The recent research has uncovered a serious vulnerability inside the Model Context Protocol (MCP), the standard that powers communication between AI agents, developed and maintained by Anthropic. The implications are significant and wide-reaching.
What Is MCP?
MCP is the backbone that allows AI agents and applications to connect with external tools, data, and systems. Millions of developers build on it daily, which is exactly what makes this discovery so critical.
What Was Found?
This is not a simple coding mistake. The researchers describe it as an architectural flaw built into Anthropic’s official MCP software kits across every supported programming language, including Python, TypeScript, Java, and Rust. Any developer building on MCP unknowingly carries this vulnerability into their product.
10 CVEs issued – MCP vulnerability findings
| CVE ID | Product | Attack type | Severity | Status |
|---|---|---|---|---|
| CVE-2025-65720 | GPT Researcher | UI injection / reverse shell | Critical | Reported |
| CVE-2026-30623 | LiteLLM | Authenticated RCE via JSON config | Critical | Patched |
| CVE-2026-30624 | Agent Zero | Unauthenticated UI injection | Critical | Reported |
| CVE-2026-30618 | Fay Framework | Unauthenticated web-GUI RCE | Critical | Reported |
| CVE-2026-33224 | Bisheng | Authenticated UI injection | Critical | Patched |
| CVE-2026-30617 | Langchain-Chatchat | Unauthenticated UI injection | Critical | Reported |
| CVE-2026-33224 | Jaaz | Unauthenticated UI injection | Critical | Reported |
| CVE-2026-30625 | Upsonic | Allowlist bypass via npx/npm args | High | Warning |
| CVE-2026-30615 | Windsurf | Zero-click prompt injection to local RCE | Critical | Reported |
| CVE-2026-26015 | DocsGPT | MITM transport-type substitution | Critical | Patched |
The flaw allows attackers to run commands directly on any vulnerable server, which gives them access to:
- User data
- Internal databases
- API keys
- Chat histories
The scale of exposure:
- 150 million+ downloads affected
- 7,000+ publicly accessible servers at risk
- Up to 200,000 vulnerable instances identified
- Commands successfully executed on six live production platforms
- Critical vulnerabilities confirmed in LiteLLM, LangChain, and IBM’s LangFlow
- 10 CVEs issued, all rated Critical or High
The flaw can be triggered in 4 ways:
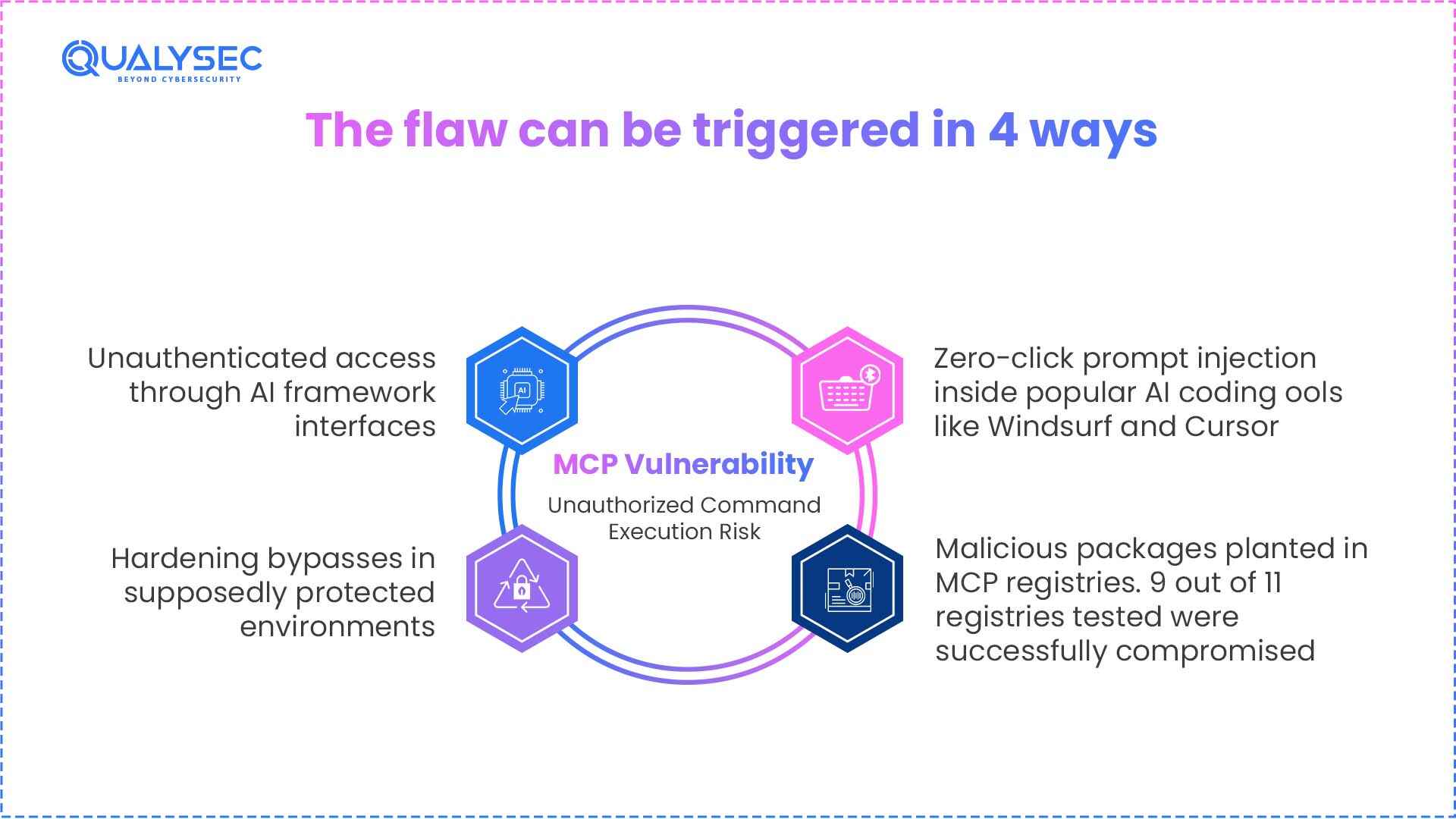
- Unauthenticated access through AI framework interfaces
- Hardening bypasses in supposedly protected environments
- Zero-click prompt injection inside popular AI coding tools like Windsurf and Cursor
- Malicious packages planted in MCP registries. 9 out of 11 registries tested were successfully compromised
Anthropic’s Response
The findings included repeated recommendations for fixes that could have protected all downstream users at once. Anthropic declined, calling the behavior “expected” and placing responsibility on individual developers to secure their own implementations. A quiet policy update followed, but the root problem remains unfixed.
What This Means
AI tools are being built and deployed faster than they are being secured. This incident makes that reality impossible to ignore. If your systems connect to AI tools built on MCP, now is the time to get them properly assessed, before someone else finds what you haven’t looked for.
Qualysec’s Take on Emerging Security Risks
Qualysec, a human-led, AI-powered penetration testing company, is prepared to deal with exactly this kind of threat landscape. As part of ongoing efforts to address modern security challenges, we continue to study vulnerabilities in emerging technologies, such as AI frameworks. Our goal is to help organizations stay aware and protected by building more resilient systems.