cryptocurrencies. A single e-crime group tied to the Chinese government appears to be using the stolen certificates known as GoldenEyeDog (APT-Q-27).
Emergency Response & Remediation
Since then, DigiCert has cancelled all 60 affected certificates, and the team has made emergency security upgrades:
- Feature Removal: Support staff can no longer view initialization codes.
- Identity Hardening: MFA teams have tightened the requirements, and the system administrators have disabled Okta FastPass for support portals.
- IP Blocking: The security team has blacklisted seven attacker-controlled IP addresses.
Industry Awareness
Security professionals are encouraged to immediately update their Certificate Revocation Lists (CRL) and OCSP responders. You should conduct a security audit of any internal “allow-lists” to make sure that none of the 60 revoked DigiCert certificates are being unwittingly trusted.
This incident is part of a pattern that experts say is becoming more common: Attackers are exploiting the human component of the digital supply chain, which threatens the trust in the internet globally.
Upcoming Maintenance
DigiCert has a scheduled maintenance window starting Saturday, May 9, 2026:
- Time: 22:00 – 24:00 MDT (Sunday, May 10, 04:00 – 06:00 UTC).
- Impact: Signing services (like PrimoSign) and certificate issuance APIs may be temporarily unavailable.
- Check your systems: Are you seeing any SSL/TLS connection errors or “untrusted” warnings in Windows today?






