Desktop Penetration Testing Report
This is a desktop application sample penetration testing report that documents the findings and summary of the test. It belongs to one of our former clients, whose identity has been kept secret to protect their privacy.
You can use a desktop application penetration testing report PDF for compliance, client demands, and internal security improvements. With our clear insights and user-friendly documentation, you can easily understand the content of the report. We aim to educate and inform organizations and individuals about the security risks of desktop applications and their effects.
Key Features of a Desktop App Penetration Testing Report:
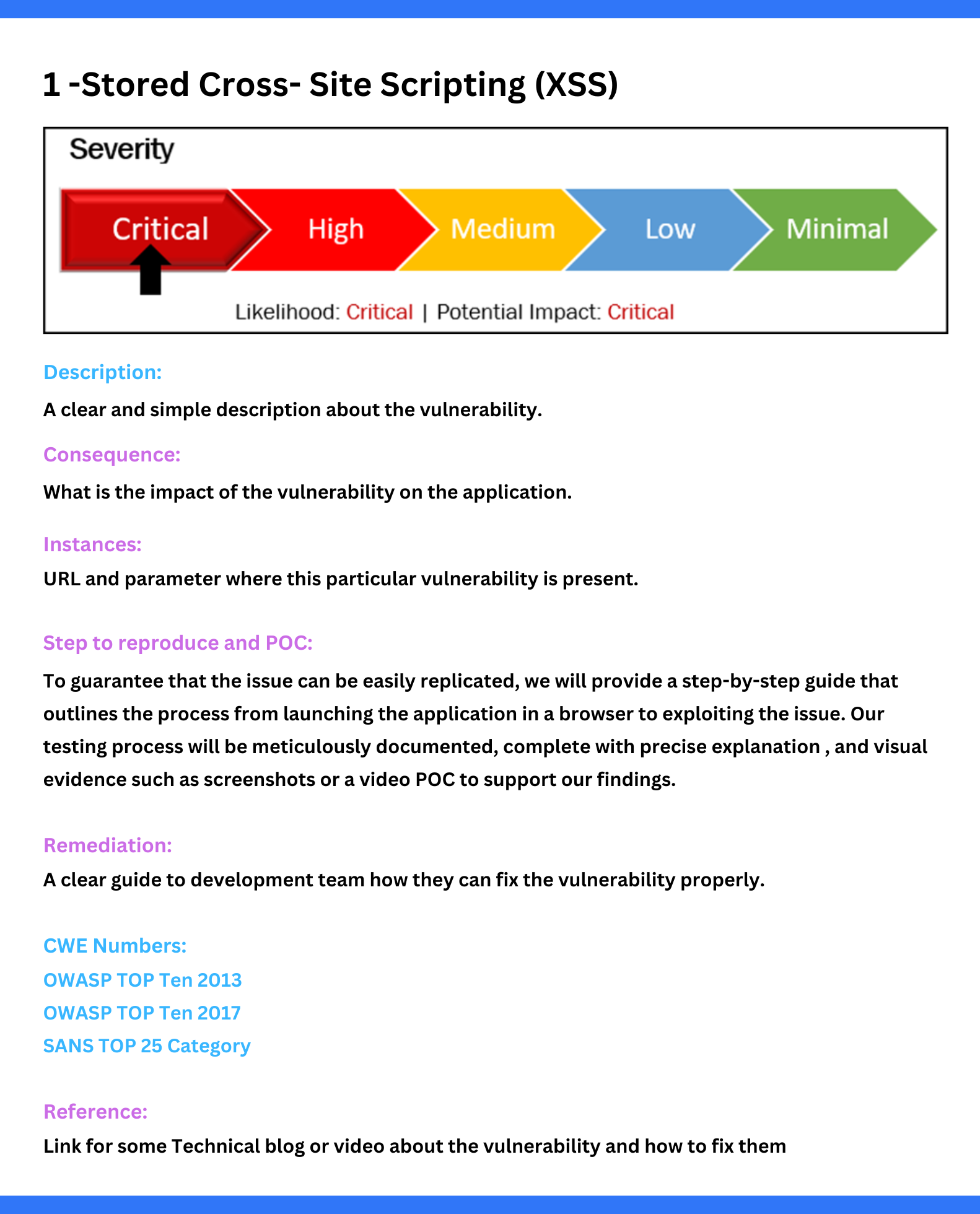
- Vulnerabilities found
- Vulnerabilities description
- Impact level of vulnerabilities
- POC (Probe of Concept)
- Remediation steps
How are Reports Looks like
Risk Assessment Methodology: NIST 800-30 Revision 1 Standard
We provide an executive summary that highlights the main points and provides the context to help you understand the overall security posture of your whole application.
Executive Summary
We provide an OWASP top 10 comparison table which helps you to gain insights on the top vulnerabilities found in your application.
OWASP Top 10 Comparison
From opening your app in a browser till we exploit the vulnerabilities, what steps we follow, and what scripts we put in, we write in very simple English with screenshots of each step.
Detailed and Step-by-Step Exploitation Process
We provide a proper remediation strategy that takes a methodical approach to fixing vulnerabilities. It requires prioritizing and carrying out corrective steps to decrease risk and improve security in a timely way.
Proper Remediation Plan
Apart from the list of vulnerabilities, we test and provide details about the open ports and outdated
components, such as technology, plug-ins, etc, to help you keep them up-to-date.

Talk to our Cybersecurity Expert to discuss your specific needs and how we can help your business.







