Automotive Device Penetration Testing
Protect your Automotive Device and applications from latest cyber security risks.
We Can Help You In
- Secure your hardware, firmware, radio/communication, and Dashboard.
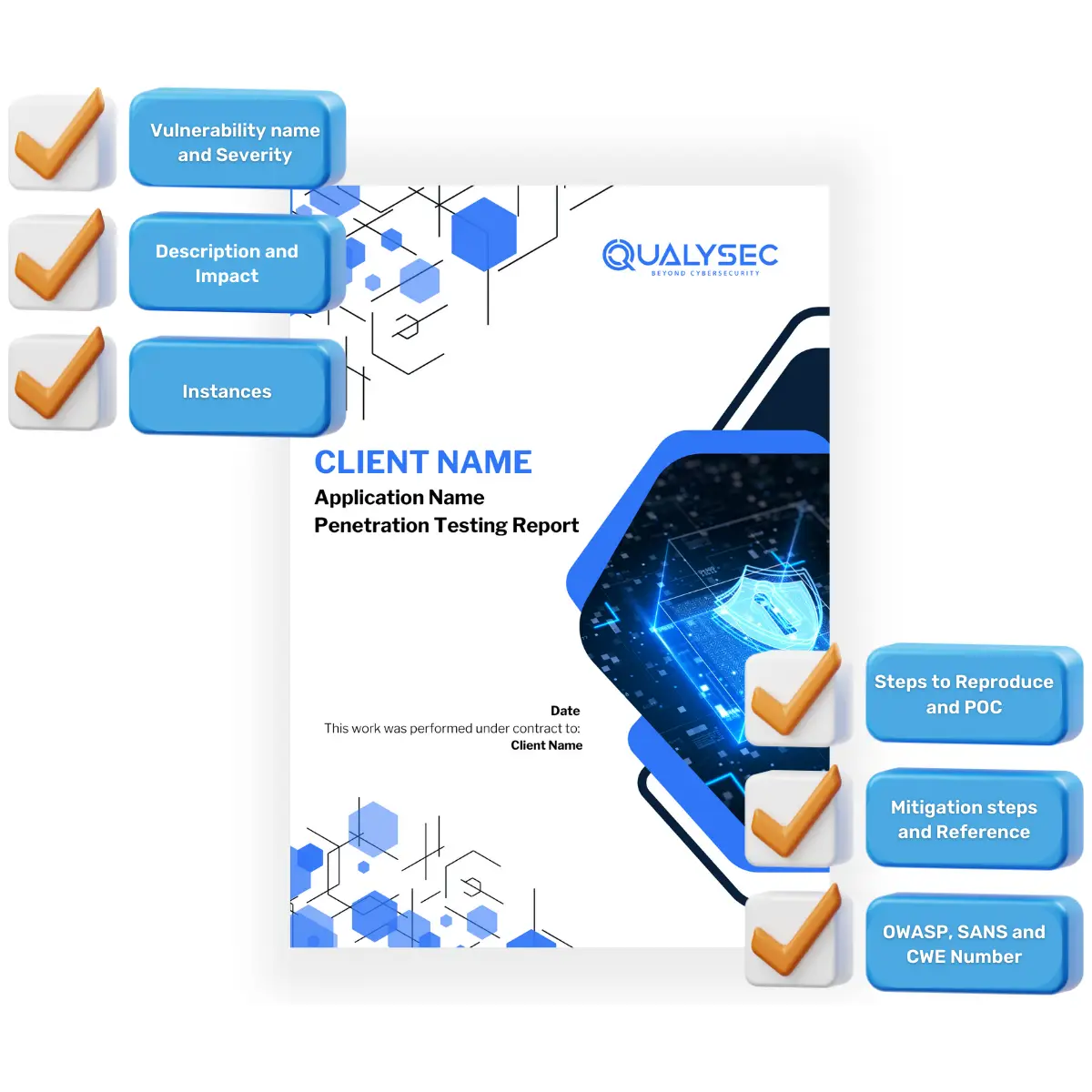
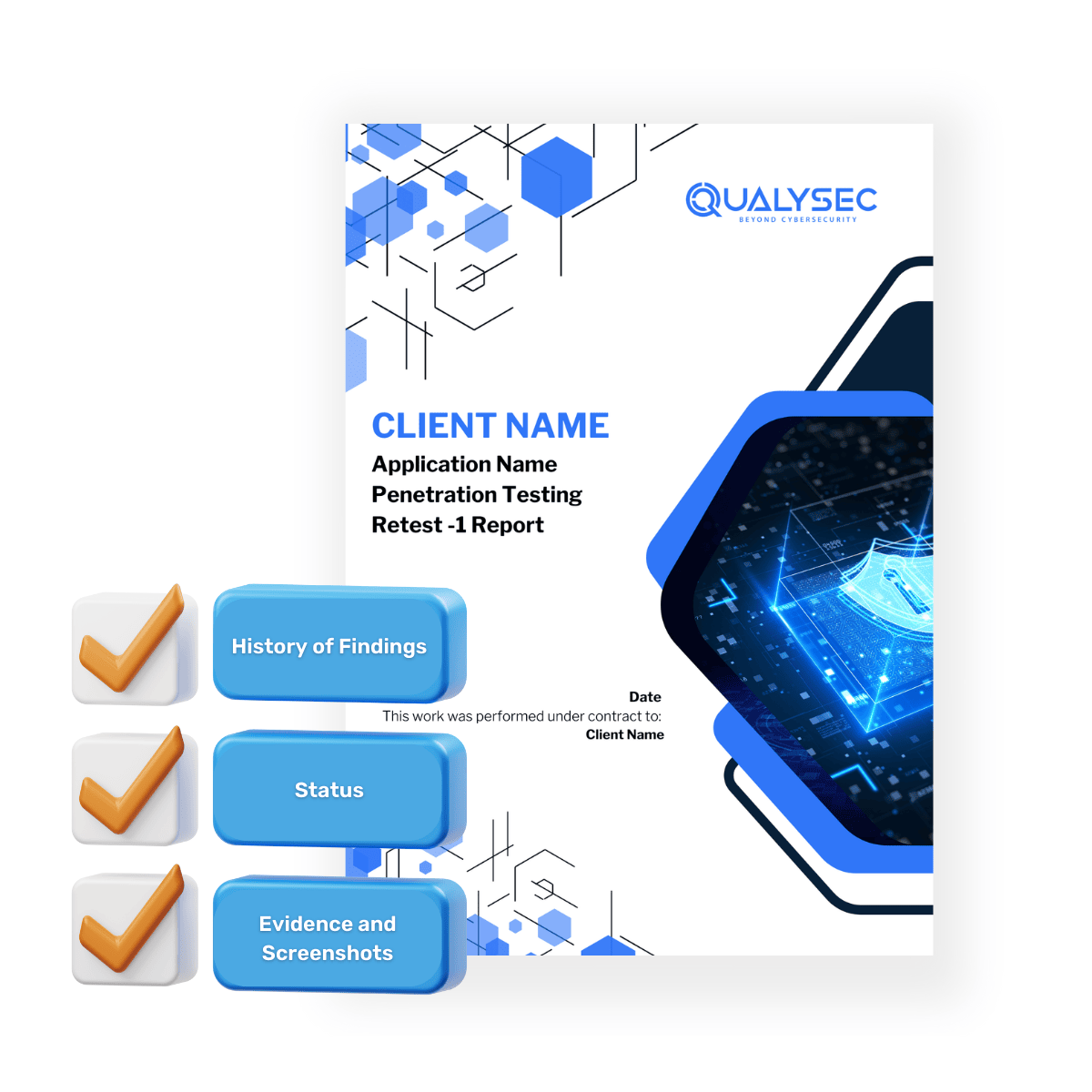
- Find and track vulnerabilities.
- Help you in fixing the vulnerability.
- Help you in standard and regulatory compliance.